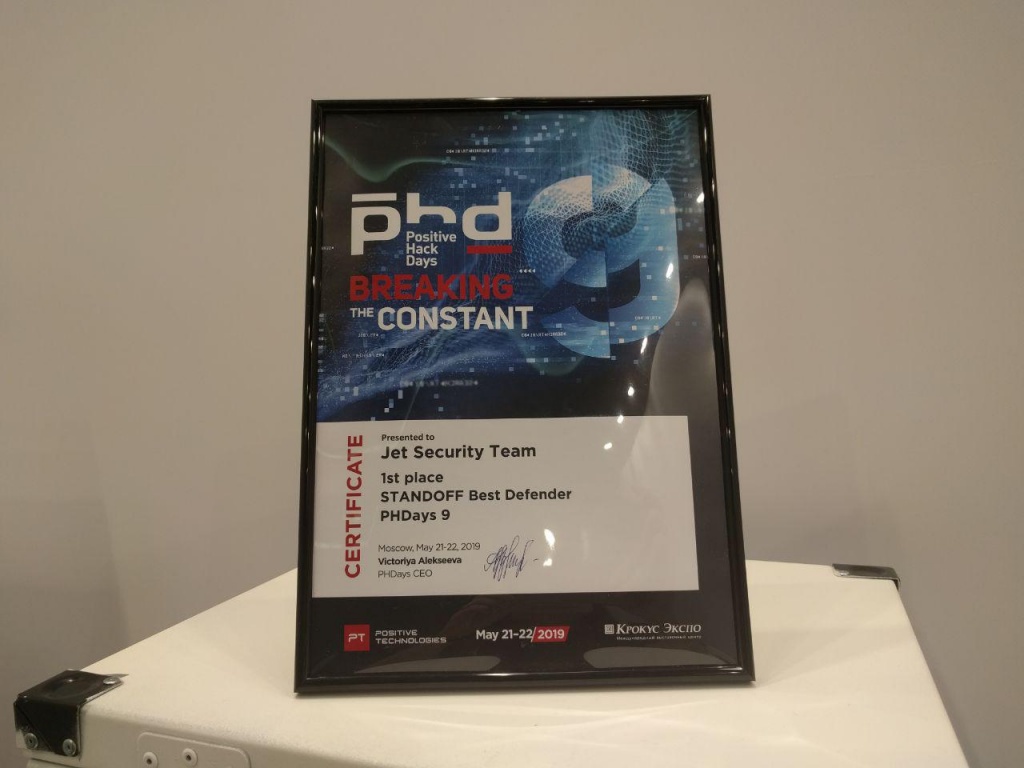
Confrontation 2019: Jet Security Team took first place in defense

For the third year in a row, the strongest Information Security experts at Jet Infosystems took part in The Standoff at PHDays. Our Jet Security Team and Jet Antifraud Team fought shoulder to shoulder: the cyber battle lasted non-stop for as long as 28 hours! According to the results of the “Confrontation”, our defenders became the best, not allowing the attackers to “crack” the whole city!
This year, “Confrontation” was quite large: 18 attacking teams (more than 250 people!), 5 classic defense teams, antifraud team and 3 SOC.
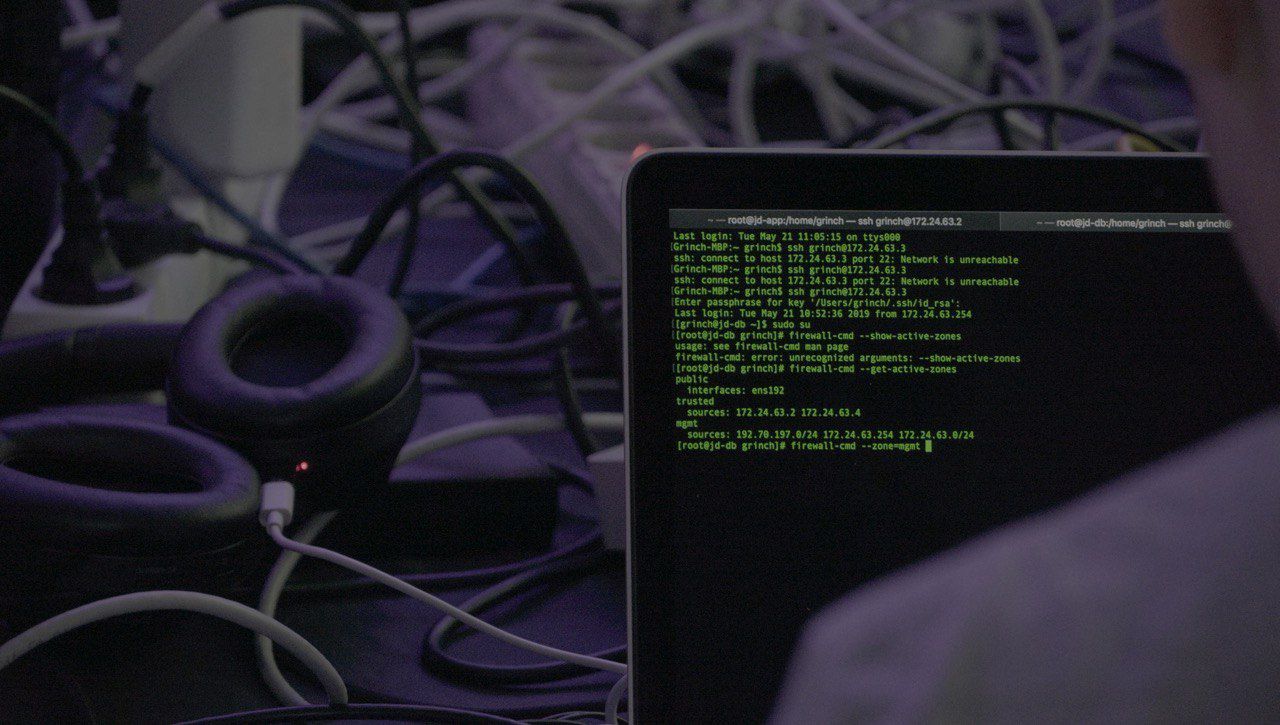
For 28 hours, the attackers attacked the virtual infrastructure (about which they will write in more detail on Habré). Both common exploits and 0-day infrastructure vulnerabilities were used. Defenders quickly identified attacks and patched vulnerabilities on the fly.
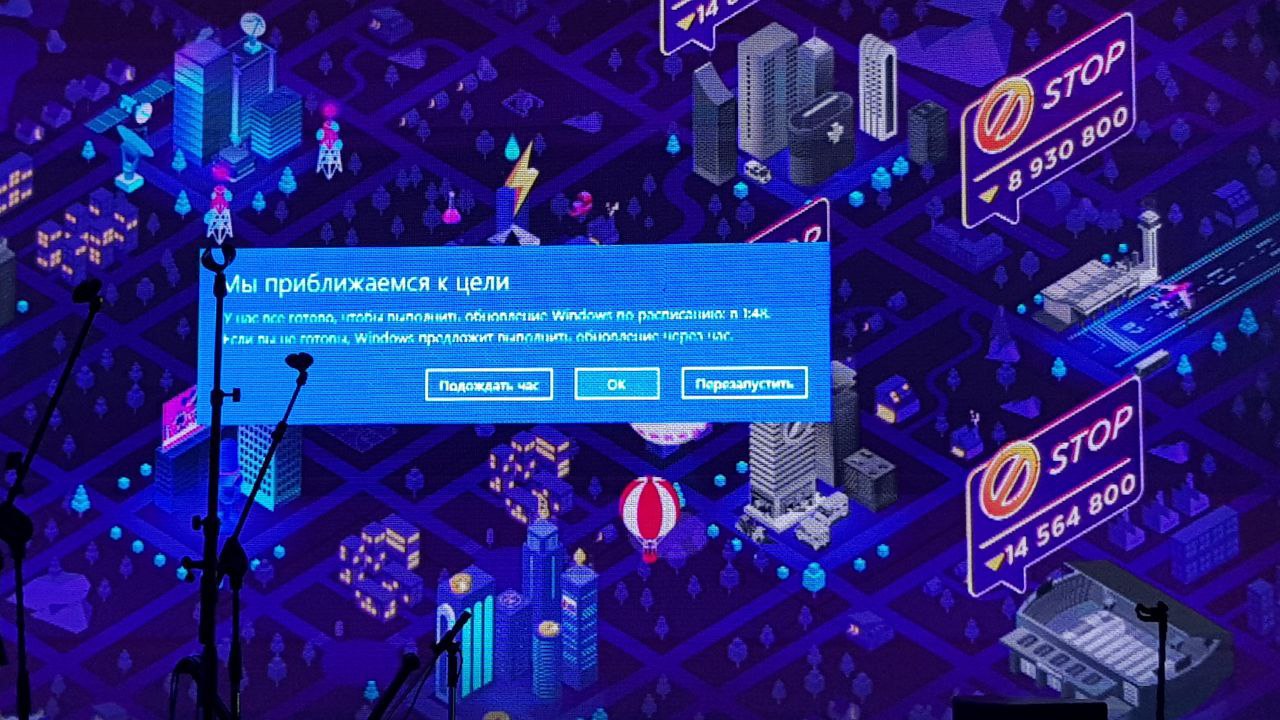
The attackers were not limited to this, using social engineering techniques to land behind the defenders:

The fight was very intense, any technical and analog means were used:

Despite this, the Jet Security Team and the Jet Antifraud Team adequately withstood the attacks, and hackers from the bank failed pick up a single “public” - units of virtual currency.
The Jet Security Team defeated the defending teams, stubbornly reflecting the attacker's many attempts to break into the infrastructure of the office of the shipping company entrusted to it. For the first time, the team consisted of specialists from the Jet CSIRT Information Security Monitoring and Response Center, who closely monitored each incident and timely blocked any threats.
For defenders, the format of the event has changed a bit. Previously, everyone had different objects of protection (telecom, office, automated process control system) and it was difficult to compare them directly, but now for all defense teams the organizers prepared almost the same infrastructure and introduced a single rating. This definitely added drive and spurred our team to victory.Ilya Sapunov, captain of the Jet Security Team.
For us, the object of protection has changed. If earlier it was an automated process control system, and the conditional “attack surface” was small, now we defended the office. There was Exchange with OWA, a VPN server, a terminal server exposed outside, a lot of web services, telephony, etc.
By tradition, organizers provide access to the object of protection at the end of April. This year access was granted on April 26th. Also, by tradition, a moratorium on the work of defenders is usually introduced about a week before the “Confrontation” itself. Accordingly, the protection team usually has a little more than 2 weeks to study the object, develop a protection strategy, deploy SZI, configure, debug, etc. Given the May holidays, pre-planned vacation of the team, this also added drive and stimulated us to win.
Under the terms of the competition, the Jet Antifraud Team was not rated among the classic defending teams due to the peculiarities of the anti-fraud decision. Colleagues outside the competition program once again showed the highest class of bank protection in virtual city F, without missing a single attack from attackers!
This year, attacks by attackers have become less active, but more thoughtful. Attackers stopped randomly sending a large number of operations, they selected passwords a lot, protected the stolen accounts, tried to disguise their operations as bank robots. However, this did not bring cumulative success, and they did not even try to withdraw money through other services, such as telecom.Alexey Sizov, captain of the Jet Antifraud Team.
The attackers had a hard time, but despite the complex vulnerabilities and opposition from the defense, they showed a decent result:
The day began when MassScan scans were given to us at 9.45. This marked the start of our work, we immediately wrote out all the hosts with an open 445 port and at exactly 10.00 we launched the ready-made metasplit checker for MS17-010. There was one vulnerable host in the bigbrogroup.phd network. In the first 10 minutes, we exploited the vulnerability, fixed it, fixed it in the system, and received an administrator-domain token. In this domain, as in all others below, the option of reversible encryption was enabled, which allowed to extract all passwords from ntds.dit and submit them for verification.Vitaly Malkin, head of security analysis at Informzashita, captain True0xA3 (winners from the attackers promised to write a detailed analysis of the competition, wait on Habré).
Further at 18.00 we got access to the CF-Media domain, exploiting the vulnerability in Nagios and climbing through the unquoted path in one of the sudo scripts. After that, using password reuse, we got a local administrator on one of the CF-Media domain computers. The further path of operation was similar to the first domain.
At night, we were able to understand the principle of operation of several automated process control systems, and this allowed us to take control of 2 skads and complete 2 tasks in the production segment. In particular, we turned off the outdoor lighting and arranged for oil spills from the oil storage. We also installed the miner on all the servers and workstations controlled by us; in total, our botnet stood at about 30-45 hosts. All this time, we simultaneously broke protected segments, but each time, as soon as we received RCE, the defenders simply dropped the service and did not pick it up anymore.
At 12.15, they announced the results of OSINT to us and handed out several domain accounts. Some defenders at this moment simply dropped OWA and VPN. Some tried to really protect their services. One of these companies was behealty, whose advocates allowed us to connect via VPN and operate the MS17-010. And to our surprise, the domain again had reversible encryption. The result - another +1.1 million public and a confident victory in the competition.
I want to note on my own that the struggle was serious, literally until the last hours the intrigue persisted - the CARK and SNIFF & WATCH teams did not let the winners relax, and any trifle or “Joker” in the sleeve could affect the result.
It was an epic battle, and I am glad for the well-deserved victory of my colleagues.