Data leakage (which may have occurred but did not occur) from the telemedicine company
Just a couple of days ago, I wrote on Habrir about how the Russian medical online service DOC + managed to leave in the public domain a database with detailed access logs, from which it was possible to obtain data from patients and service employees. And here is a new incident, with another Russian service providing patients with online consultations with doctors - “Doctor is nearby” (www.drclinics.ru).
I will write right away that due to the adequacy of the Doctor Near employees, the vulnerability was quickly (2 hours from the moment of notification at night!) Eliminated and most likely there was no leakage of personal and medical data. In contrast to the incident with DOC +, where I know for sure that at least one json file with data of 3.5 GB size fell into the “open world”, while the official position looks like this: “ A small amount of data has been temporarily made publicly available, which cannot lead to negative consequences for employees and users of the DOC + service. ".

An anonymous subscriber contacted me as the owner of the Telegram channel " Information Leaks " and reported a potential vulnerability on the site www.drclinics.ru.
The essence of the vulnerability was that, knowing the URL and being in the system under your account, you could view the data of other patients.
To register a new account in the Doctor Near system, in fact, you only need a mobile phone number to which you receive a confirmation SMS, so no one could have had problems accessing your personal account.
After the user entered his personal account, he could immediately, changing the URL in the address bar of his browser, view reports containing personal data of patients and even medical diagnoses.
A significant problem was that the service uses end-to-end numbering of reports and already generates URLs from these numbers:
https://[адрес сайта]/…/…/40261/…
Therefore, it was enough to set the minimum acceptable number (7911) and maximum (42926 - at the time of the vulnerability) in order to calculate the total number (35015) of reports in the system and even (if there was malicious intent) to download them all with a simple script.

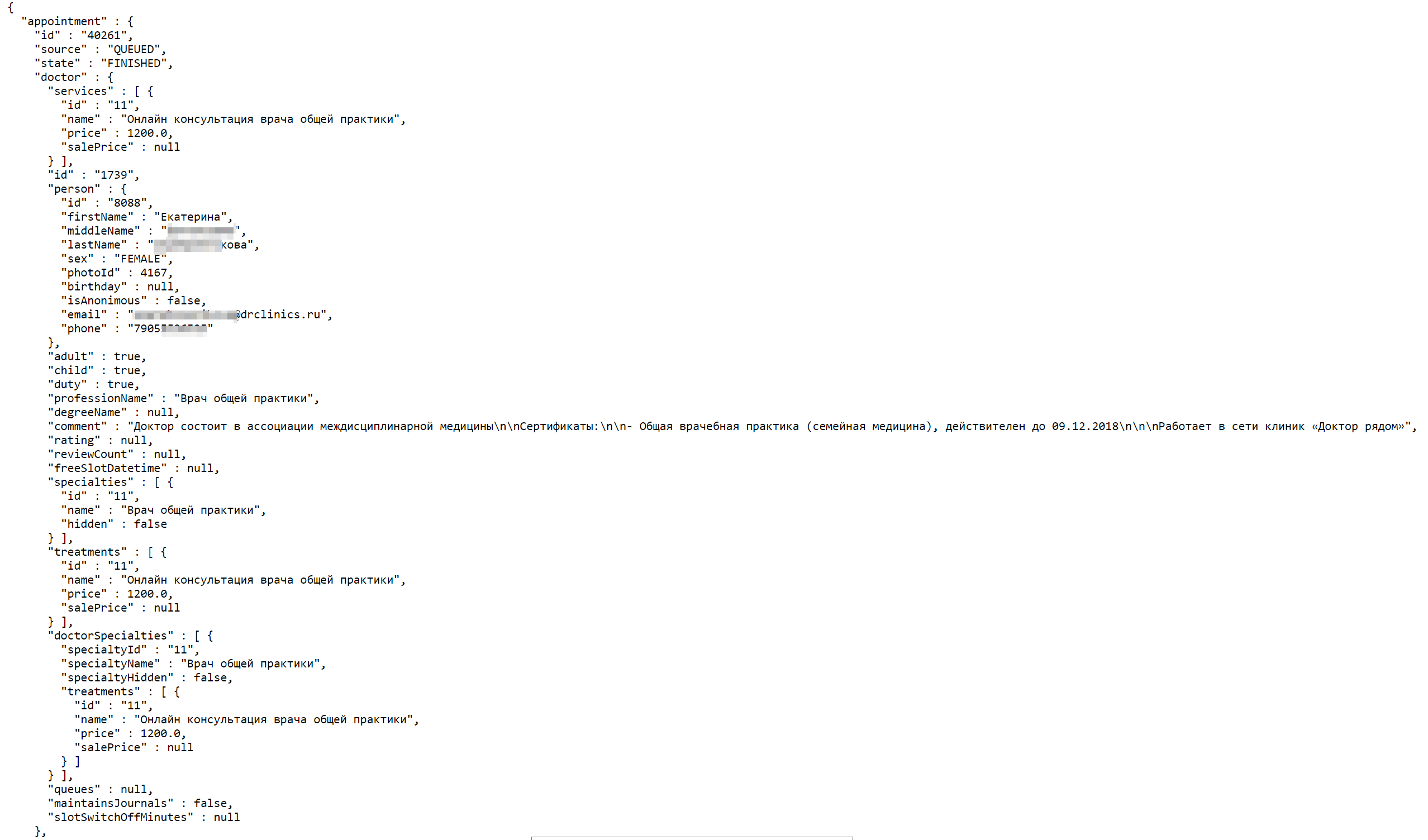
Among the data available for viewing were: name of the doctor and patient, dates of birth of the doctor and patient, phone numbers of the doctor and patient, gender of the doctor and patient, email addresses of the doctor and patient, specialization of the doctor, date of consultation, cost of consultation, and in some cases even a diagnosis ( as a comment to the report).
This vulnerability is essentially very similar to the one that was discovered in December 2017 on the server of the microfinance organization Zaimograd. Then the search could get 36763 contracts containing the full passport data of the organization’s clients.
As I pointed out from the very beginning, the Doctor Near employees showed real professionalism and despite the fact that I informed them of the vulnerability at 23:00 (Moscow time), access to my personal account was immediately closed to everyone, and by 1:00 ( Msk) this vulnerability has been fixed.
I can’t help but kick again the PR department of the same DOC + (New Medicine LLC). Declaring " an insignificant amount of data has temporarily turned out to be in the public domain ", they lose sight of the fact that we have at our disposal the data of "objective control", namely the Shodan search engine. As correctly noted in the comments to that article, according to Shodan, the date of the first commit of the open ClickHouse server at the DOC + IP address: 02.15.2019 03:08:00, date of the last commit: 03/17/2019 09:52:00. The database size is about 40 GB.
And there were 15 fixations in total:
15.02.2019 03:08:00
16.02.2019 07:29:00
24.02.2019 02:03:00
24.02.2019 02:50:00
25.02.2019 20:39:00
27.02.2019 07:37:00
02.03.2019 14:08:00
06.03.2019 22:30:00
08.03.2019 00:23:00
08.03.2019 14:07:00
09.03.2019 05:27:00
09.03.2019 22:08:00
13.03.2019 03:58:00
15.03.2019 08:45:00
17.03.2019 09:52:00From the statement, it turns out that temporarily it's a little over a month, and a small amount of data is about 40 gigabytes. Well I do not know...
But back to the "Doctor is nearby."
At the moment, my professional paranoia is haunted by only one remaining minor problem - by the response of the server you can find out the number of reports in the system. When you try to get a report by a URL that you don’t have access to (but the report itself is there), the server returns ACCESS_DENIED , and when you try to get a report that isn’t there, NOT_FOUND is returned . By monitoring the increase in the number of reports in the system in dynamics (once a week, month, etc.), you can evaluate the load of the service and the volume of services provided. This of course does not violate the personal data of patients and doctors, but it can be a violation of the trade secrets of the company.
