Aether Management Console: How to Deploy Enterprise Security

The main steps that need to be taken to implement Panda corporate protection on Windows, Linux, Mac, Android devices from the Aether central management web console.
In this article, I want to tell you how to quickly install the Panda enterprise cloud security solution from the Aether central management web console, and what needs to be done to configure and deploy Panda on the corporate network. I think that the article will be useful in testing the Panda corporate solution, as well as in its initial implementation.
The information presented in the article is valid for Panda Endpoint Protection , Panda Endpoint Protection Plus , Panda Adaptive Defense and Panda Adaptive Defense 360 solutions , which are controlled from the new Aether management console .
Preliminary Actions
Before you begin installing your Panda enterprise solution, make sure that:
- You have the credentials to access the Panda enterprise solution Aether cloud-based central management console.
- You have read the URLs and ports for the product to work correctly .
1. Quick launch of Panda
1.1. Connecting to the management console
In order to protect the corporate Panda solution, you need to log in to the Aether cloud-based central management console. There are two ways to do this:
1. From the invitation letter : When registering the licenses of the Panda corporate solution, an invitation letter should have arrived at the e-mail address indicated by you, in which your registration information was indicated: link to go to the management console, login and password.
2. Directly open the management console :
a. Go to www.pandacloudsecurity.com
b. Enter your username and password
c. Click the Login 1.2 button
. Quick installation of protection
If this is your first time logging into the Panda management console and / or you have never set up protection within your account, you will see a start page offering to add computers. As part of the quick installation, you can install protection on the required computers with the default settings. In any case, later you can change the computer settings and security at your discretion.
To perform a quick installation on your computer, click the Add Computers button .
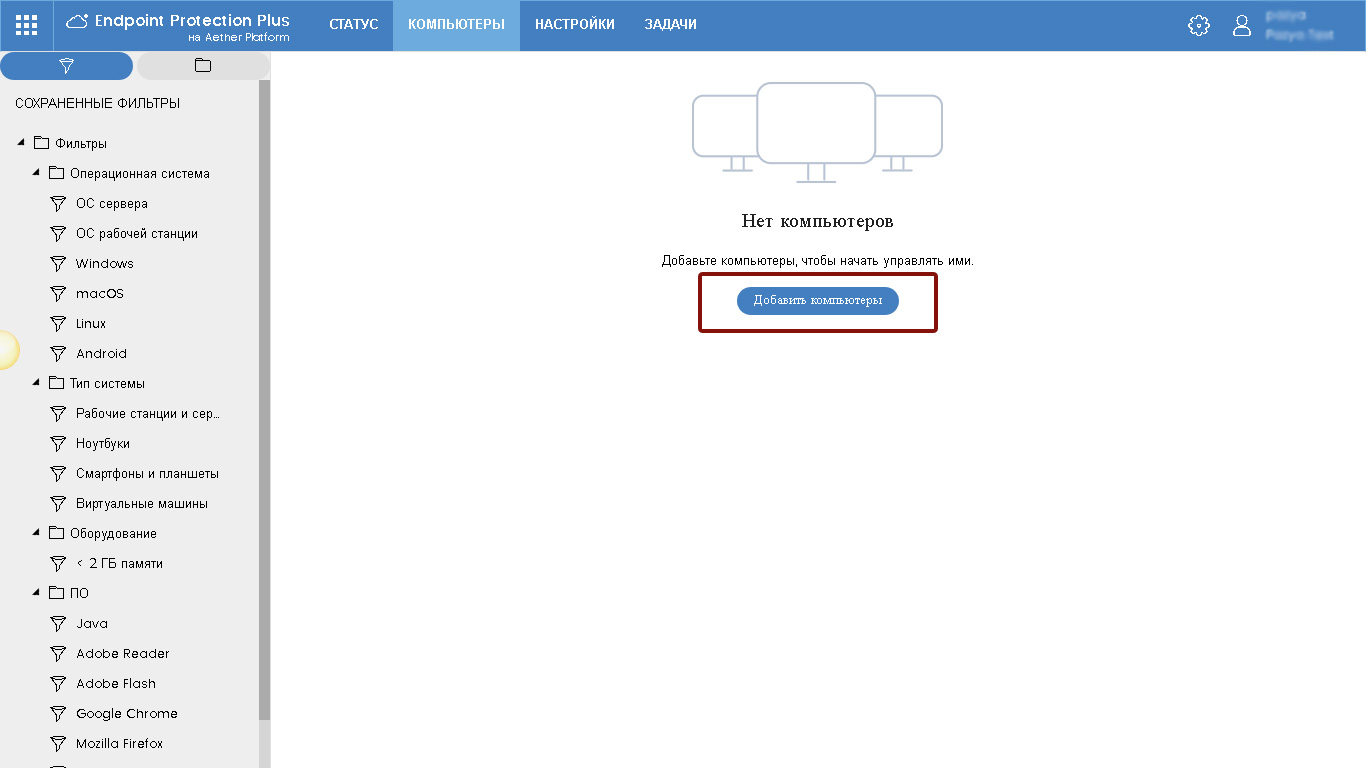
Fig. 1. Quick installation of protection
As a result of this, a window opens for choosing the operating system of the computer on which it is planned to install Panda protection.
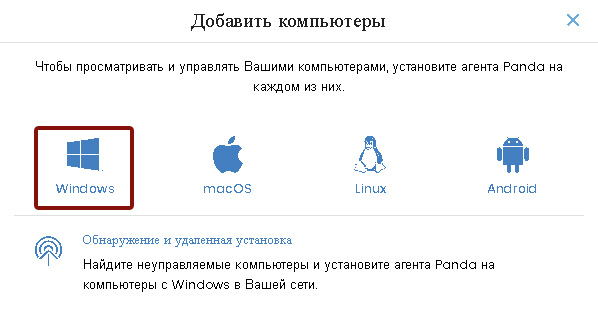
Fig. 2. Choosing a computer operating system
As part of a quick installation, select the operating system of your computer (for example, Windows) by clicking on its logo. After that, a window will open for selecting installation parameters.

Fig. 3. Downloading the installer
In this window, click on the Download installer button . As a result, the Panda Endpoint Agent.msi file will be downloaded to your computer. Next, follow these steps:
1. Uninstall your current antivirus solution. It is recommended that you restart your computer.
2. Run Panda Endpoint Agent.msi to begin installing Panda Protection.
3. Click on the Next button to start the installation process, and after the Install button. The local Panda Endpoint Agent protection agent will be installed on the computer.
4. Click on the Finish button to complete the installation wizard.
5. Double-click the Panda icon located in the system tray on the taskbar to see the Panda Endpoint Protection installation indicator. The installation process may take several minutes.
You can also see the installation indicator in the console. Connect to the console and select Computers from the main menu .
During the installation process, you will be asked to restart the computer to complete the installation. Please restart your computer when necessary.
After completing the above steps, your computer will be protected with the Panda corporate solution.
1.3. Verifying
that the protection is working correctly To verify that your protection is working correctly, you can perform the following steps:
Go to www.eicar.org/download/eicar.com . In this case, an attempt will be made to download a file that each antivirus solution recognizes as an Eicar-Test-File (Eicar-Test-File is a file developed by the European Institute for Computer Antivirus Research to test the response of antivirus programs. For more information, visit ) .
Congratulations! Your computer is now properly protected with the Panda enterprise solution.
You can configure your protection more correctly by following the basic steps, which are presented in the next chapter 2.
When setting the default protection, it is quite possible that the protection will be installed in English. You can always change the language settings in the management console.
2. Three basic steps to configure Panda Endpoint Protection
The first chapter of this document contains information about the quick installation of Panda Corporate Security on your computer within the default settings. This chapter presents several basic and very simple steps, the implementation of which will allow you to more correctly configure the protection of all required computers and devices using the corporate Panda solution.
If you need background information about the product, access to the manual for the administrator, etc., just click on the gear button in the upper right corner of the web console and select the appropriate item in the drop-down menu.
If you have questions or need further assistance, please do not hesitate to contact your supplier or the Panda Security office, all of which are listed at the end of the document.
2.1. Step 1: Configuring Settings
The management console allows you to configure settings for computers, networks, and security. As a result, profiles are formed that can subsequently be assigned to the required computers. Parameters can be configured both before and after installing local protection agents.
To configure the settings, go to the Settings section .
2.1.1. Configuring the security of workstations and servers
When you go to the Default settings section , the subsectionSecurity -> Workstations and servers . Here you can configure security settings for workstations and Windows, Linux, and Mac servers.
By default, there is a Default Settings profile that cannot be changed or deleted. Therefore, you can create your own profile by clicking on the Add button .
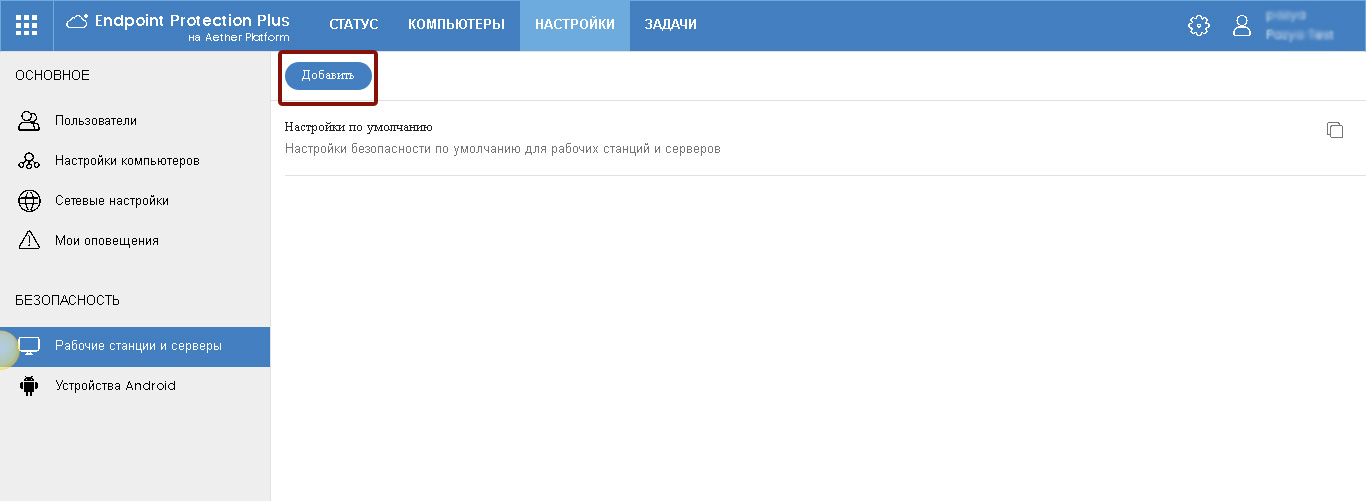
Fig. 4. Workstations and servers
On the add profile page, specify its name, a brief description (optional) and click the Save button .
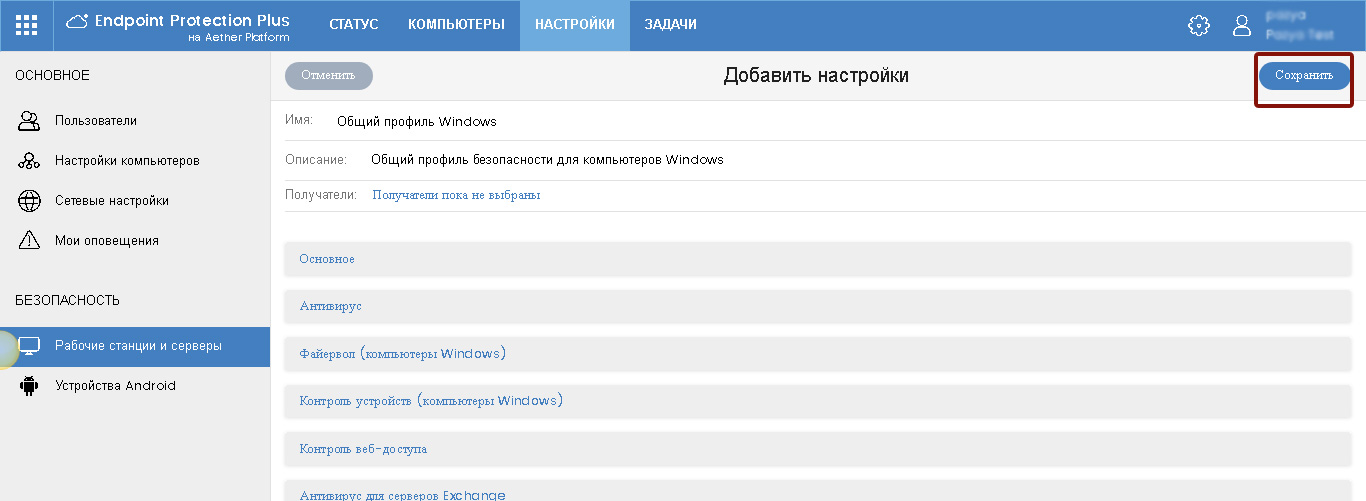
Fig. 5. Adding a security profile
After that, in the saved profile, you can make basic settings for security parameters and all the required settings for various product modules.
2.1.2. Computer settings
In the Settings section, select the Computer settings subsection . Here you can configure the basic parameters of the protection on protected devices. There is also a Default Settings profile here , but you can create your own profiles by clicking the Add button .
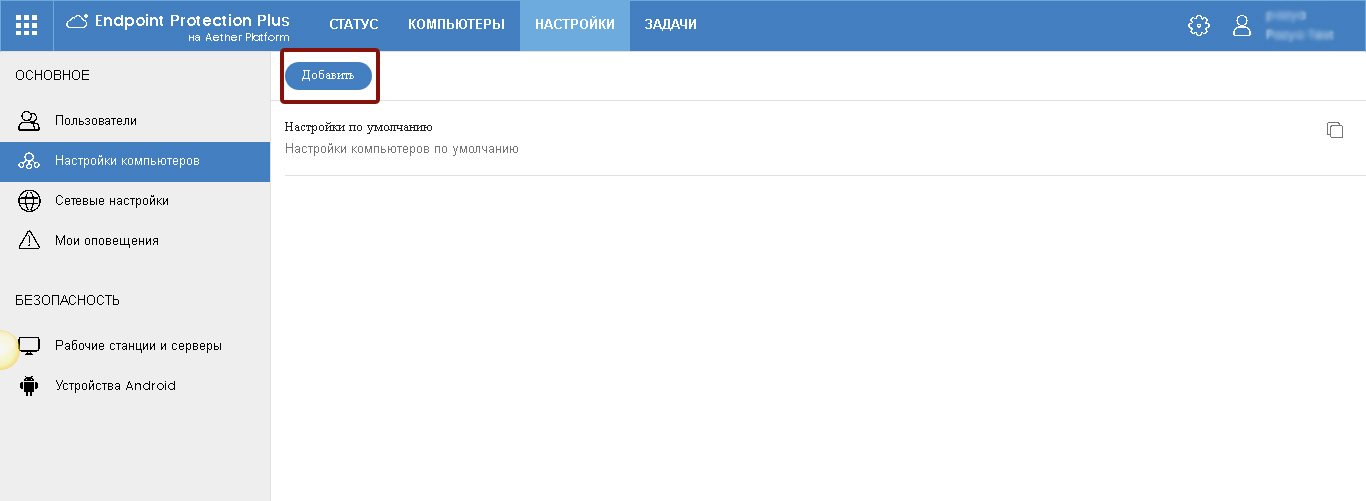
Fig. 6. Computer settings
As a result, a page opens with the addition of a settings profile.
On the add profile page, specify its name, a brief description (optional) and click the Save button .

Fig. 7. Adding a computer settings profile
Settings are presented in two sections: Updates andProtection against unauthorized interference with the protection. Specify the required settings.
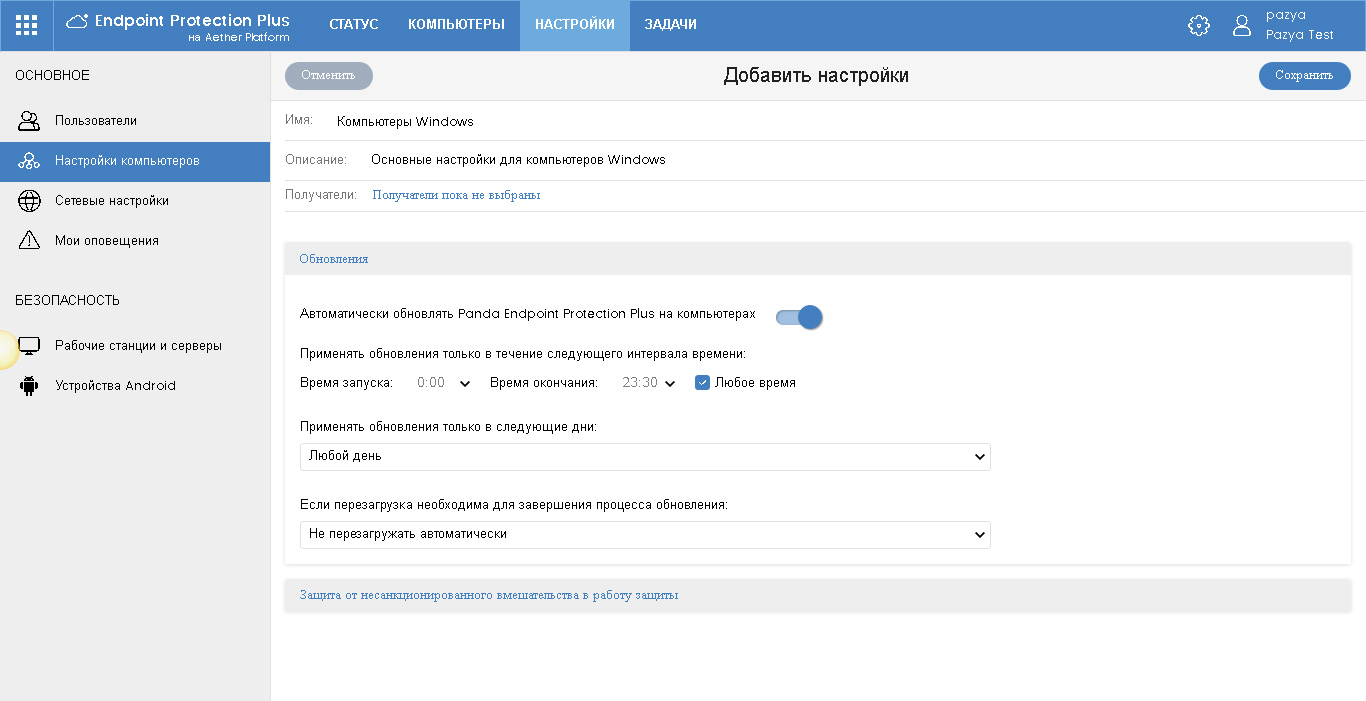
Fig. 8. Computer protection update
settings In the update settings, you can specify the update settings for local agents of the Panda corporate solution. We recommend that you enable automatic updates at any time, but if necessary, you can specify a specific update schedule (certain days and hours).
In addition, specify whether to automatically restart computers to complete the update process (if required), and if so, which ones (only servers, only workstations, or both).

Fig. 9. Protection settings against unauthorized interference with the protection
In the anti-tamper protection settings section, it is recommended to request a password when removing protection from computers to exclude cases when employees can delete the local agent.
Also, just in case, you can enable the management of security modules from the local console. There are no special risks, because To do this, you still need to know a special password (it is configured immediately below), but in certain cases, for administration or troubleshooting, it is advisable that you have the opportunity to access advanced options in the local console.
2.1.3. Network Settings
In the Settings section, select the Network Settings subsection. Here you can configure basic network parameters for the protection to work on protected devices.

Fig. 10. Network Settings
This page has three tabs: Proxy and Language , Cache and Discovery .
Proxy and language
The most important thing is to check the settings in the first tab so that the product as a whole functions correctly. There is a default settings profile here , but we recommend creating your own profiles, as in the default profile, which cannot be changed or deleted, the protection language is set to English, and proxy settings are not made (if necessary).
To add a profile, click the Add button.. Indicate the name of the profile and its description (if necessary), and also set the required options in the Language and Proxy sections .
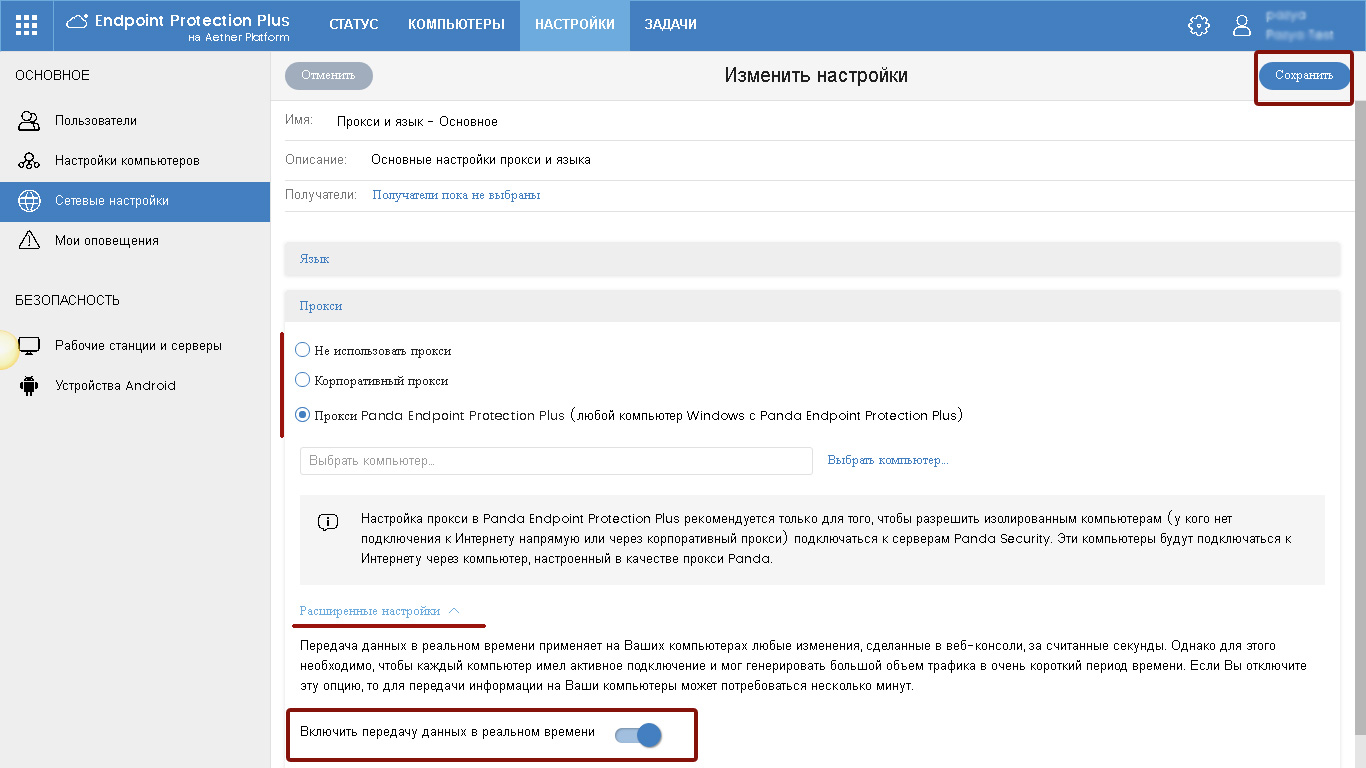
Fig. 11. Language and proxy settings
As for the Proxy section , if necessary, you can specify the corporate proxy settings or select one of the computers on which the local Panda agent is installed, which will act as the Panda proxy. Panda proxies are only recommended to allow isolated computers (who do not have an Internet connection directly or through a corporate proxy) to connect to Panda Security servers. These computers will connect to the Internet through a computer configured as a Panda proxy.
We also recommend that you enable the Enable real-time data transfer option in the advanced settings, if possible . By and large, this will not greatly increase traffic, however, remote tasks and the application of settings will be implemented in real time.
Cache
tab cache You can configure one or more computers that will operate as a cache to store updates, installers and any other packages downloaded from the Internet. Thus, all updates and downloads will be transmitted within the network not using peer-to-peer technologies from the nearest available updated computers, but only from directly configured cache computers. See Admin Guide.
Detection
On this tab, you can configure computers from which you will search for unmanaged / unprotected computers on which you can quickly install Panda protection.
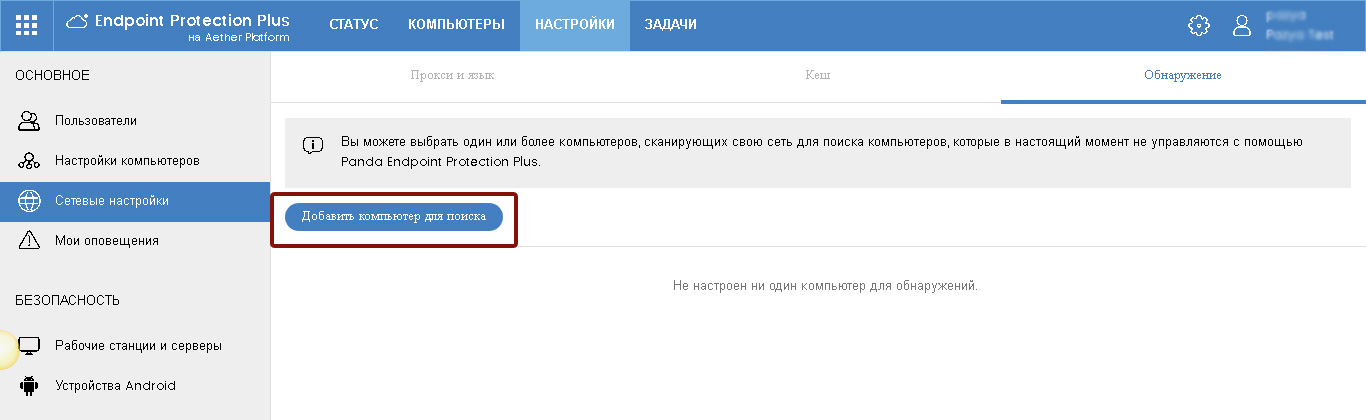
Fig. 12. Adding computers for search
To add a computer for search, click the Add button , and then in the list of computers with Panda protection installed, select the computer that will be used to search for other unmanaged / insecure computers. In the event that you have several networks / network segments, we recommend that you specify a separate computer for each of them.
After that, the selected computer will appear in the list. To carry out automatic verification right now, click on his link Check now. Click on the Configure link to configure the operation of the computer discovery function.

Fig. 13. List of computers to search
On the settings page, specify the required settings for the detection options for unmanaged computers. To save the settings, click the Save button .

Fig. 14. Computer settings for search
2.2. Step 2: Install Security
Panda offers you several ways to install security. But regardless of the selected method, as part of the installation process, a communication agent is downloaded and installed, which starts the process of installing local protection on the required devices.
Ways to install Panda protection on your network:
1. Installer
Allows you to download the msi file, which you can distribute on the required computers using third-party software distribution tools (SMS, Tivoli, etc.), as well as manually. Suitable in cases where you use automated software implementation tools in your network.
2. URL
Allows you to generate a URL, when you click on it, the automatic installation process starts. This URL can be emailed. This method is most suitable for automated installation of the product on remote computers located outside the local network, to which you do not have administrative access, and also if you do not have the knowledge / ability to use automated software implementation tools or your network is quite small.
3. QR Code / Google Play (for Android)
This method is intended only for Android devices and allows you to transfer a QR code or a link to go to Google Play for devices with Android
4. Remote computer detection
If you have computers configured to remotely detect unmanaged computers on the network, you can automatically find unmanaged computers, remotely install Panda protection on them, and then bind these computers to the required groups and profiles.
There is also the possibility of an automated installation through integration with Active Directory. See Admin Guide.
To add computers, go to the Computers section and click the Add Computers button .
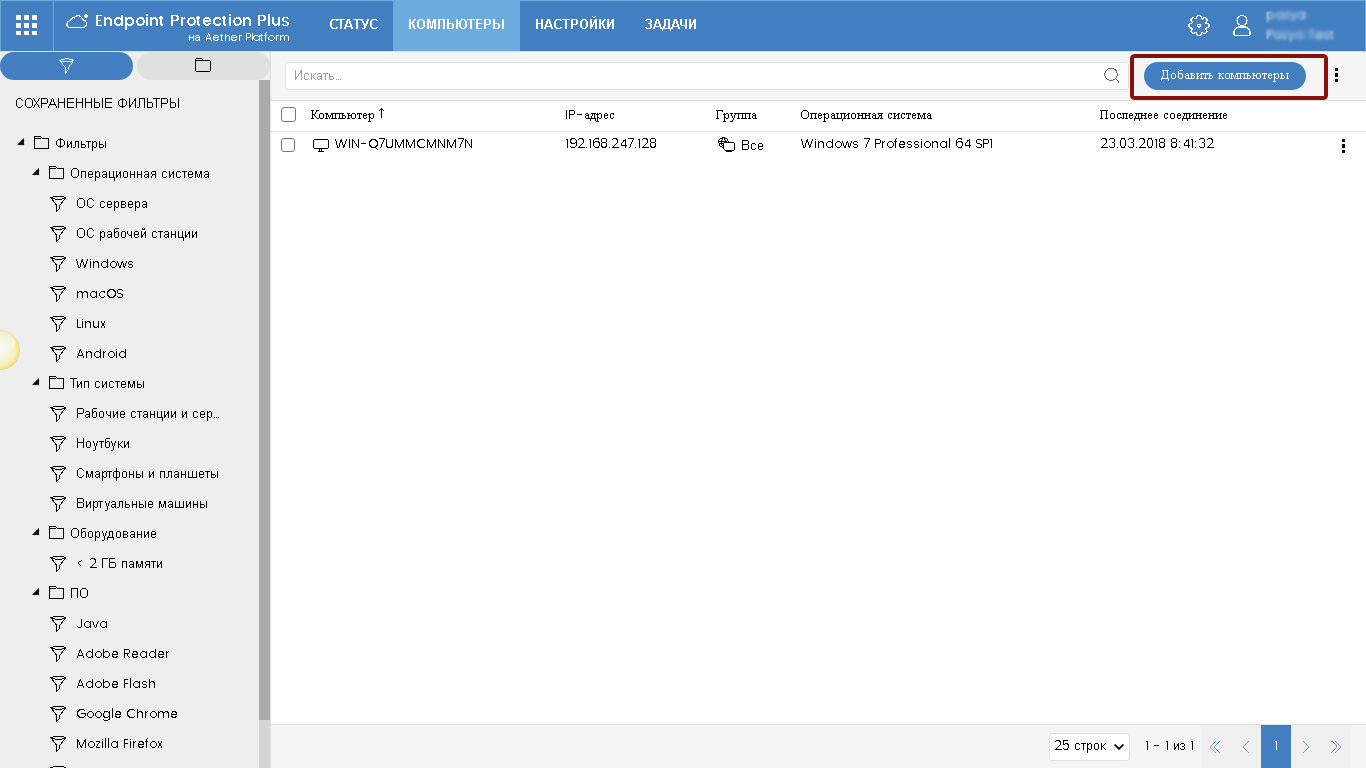
Fig. 15. Adding computers
2.2.1. Implementing protection using remote discovery
In the window that appears, click the Discover and remote installation link .
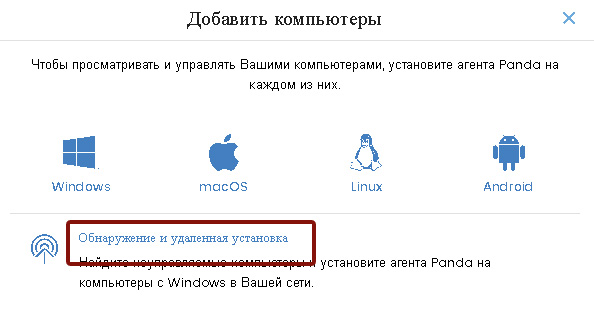
Fig. 16. Adding computers using remote discovery
Then, specify the computer that will be used to search for unmanaged computers. After performing the search, you can view the detected unmanaged computers in one of the following ways:
• in the Status section of the Protection status widget, a warning about found unmanaged computers appears
• in the Status section of the My Lists context menu, you can add a quick jump to view the list of unmanaged computers
After that, in the list of unmanaged computers, you can remotely start the installation of the Panda agent, after which these computers will be added to the Computers section , where you can bind them to the required groups and profiles. See the Administrator Guide for more details.
2.2.2. Implementing protection using the installer
In this case, in the add computers window (see Figure 16), select the required operating system (Windows, Linux, Mac), specify the appropriate group and configuration profile, and click the Download installer button .

Fig. 17. Adding computers using the installer
As a result of the steps taken, you will download the installation file in msi format to your computer, which you can then distribute using automated software injection tools or run manually. Keep in mind that all computers on which this installer will be launched will be automatically added to the group of computers that you selected when downloading it.
2.2.3. Implementing protection using URLs
Follow the same procedures as during installation using the installer (see section 2.2.2), but at the end click the Email URL button . As a result of this, a Microsoft Outlook window (or another installed and configured mail agent) will open to send an email with a link.
By the way, this method can also be used to install protection on Android devices.
As a result of the actions performed, you will be able to provide users with appropriate links for installing protection on their computers and devices. Keep in mind that all computers on which this URL will be opened will be automatically added to the group of computers that you selected when generating it. Please note that as part of this method, the installation process depends on the end user (he must click on the URL to start the automatic installation process).
2.2.4. Implement security with a QR code or Google Play
In this case, in the window for adding computers (see Fig. 16), select the required operating system (Android), specify the appropriate group into which you want to automatically add device data from Android.
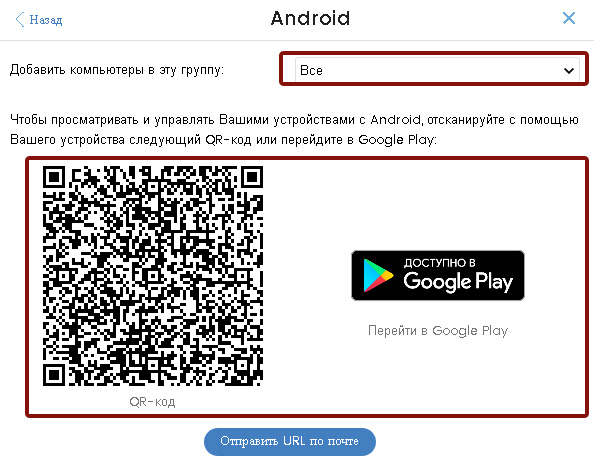
Fig. 18. Adding an Android device using a QR code or Google Play
After that, you can scan the QR code or click on the Google Play link if you want to protect your current Android device. You can also send a QR code as a picture to the required users in any way possible.
2.3. Step 3: Protection Monitoring
In order to verify the correct implementation of Panda protection in your network, as well as to monitor and control the protection status of computers and devices and perform the required management, control and protection tasks, you need to go to the sectionComputers .
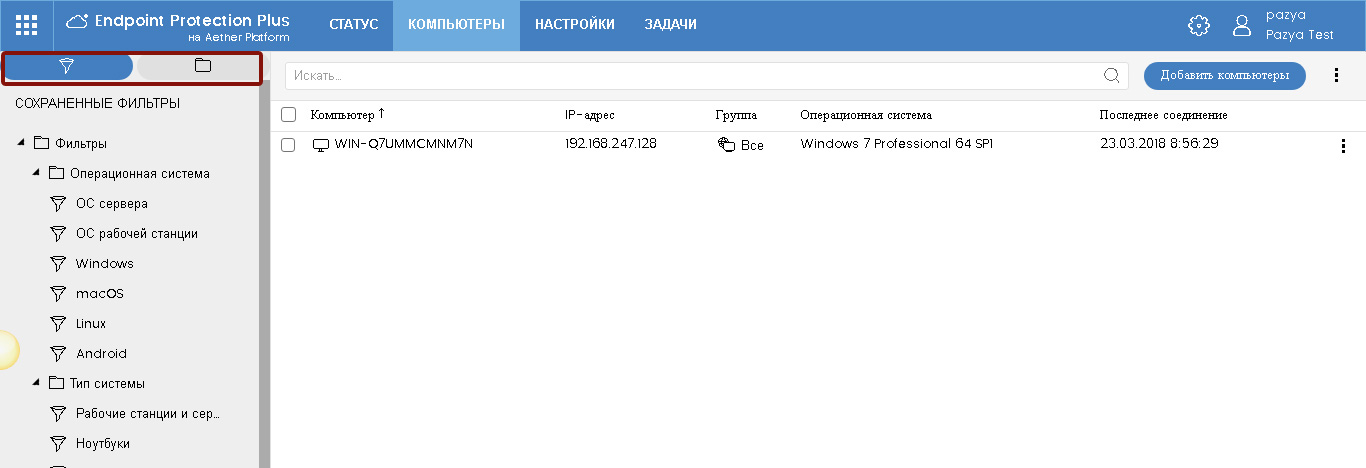
Fig. 19. List of computers
On the left side of the screen is a block for selecting the required computers either by filters or by the organizational tree (groups and folders of Active Directory). In the central part is a table with a list of computers.
In this section you can select the required computers, check their status, remotely perform various tasks in relation to the required computers (groups of computers), etc. When you click on a computer of interest, you can go to the page with detailed information about it.
What actions and how can be done in relation to computers, see the Administrator Guide.
3. Local agent
As a result of implementing the solution, a local agent will be installed on the protected devices, and the product icon will be displayed in the system tray.
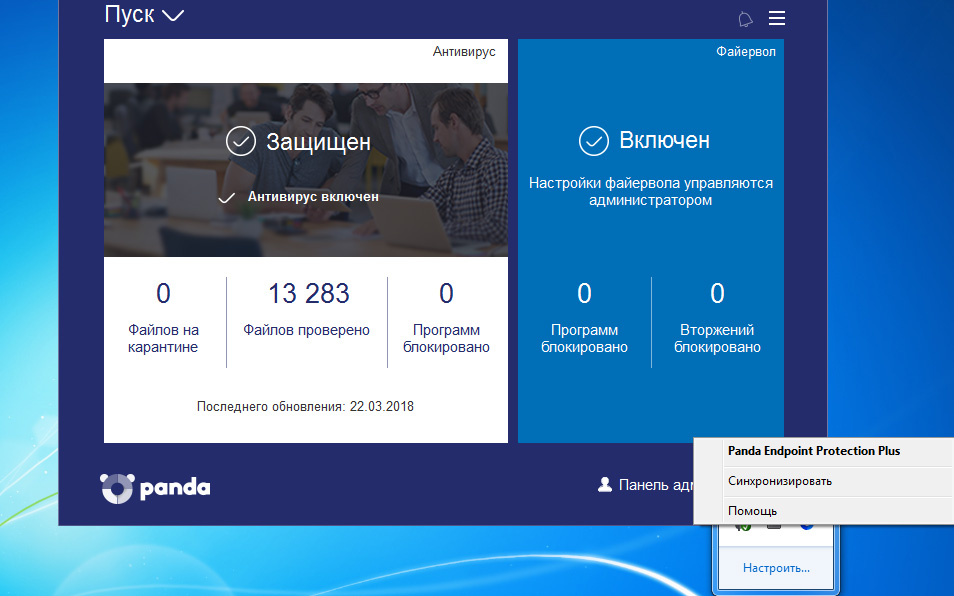
Fig. 20. Local console
In the local agent, the user can check the information on the latest detections, run an anti-virus scan on demand, synchronize the local agent with the cloud and refer to the online help.
In that case, if the security profile implies the possibility of local firewall management, then in the local console the user will also be able to manage it.
In addition, the local console has a link to access the admin panel, access to which is limited by the administrator password (see section 2.1.2.). In this case, the administrator can go to this panel to make changes to the operation of the modules.
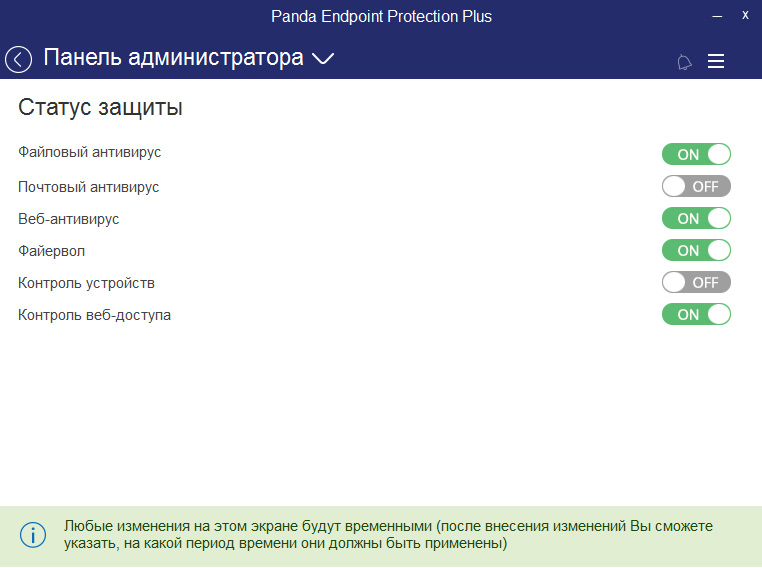
Fig. 21. Admin panel in the local console
In the event that some changes are made to the operation of the modules, they will by default be active for 6 hours, although you can set a different period of their activity.
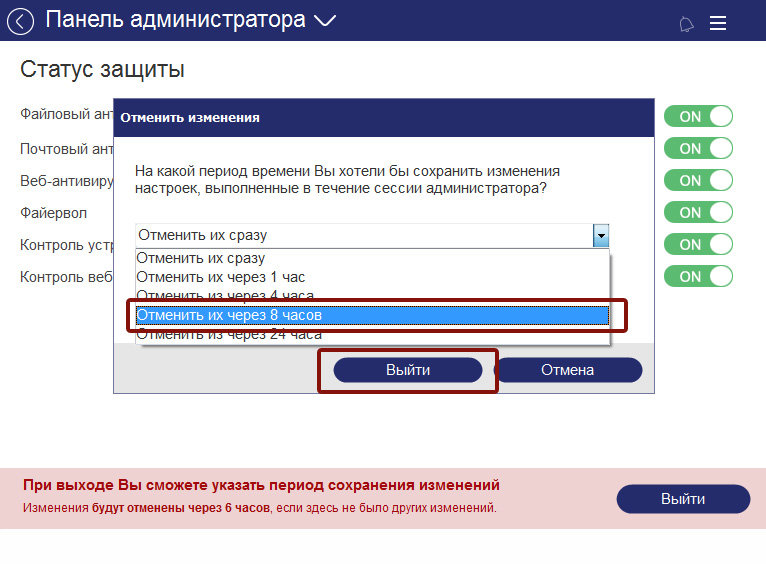
Fig. 22. Selecting the date for canceling changes in the local console admin panel
Conclusion
As a result of the above steps, you can centrally and remotely deploy Panda corporate protection on the required computers and devices quite simply and quickly. For details on how to configure and operate Panda Corporate Security, see the Administrator Guide, which is available in the management console.
Thank you for your interest in Panda.
