Petya crypto ransomware actually destroys user data, sending money is pointless
Many people write about ransomware, dubbed Petya / PetrWrap . And this is not surprising, because it is he who is the central element of the most powerful cyber attack, which affected the computers and computer networks of commercial companies, government organizations and individuals in Ukraine, Russia, Belarus and many European countries. Outwardly, Petya looks like an ordinary crypto ransomware, the authors of which promise to decrypt the user's data if he sends a ransom.
But the reality is somewhat different. The fact is that under the guise of a crypto ransomware hides a virus-viper (ie, “eraser”), the creators of which have only one goal - the destruction of the victim's computer data. Yes, all this is masked by the requirement to send money, but still it’s not worth paying. And not only because the email to which you want to send payment information was blocked by the operator . But also because it is still pointless, the data decryption function is simply not provided here.
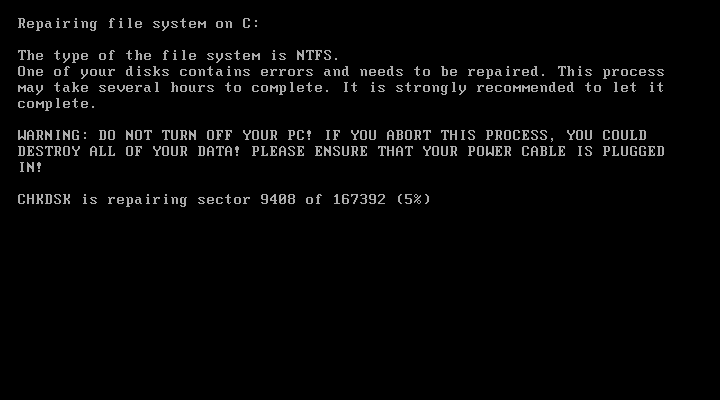
"Crypto extortionist" really asks the victim about $ 300 for returning information from the hard drives of the infected computer. Attackers also scare their victims with the following text: “Do not waste your time. No one can recover your files without our decryption service.”
The text is valid, some infected users Still, they pay a lot of cars, and now there are at least 50 Petya victims (aka ExPetr, aka NotPetya) who paid a total of $ 10,200 in dollar terms, but the affected users don’t know what evil there is no decryption service for money-launderers. Money is thrown to the wind.
According tocybersecurity experts, for their money these users will get absolutely nothing, because there is an error in the malware code that makes it impossible to decrypt files. The company's specialists analyzed the malware code, the area that is associated with file encryption, and realized that after the disk is fully encrypted, the victim loses the opportunity to get his information back.

The fact is that when processing the file exPetya does not create a unique installation ID for the program. Accordingly, when a victim requests payment, the user receives a completely random set of characters. Perhaps the new version of ransomware has nothing to do with the original Petya malware, since the original virus created this ID during installation. Here is the piece of code that is responsible for creating the ID.

The screenshot shows that the ID is randomly generated, which blocks the possibility for the victim to get a key to decrypt their files, even if it exists.

An attacker simply has no way to extract information for decryption from a string of random characters. The 2016 Petya version encrypted the drive in such a way that it could be decrypted with a key. All operations with files and disk sectors were performed correctly. But Petya from 2017 irreversibly damages drives.

On the left is a section of exPetr code that seems to have turned into a viper
Moreover, in the exPetr code there is a section that is responsible for the operation of the viper. When this code section is activated, the virus completely erases user data. So, the malware overwrites the file location table (Master FAT Table) and the master boot record (Master Boot Record) of the computer on which the virus is installed. This is a distinctive feature of the new virus, which is not typical for ransomware.

Many cyber-security people agree with the above opinion. For example, Matt Swish of Comae Technologies tellsthat Petya simply destroys data, as other wipers, including Shamoon, do it. And the goal for the developers of malicious software is completely different than the one pursued by the creators of real crypto ransomware. Everything is simple there - attackers want money. In the case of vipers, the situation is more complicated - what their creators want, only they know.
Other features of the virus include the command to restart the infected PC an hour after infection. For this, the undocumented feature of the WinAPI NtRaiseHardError function is used .
