The history of the fight against censorship: how the flash proxy method created by scientists from MIT and Stanford works
In the early 2010s, a joint team of specialists from Stanford University, the University of Massachusetts, The Tor Project and SRI International presented the results of their research on how to deal with censorship on the Internet.
Scientists analyzed the methods of bypassing the locks that existed at that time and proposed their own method, called flash proxy. Today we will talk about its essence and development history.
Introduction
The Internet began as a network open to any type of data, but over time, many countries began filtering traffic. Some states block certain sites, such as YouTube or Facebook, while others block access to content that contains certain materials. In one form or another, locks are used in dozens of countries from different regions, including Europe.
Users in regions where locks are used try to bypass them using various proxies. There are several directions for the development of such systems, one of the technologies - Tor, was used during the project.
Typically, developers have proxies to bypass locks with three tasks that need to be addressed:
- Rendezvous protocols. The rendezvous protocol allows users in a country with locks to send and receive small amounts of information to establish a connection with a proxy - in the case of Tor, for example, it uses rendezvous to distribute the IP address of Tor relays (bridges). Such protocols are used for low-rate traffic and blocking them is not so simple.
- Creating a proxy. Blocking systems need proxies outside the region with filtered Internet in order to transfer traffic from the client to the target resources and vice versa. Blocking organizers may, in response, prevent users from recognizing the IP addresses of proxies and blocking them. To counter such a Sibyl attack, a proxy service must be able to constantly create new proxies. It is the rapid creation of new proxies that is the main essence of the method proposed by the researchers.
- Camouflage. When a client receives the address of an unblocked proxy, he needs to hide his communication with him in some way so that the session cannot be blocked using traffic analysis tools. It needs to be camouflaged for “normal” traffic, such as exchanging data with an online store, online games, etc.
In their work, scientists proposed a new approach to the rapid creation of proxies.
How it works
The key idea is to use many websites to create a huge amount of proxies with a short lifespan of no more than a few minutes.
To do this, create a network of small sites owned by volunteers - such as users' home pages, living outside the region with Internet locks. These sites are in no way associated with the resources that the user wants to access.
A small badge is installed on such a site, which is a simple interface created using JavaScript. An example of such a code:
This is what the badge looks like:
When a browser from a location outside a region with locks gets to such a site with a badge, it starts transmitting traffic to this region and back. That is, the visitor’s browser becomes a temporary proxy. After this user leaves the site, the proxy is destroyed without any traces.
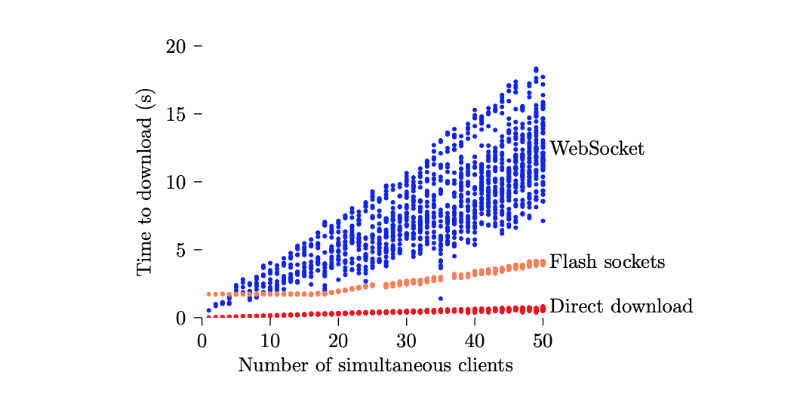
As a result, it is possible to obtain sufficient performance to maintain the Tor tunnel.
In addition to Tor Relay and the client, the user will need three more elements. The so-called facilitator, which receives requests from the client and connects it to the proxy. Communication takes place using transport plug-ins on the client (here is the version for Chrome ) and Tor-relay switches from WebSockets to pure TCP.

A typical session using this scheme looks like this:
- The client launches Tor, the flash-proxy client (browser plug-in), and sends the registration request to the facilitator using the rendezvous protocol. The plugin starts listening to the remote connection.
- A flash proxy appears online and contacts the facilitator with a request to connect to the client.
- The facilitator returns the registration by passing flash proxy data for the connection.
- The proxy connects to the client whose data was sent to it.
- The proxy connects to the transport plugin and Tor-relays and begins the exchange of data between the client and the relay.
The peculiarity of this architecture is that the client never knows in advance exactly where he will need to connect. In fact, the transport plugin accepts the fake destination address only so as not to violate the requirements of the transport protocols. Then this address is ignored and a tunnel is created to another endpoint - the Tor relay.
Conclusion
The flash proxy project has been developing for several years and in 2017, the creators stopped supporting it. The project code is available at this link . The flash proxy has been replaced by new lock bypass tools. One of them is the Snowflake project, built on similar principles.
