Synchronize Wi-Fi access points for collaboration
This story is worth starting with one interesting story ...
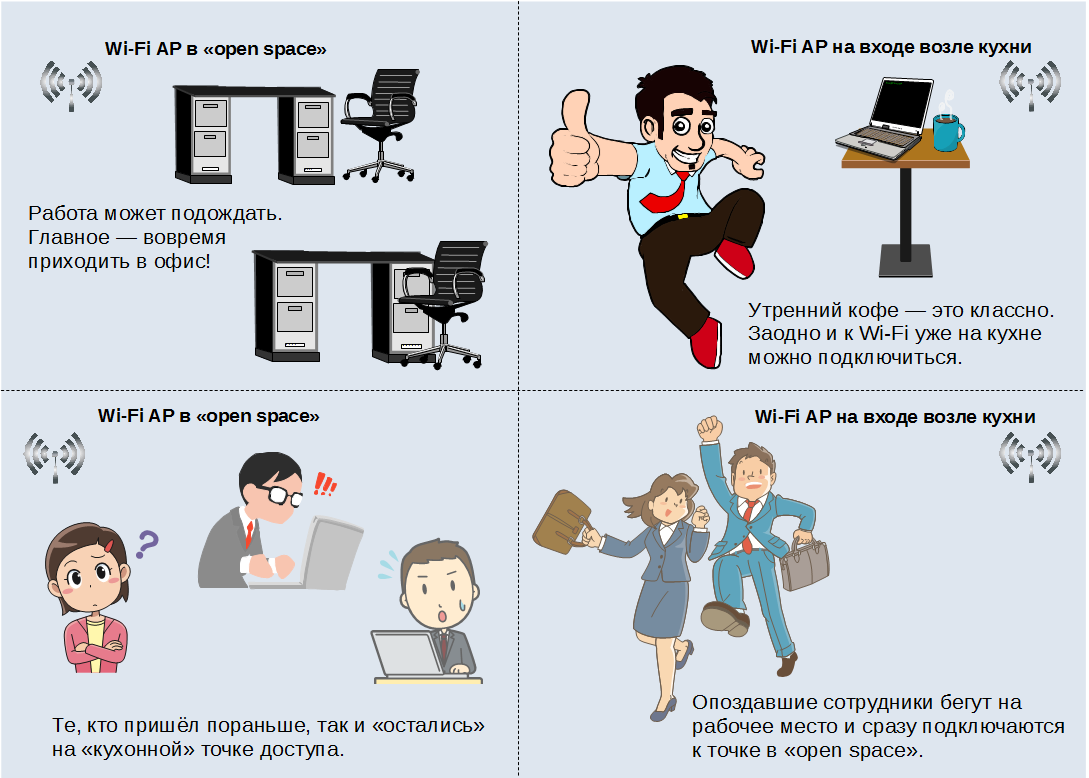
A certain small company had a very small office consisting of a corridor, a kitchen with a coffee machine, a meeting room, a director’s office and an open work space.
Employees received corporate laptops as a working computer. And the strange fact was noticed that people who came to work on time had interruptions in communication, and those who were late did not notice such problems. Just some kind of mysticism.
Of course, lovers of being late would gladly tease their more disciplined colleagues. It came to an absurdity, when some employees began to specifically linger in order to have better communication.
It turned out, everything is simple. The office had only two autonomous access points. One was at the entrance right near the kitchen, the second was in the middle of open space. Employees who arrived on time first went to the kitchen to drink coffee and talk on various topics, and so that the bosses wouldn’t scream once again, they would also immediately turn on their laptops, thereby demonstrating a working attitude. And the latecomers immediately ran to the workplace.
It turned out that those who arrived on time connected to the “kitchen” access point, and then moved away from their signal source for a considerable distance.
And those who were late to the kitchen did not enter and were connected in the open space to a point that was much closer and less loaded compared to the “kitchen”. So you and "bonus slobs".
To avoid such situations and to ensure high-quality uninterrupted communication, the seamless roaming technology is intended.
About terminology
In theory, the title of the article should have something like “Zyxel solutions for seamless roaming”. But the fact is that roaming in the Wi-Fi environment and roaming, for example, for GSM are different concepts.
If we are talking about cellular communication, the beautiful word "roaming" indicates the ability to receive and transmit data in the "alien" network, but not the ability to reconnect between stations without losing communication and imperceptibly to the user.
When applied to Wi-Fi, the term “roaming” is used in a different sense. From English “roaming”, “roam” can be translated as “roam”, “wander”. In theory, a client that “roams” between several Wi-Fi access points requires roaming.
Note. Some sources also mention the term “handover,” literally meaning “transfer of authority.” It is assumed that when a client moves from one access point to another, the necessary information is transmitted for authentication and maintenance of the consumer device.
Sometimes the word “seamless” introduces additional confusion. For each case, this concept is perceived in its own way. Therefore, we’ll focus on the following definition: Seamless roaming allows customers to work without interrupting their core business. ”
Simply put, we will consider “seamless” the option of roaming, which “helps us to build and live,” and not when it is required to constantly be distracted and perform some actions.
About standards
Fortunately or unfortunately, this direction has been developing from the point of view of modern technologies for a long time. Accordingly, several standard protocols managed to appear, one way or another designed to help in ensuring seamless roaming
802.11k - it helps to quickly locate neighboring access points.
Allows the client to quickly switch between the points found.
The first time you connect to an access point, the client, which itself supports 802.11k, receives information on the compliance of a point with this protocol.
If 802.11k is mutually supported, then the client sends a request to the selected point to obtain a list of neighboring access points. When the signal is weakened, the client will search for other access points from this list. Since it scans only the desired channels, the search is much faster. After migration, the client again requests the updated list of neighboring access points.
Using an optimized list greatly reduces the scanning time of the radio.
If the client were scanning the entire range, this would lead to long delays and disconnection.
802.11v - Wireless Network Management (WNM)
IEEE 802.11v is an amendment to the IEEE 802.11 standard that makes it possible to reconfigure client devices when connected to wireless networks.
802.11v was published as 802.11v-2011 in 2011, after being included in 802.11-2012 in 2012.
The main goal of this standard is to get efficient control of Wi-Fi data transfer media. The protocol resolves the issue of data exchange on the environment between stations, roaming and balancing.
Often consider the joint application of the above standards, which is designated as 802.11k / v. Such a combination of efforts brings successful results, for example, when organizing home networks and networks for small offices. Also, the use of the 802.11k / v protocol bundle is recommended when there are a large number of legacy devices that do not support the later 802.11r standard.
Where a more rigorous approach to communication is required, the use of
the 802.11r protocol is recommended.
802.11r- alternative name - FT (Fast Transition). The protocol allows the implementation of encryption key storage technology for access points.
Setting parameters is made by the user. Of course, it makes no sense to remind you that all the identifiers and keys of the mobile domain on all Internet centers of the local network segment should be the same.
Note . When using FT mode to maintain voice communication, for example, SIP telephony, there may be slight pauses when switching between points, this does not lead to disconnection.
When using 802.11r, if the client transitions to a new point, you do not need to re-perform the encryption key negotiation.
There are two types of Fast Transition: the newer - Over the Air (OTA) and the more deserved - Over the DS (OTD).
OTA literally means "by air." The client interacts with the access point to which he wants to connect before starting the migration via radio.
OTD - a client to communicate with the "new" access point for reconnection communicates through the point to which it is connected at the current time.
This option, which was designed for the 802.11r protocol at the very beginning.
Accordingly, older devices "can work" only through Over the DS.
If both functions are supported and enabled: Over the DS and Over the Air, the client chooses which function to use. More modern models of smartphones support Over the Air and this mode is more often chosen for roaming.
Important! The moment for reconnection is chosen by the client device. Specific criteria are set by its manufacturer. The standard "gentleman's set" traditionally includes: low level of RSSI, workload of the access point, low data transfer rate, other parameters can be used.
Solutions for every occasion
Different companies, different conditions require different solutions. And it can be not only in terms of volume, but also in the budget, the level of personnel training, and so on.
Zyxel offers two solutions: an express solution for small companies and specialized for larger organizations or for cases when reliable access to Wi-Fi is important enough for a business.
The express solution is that the USG Internet gateways support the 802.11r protocol, which is called out of the box.
Firewalls support only 802.11r (and older methods like OKC), as well as proprietary Load Balancing and RSSI Threshold algorithms, which can disable clients or prevent them from connecting, depending on the signal level or the load on the points.
For example, USG 40 / 40W / 60 / 60W gateways can manage from 2 access points immediately after installation and up to 18 points after purchasing additional licenses.

Figure 1. Universal Firewall USG60W - not only network protection, but also seamless roaming for a small organization.
For the USG 1100/1900 gateways, these numbers will be 2 and 130, respectively.
Thus, if you already have a USG gateway, then in principle, it is possible to organize Wi-Fi roaming.

Figure 2. The powerful USG 1900 firewall - with control of up to 130 Wi-Fi access points.
This option is well suited for small organizations in the making (“start-ups”). When the company was born not so long ago, equipment is purchased for users' work (laptops, corporate smartphones), which was released relatively recently, so the modern 802.11r protocol will fit perfectly.
The USG series was originally conceived as a universal solution for small networks, allowing you to immediately close a lot of issues: from anti-virus protection, VPN connection and right up to Wi-Fi control.
If you need to create larger wireless networks, there is an appropriate solution based on specialized NXC series controllers.
Professional NXC Series Controllers
This series allows you to apply the most flexible and thoughtful approach to managing a Wi-Fi network.
First, there is support for all the above protocols, which allows you to cover a wide range of client devices. If a laptop, tablet, smartphone, and so on is capable of working in modern wireless networks, most likely, it will work without problems on the network running the Zyxel NXC.
At the same time, Zyxel continues to take care of users and their business, which is why it also offers some specialization here. At the time of this writing, two models of controllers have been released: the NXC5500 model for larger networks and the NXC2500 model for smaller IT infrastructures. In principle, both devices have the same set of functions, the only difference is in performance.
Common features of the NXC5500 and NXC2500
Auto Healing
With this function, the controller checks the status of neighboring points and automatically adjusts the signal strength. If the access points are working normally, their signal level is adjusted so that they do not interfere with each other and do not consume additional energy.
If one of the access points fails, the controller instructs the neighboring points to increase the signal power in order to cover the resulting “dead zone”. When the point comes back in operation, the controller will indicate the need to reduce the signal level.
Client Steering
Client Steering helps dual-band devices select 5 GHz as their priority to relieve the 2.4 GHz band, which is often used by legacy customers.
The client signal threshold automatically switches the device to access points with a stronger signal. These two functions provide more efficient use of network resources and maximum wireless network speed.
ZyMesh
The ZyMesh feature is used to support Wi-Fi in areas where it is difficult to run an Ethernet cable.
In addition, each access point with a repeater function has a set of alternate routes for continuous access to Wi-Fi. ZyMesh is able to independently provide network resources. This function is used for efficient centralized management of multiple access points.
Comprehensive Account Management
NXC series controllers provide dynamic account creation and support the necessary user authentication methods. This flexible approach is necessary for seamless and secure user access to any network, even a very complex one.
MAC-based authentication and the Captiva customizable authentication portal can be used for businesses, hotels and public places. Authorization using a QR code makes it easy to set up secure Internet access from mobile devices without using a keyboard.
NAT Traversal
This function allows you to provide a connection through a NAT gateway between different networks to control remote points and provide users with access to the necessary resources.
Secured wireless edge
The use of this feature allows you to avoid security problems when using Wi-Fi at the edge of the network.
The controller finds and isolates unauthorized access points that may pose a potential threat.
Support for standard WPA / WPA2-Enterprise authentication, various Extensible Authentication Protocol (EAP) implementations, and built-in firewall helps prevent intruders from acting.
Zyxel Wireless Optimizer
Devices from the NXC family are capable of working with the Zyxel Wireless Optimizer (ZWO) utility. The use of this software simplifies the planning, deployment and management of a Wi-Fi network at no additional cost, such as purchasing expensive site survey tools and installing additional sensors or location servers.
Support for all seamless roaming standards
I would like to emphasize once again that NXC controllers support all the standards required for seamless roaming - 802.11r / k / v, as well as proprietary Load Balancing and RSSI Threshold, which allow clients to connect or disconnect "without their demand" .
Note. On the Zyxel firewalls, support for 802.1 k / v will also appear, but after a while.
NXC5500 Features
A large number of supported points The
NXC5500 can centrally support managing up to 1024 access points inclusive. This is a fairly large number of devices for which you can perform all the necessary settings in a few minutes.
It is also worth noting that the NXC5500 has 6 built-in Gigabit Ethernet ports, to provide high bandwidth and flexible configuration of the wireless network.

Figure 3. High-performance controller NXC5500 - control up to 1024 access points inclusive.
The Wi-Fi and RTLS
Deployment Site Survey NXC5500, together with Zyxel's partner, Ekahau, allows you to perform site surveys, and provides Real-Time Location Tracking Systems (RTLS) service for site selection and rapid deployment of wireless infrastructure.
Note . More information about the features of the NXC5500 controller can be obtained from the technical specifications .
Features NXC2500
Despite the fact that the NXC2500 controller was developed as a “junior model”, it also has something to be proud of compared with its older brother - the NXC5500

Figure 3. The Wi-Fi Access Controller NXC2500 is an elegant and affordable solution for small and medium-sized companies.
Big time between failures
For the NXC2500, the upper limit of time between failures is set at 815,464 hours, in terms of years it is more than 90 years. For the NXC5500, this is a slightly more modest value of 43,800, which corresponds to about 5 years.
This feature has arisen due to the fact that the NXC2500 uses passive cooling, which means there is no need to replace the fans.
Note . More information about the features of the NXC2500 controller can be obtained from the technical specifications .
Conclusion
Summarizing, we can say that the organization of uninterrupted operation of the Wi-Fi network is not so difficult and expensive. Properly selected equipment together with an understanding of the principles of operation allows you to create an effective solution that meets the requirements of users.
Sources
- Zyxel webpage dedicated to USG gateways
- Zyxel NXC5500 controller description
- Zyxel NXC2500 controller description
- The article “ Roaming in WiFi networks - 802.11i / r / k / v / OKC, what we really need and how to recognize it ”
