12. Check Point Getting Started R80.20. Logs & reports
- Tutorial
Welcome to the 12th lesson. Today we’ll talk about another very important topic, namely working with logs and reports . Sometimes this functionality is almost decisive when choosing a means of protection. Security guards really like a convenient reporting system and a functional search for various events. It's hard to blame them. In fact, logs and reports are an essential element in assessing security. How to understand the current level of security if you do not see what is happening? Fortunately, Check Point has everything in that order and even more. Check Point has one of the best reporting systems that works out of the box! At the same time, there is the possibility of customization and creating your own reports! All this is complemented by a convenient and intuitive process of working with logs. But let's talk about everything in order.
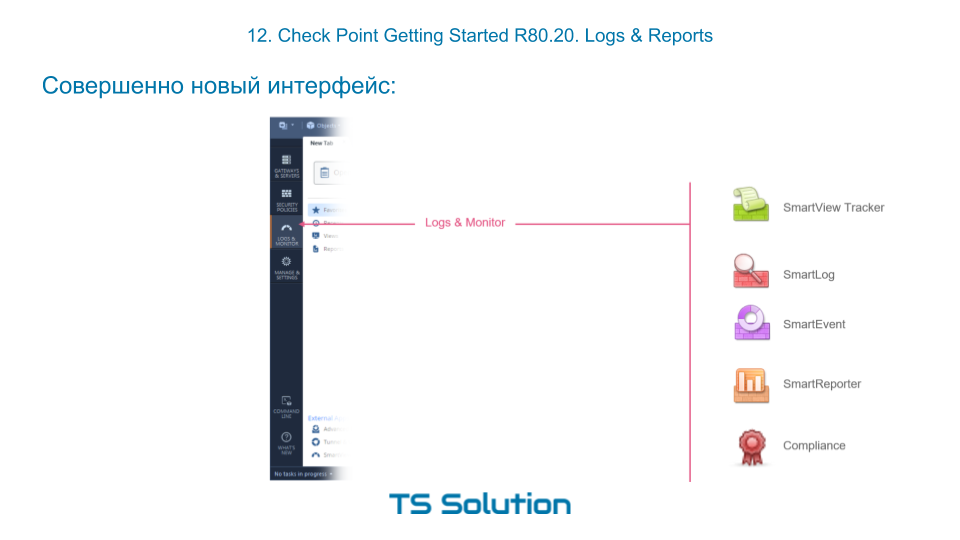
Brand new interface
If you worked with Check Point before, then you were probably surprised by the completely new interface for working with logs and reports in R80. The picture shows how many different utilities are combined in one new tab Logs & Monitor :
Logs & Monitor Section
If you go to Logs & Monitor and open a new tab, then you should see something like the following:

By default, there are two large sections:
- Audit Logs View - here you can find all the events related to the entrance / exit of administrators, changes in configuration, etc. Those. classic audit of administrator actions.
- Logs View - this is where you can search for events that “generate” all of our included blades, be it firewall, antivirus, IPS, etc. We have used this feature more than once.
In addition, there are links to reports ( Reports ) and various dashboards ( Views ). For their operation, the included Smart Event blade is required . But more on that later. First, let's figure out how to work with logs.
Log Search
In my opinion, working with logs in the R80 is a pleasure. We have a very clever search string, which allows us to “cut” by arbitrary text, by blade, and by any other indexed parameters such as source, destination, action, etc.
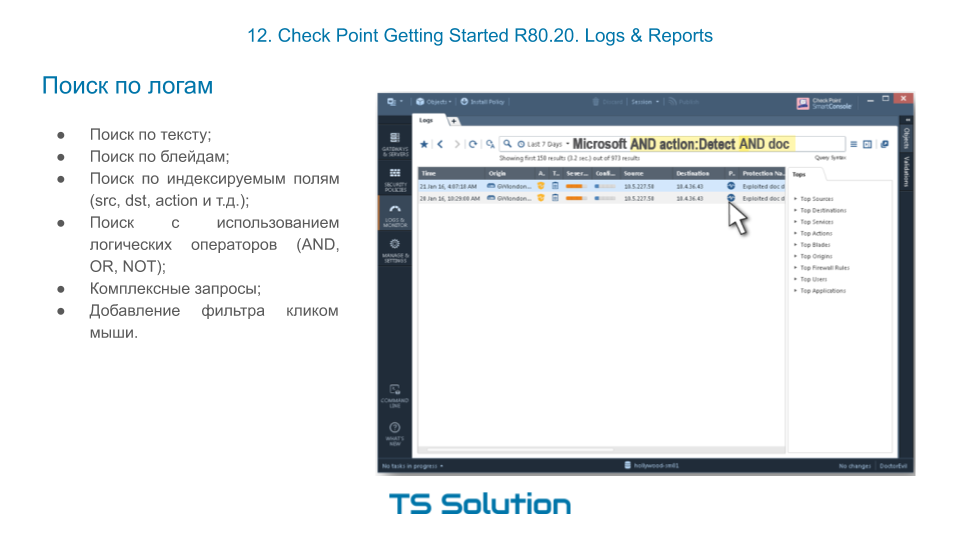
At the same time, we can compose very complex search queries using the logical operators AND , OR , NOT . And for this, it is not even necessary to print anything. A filter can be created in just a couple of mouse clicks. Later we will try it all in practice.
Display Log Messages by Access-List
We have also appreciated the ability to display logs for a specific access list. It is insanely convenient and you get used to it very quickly. This especially helps with Troubleshoot. I highlighted the “access list” that is interesting to you and look from below whether the necessary traffic falls under it.
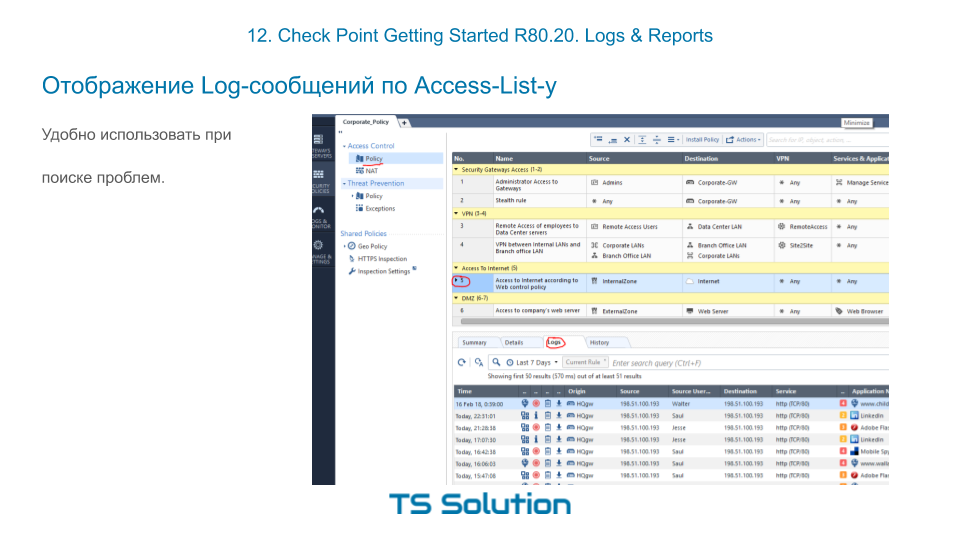
No need to go anywhere or make up a sophisticated filter for logs.
Views & Reports
For reporting and data visualization in Check Point, the Smart Event blade is responsible , which is activated on the management server. This functionality can be safely called SIEM, but only for Check Point products! Technically, on Smart Event, you can wrap logs from other systems (such as cisco, microsoft, etc.), but this is not a good idea :) In practice, this is very problematic. But SmartEvent does just fine with the checkpoint logs. It can correlate, summarize, average and much more. And it all works out of the box! Of course, there are ready-made dashboards for displaying the most important information. In Check Point, they are called Views :

You can see that there is a fairly large number of default dashboards, which are very useful in daily administration and monitoring.
In addition to dashboards, where the information is simply visualized, it is possible to generate complete reports and save them in pdf or excel format. You can generate on a schedule and send them to some mailbox.
And the best part! You can create dashboards and reports yourself! Those. You are not limited to built-in. Not every vendor can boast of this. At the same time, templates for these dashboards or reports can be imported or exported, which allows users to share their best practices. The process of creating a dashboard is very simple and intuitive. I will try to show you this as part of the laboratory work, which you will find in the video tutorial below.
Video lesson
Stay tuned for more and join our YouTube channel :)
