New 0-day or feature from Microsoft?
It all started with the fact that on July 9, specialists of the Belarusian antivirus company VirusBlokada discovered an interesting malware program whose drivers had a legal digital signature from Realtek. The surprises did not end there, since this malware used a previously unknown vulnerability in processing LNK files (Shell Link) for unauthorized distribution from various USB drives. Seeing this informational message, we also drew attention to this threat, and noticed a rather interesting distribution landscape (the data was obtained through our ThreatSense.Net early detection system ).
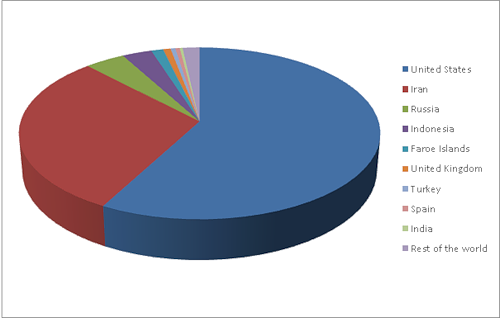
According to our statistics, it is clear that the United States is clearly the leader in the number of infections in the region. Further, with almost a twofold margin, comes Iran, followed by Russia.
In part, this distribution of data is confirmed by statistics from Microsoft, but it is possible that it deliberately omitted data for the United States, as an active investigation is currently underway regarding the appearance of this threat. MS only on Saturday July 16 released an MS Security Advisory , which officially confirmed the existence of this vulnerability. So, let's talk now about the technical details of this threat.
Distribution mode: 0-day or feature?
The only detected way to spread this malware is to infect USB drives. Interestingly, the malware launch method exploits a previously unknown vulnerability in processing LNK files contained on a USB drive. The execution of malicious code is due to a vulnerability in Windows Shell related to the display of specially prepared LNK files. This is what the contents of the infected drive look like:

It can be seen that there are two hidden files in the root directory that are installed during the system infection. The LNK files themselves contain the following:

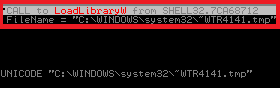
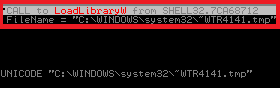
In the figure, the part that actually contains the data that allows
unauthorized execution of an executable file. When viewing the contents of a USB stick in Windows Explorer or any other file manager, LNK files are automatically loaded into memory. The vulnerability allows the execution of an arbitrary dynamic library, in our case it is ~ WTR4141.tmp.
All operating systems starting from Windows XP and including Windows 7 are vulnerable. We find LNK files exploiting this vulnerability as LNK / Autostart. Now let's talk about the malicious components that are installed on the system.
Win32 / Stuxnet
The most insidious and unexpected thing for the antivirus industry turned out to be that some components of this malware have a legitimate digital signature (at the moment this certificate has already been revoked) And even more interesting was the fact that the certificate was issued by Realtek.
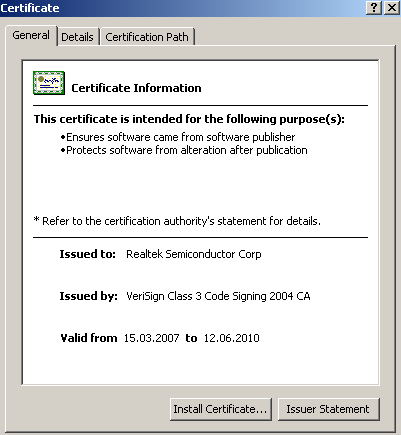
In particular, he signed that library, which runs in connection with the vulnerability of processing LNK files. Two drivers installed in the system also have signatures. All this makes it possible to bypass most HIPS systems, since the presence of a digital signature on many systems is considered a sign of a legal program.
During the analysis of this malicious program, no obvious methods of cybercriminal monetization were revealed. But they found the possibility of collecting information from SCADA systems, which are usually used in large industrial enterprises. And the hidden possibilities of network interaction give us every reason to believe that Win32 / Stuxnet is targeted for industrial espionage. While the investigation is ongoing, we were forbidden to disclose some details related to this malicious program, so we will limit ourselves to this information for now.
In the meantime, we recommend that you familiarize yourself with infection prevention information using this 0-day, published by an independent researcher Didier Stevens.
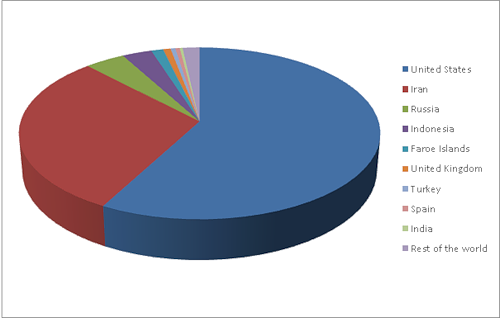
| United states | 57.71% |
| Iran | 30.00% |
| Russia | 4.09% |
| Indonesia | 3.04% |
| Faore islands | 1.22% |
| United kingdom | 0.77% |
| Turkey | 0.49% |
| Spain | 0.44% |
| India | 0.29% |
| Rest of the world | 1.73% |
According to our statistics, it is clear that the United States is clearly the leader in the number of infections in the region. Further, with almost a twofold margin, comes Iran, followed by Russia.
In part, this distribution of data is confirmed by statistics from Microsoft, but it is possible that it deliberately omitted data for the United States, as an active investigation is currently underway regarding the appearance of this threat. MS only on Saturday July 16 released an MS Security Advisory , which officially confirmed the existence of this vulnerability. So, let's talk now about the technical details of this threat.
Distribution mode: 0-day or feature?
The only detected way to spread this malware is to infect USB drives. Interestingly, the malware launch method exploits a previously unknown vulnerability in processing LNK files contained on a USB drive. The execution of malicious code is due to a vulnerability in Windows Shell related to the display of specially prepared LNK files. This is what the contents of the infected drive look like:

It can be seen that there are two hidden files in the root directory that are installed during the system infection. The LNK files themselves contain the following:

In the figure, the part that actually contains the data that allows
unauthorized execution of an executable file. When viewing the contents of a USB stick in Windows Explorer or any other file manager, LNK files are automatically loaded into memory. The vulnerability allows the execution of an arbitrary dynamic library, in our case it is ~ WTR4141.tmp.
All operating systems starting from Windows XP and including Windows 7 are vulnerable. We find LNK files exploiting this vulnerability as LNK / Autostart. Now let's talk about the malicious components that are installed on the system.
Win32 / Stuxnet
The most insidious and unexpected thing for the antivirus industry turned out to be that some components of this malware have a legitimate digital signature (at the moment this certificate has already been revoked) And even more interesting was the fact that the certificate was issued by Realtek.
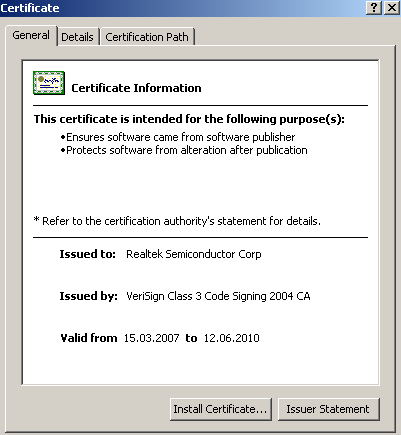
In particular, he signed that library, which runs in connection with the vulnerability of processing LNK files. Two drivers installed in the system also have signatures. All this makes it possible to bypass most HIPS systems, since the presence of a digital signature on many systems is considered a sign of a legal program.
During the analysis of this malicious program, no obvious methods of cybercriminal monetization were revealed. But they found the possibility of collecting information from SCADA systems, which are usually used in large industrial enterprises. And the hidden possibilities of network interaction give us every reason to believe that Win32 / Stuxnet is targeted for industrial espionage. While the investigation is ongoing, we were forbidden to disclose some details related to this malicious program, so we will limit ourselves to this information for now.
In the meantime, we recommend that you familiarize yourself with infection prevention information using this 0-day, published by an independent researcher Didier Stevens.
