19% of the most popular Docker images do not have a root password
Last Saturday, May 18, Kenna Security's Jerry Gamblin checked the 1000 most popular images from the Docker Hub for the root password used in them. In 19% of cases, he was absent.
The reason for the mini-study was Talos Vulnerability Report ( TALOS-2019-0782 ), which appeared earlier this month , whose authors - thanks to the find of Peter Adkins from Cisco Umbrella - reported that Docker images with the popular distribution kit for containers Alpine do not have a password for root:
Alpine versions of Docker images tested for the problem were called 3.3–3.9 inclusive, as well as the latest edge release.
The authors made the following recommendation to users affected by the problem:
The problem was fixed in Alpine versions 3.6.5, 3.7.3, 3.8.4, 3.9.2 and edge (20190228 snapshot), and the owners of the images affected by it were offered to comment out the line with root in
Jerry Gamblin decided to inquire, "how widespread it may turn out to be the practice of using null passwords in containers." To do this, he wrote a small Bash script , the essence of which is very simple:
What happened? In this file it turned 194 lines with the names of popular Docker-images with the Linux-system, root-user that has no password set:
However, it is worth recalling that this phenomenon in itself does not mean a direct vulnerability in the security of the systems that use them: it all depends on how they are used (see the comment from the Alpine case above) . However, we have already seen “the morality of this fable” many times: the apparent simplicity often has a downside, which must always be remembered and the consequences of which should be taken into account in your technology application scenarios.
Read also in our blog:
Background with Alpine
The reason for the mini-study was Talos Vulnerability Report ( TALOS-2019-0782 ), which appeared earlier this month , whose authors - thanks to the find of Peter Adkins from Cisco Umbrella - reported that Docker images with the popular distribution kit for containers Alpine do not have a password for root:
“The official versions of Alpine Linux Docker images (starting with v3.3) contain a NULL password for the root user. This vulnerability appeared as a result of a regression introduced in December 2015. Its essence is that systems deployed with problematic versions of Alpine Linux in a container and using Linux PAM or another mechanism that uses the shadow system file as an authentication database can accept a NULL password for the root user. ”
Alpine versions of Docker images tested for the problem were called 3.3–3.9 inclusive, as well as the latest edge release.
The authors made the following recommendation to users affected by the problem:
“The root account must be explicitly disabled in Docker images built on the basis of problematic versions of Alpine. The likely exploitation of the vulnerability depends on the environment, since its success requires a service or application that has been forwarded outside, using Linux PAM or another similar mechanism. ”
The problem was fixed in Alpine versions 3.6.5, 3.7.3, 3.8.4, 3.9.2 and edge (20190228 snapshot), and the owners of the images affected by it were offered to comment out the line with root in
/etc/shadowor to make sure the package was missing linux-pam.Continued with the Docker Hub
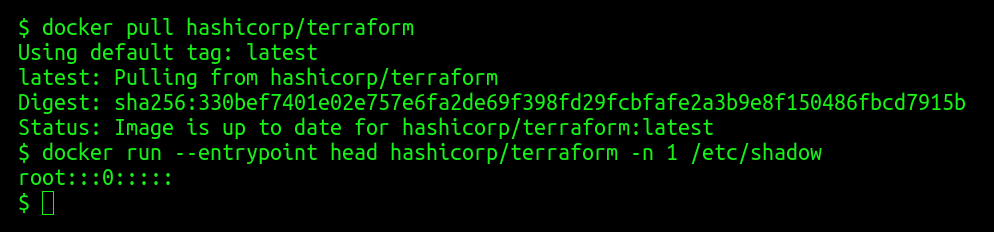
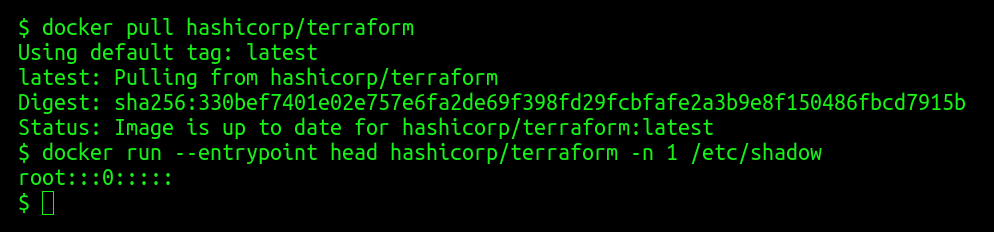
Jerry Gamblin decided to inquire, "how widespread it may turn out to be the practice of using null passwords in containers." To do this, he wrote a small Bash script , the essence of which is very simple:
- through a curl request to the API in the Docker Hub, a list of Docker images hosted there is requested;
- through jq it is sorted by field
popularity, and the first thousand remains of the results obtained; - for each of them is performed
docker pull; - for each image received from the Docker Hub, it
docker runreads the first line from the file/etc/shadow; - if the string value is equal
root:::0:::::, the image name is saved in a separate file.
What happened? In this file it turned 194 lines with the names of popular Docker-images with the Linux-system, root-user that has no password set:
“Among the most famous names on this list were govuk / governmentpaas, hashicorp, microsoft, monsanto and mesosphere. And kylemanna / openvpn is the most popular container from the list, its statistics totals more than 10 million pulls. "
However, it is worth recalling that this phenomenon in itself does not mean a direct vulnerability in the security of the systems that use them: it all depends on how they are used (see the comment from the Alpine case above) . However, we have already seen “the morality of this fable” many times: the apparent simplicity often has a downside, which must always be remembered and the consequences of which should be taken into account in your technology application scenarios.
PS
Read also in our blog:
