Puzzle "Test My Patience" by Check Point Security Academy
- Tutorial
I mentioned the program “Check Point Security Academy” several times on Habré : its essence is that the Check Point firm in the summer announced a contest in the “Capture the Flag” format, where the participant’s past experience is not important, and only his ability to disentangle a cyber is important. puzzles. According to the results of this competition, the company recruited twenty participants for a three-month professional course on cyber security, and all participants from the very beginning of the course receive a full salary of a specialist in KB, under the obligation to work in the company two years after the end of the course.

In a CTF competition, the flag may even be a picture, for example.
The selection of participants was completed in August, but the competition site will continue to operate until next summer, and I invite those who wish to register and try their hand for sporting interest. The competition consists of 12 puzzles of varying difficulty, rated from 10 to 150 points.
Here I want to make out the “Test My Patience” puzzle from the “Surprise” category. She is of medium difficulty (50 points), and here is her full text:
Inside the binary, it is encrypted; it refuses to run under the debugger; if you try to connect a debugger to it that is running, it ends instantly. Probably, experts from Check Point wrapped their puzzle in a crypto-packer, borrowed from some Malvari.
How can we guess the number, thought of by a watchmaker?
There are two ways. The first can be conditionally called “the power is, the mind is not necessary”: if the program can not be debugged live - then we will debug the dead!
Run the 32-bit Task Manager (\ Windows \ SysWOW64 \ taskmgr.exe), right-click on the mysterious process, and select Create dump file. (The 64-bit Task Manager for 32-bit processes creates a wow64cpu emulator dump, which is more difficult to work with.)
We look into the dump and see that at least the lines in it are already decoded:
But the lines with neither the number nor the flag not yet seen.
Moving on to the main-caliber gun: WinDbg (X86) -> Open Crash Dump ...
Where in memory is that line that we want to see printed - “Good job my friend!”?
Team
Let us now find where this string is printed: maybe some command contains bytes
Good luck! - such a command was found:

What is the code around this command? (
We see that, depending on the result of the function,
The function code
Two pointers are passed, equal to
Is this the function that requests the hidden number? Check the call stack (
Yes, it is she!
The overall scheme of the puzzle is now clear: the user is stored at a guess
All that is left - pull unknown number of stack frame It

Come on, Come on ...

Success! You can uncork something tasty.
But three mysterious things were left without explanation:
So, it turns out that there is a second - more intellectual - way to guess the conceived number. If you just try randomly the numbers 0-9, then it is easy to notice that on the nine, the program a little bit “freezes”. If you try the numbers 90-99, then you can see that on the number 98, the program “freezes” twice as long. (By picking up her offal, we already understand what's the matter: a successful comparison of each pair of characters causes a delay of 0.7s.) To solve the puzzle, even without launching the debugger, it was enough to select each next digit so that the delay before the response increased - either manually with an exact stopwatch, or an uncomplicated script. Thus, the compilers hinted at a long-standing method of attacking cryptographic algorithms when the time to an error message is measured and analyzed.
But learning how to unzip programs wrapped by unknown crypto-packers is, in my opinion, both more interesting and more valuable :-)
Note that we didn’t need to figure out how the binary is encrypted, nor how the line with the hidden number appears on the stack (we saw in there is no dump among the string constants) - we managed to get both ready and ready, and a dozen WinDbg commands were enough for everything.

In a CTF competition, the flag may even be a picture, for example.
The selection of participants was completed in August, but the competition site will continue to operate until next summer, and I invite those who wish to register and try their hand for sporting interest. The competition consists of 12 puzzles of varying difficulty, rated from 10 to 150 points.
Here I want to make out the “Test My Patience” puzzle from the “Surprise” category. She is of medium difficulty (50 points), and here is her full text:
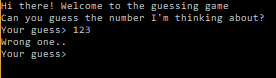
Hi there,The link is a 32-bit binary for Windows, for which some antiviruses swear , but if you run it, it looks like this:
we ’ve found this to be executable on the local watchmaker’s computer.
It is a rumored that
What is your watchmaker?
This note is not malicious in any way.
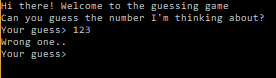
Inside the binary, it is encrypted; it refuses to run under the debugger; if you try to connect a debugger to it that is running, it ends instantly. Probably, experts from Check Point wrapped their puzzle in a crypto-packer, borrowed from some Malvari.
How can we guess the number, thought of by a watchmaker?
There are two ways. The first can be conditionally called “the power is, the mind is not necessary”: if the program can not be debugged live - then we will debug the dead!
Run the 32-bit Task Manager (\ Windows \ SysWOW64 \ taskmgr.exe), right-click on the mysterious process, and select Create dump file. (The 64-bit Task Manager for 32-bit processes creates a wow64cpu emulator dump, which is more difficult to work with.)
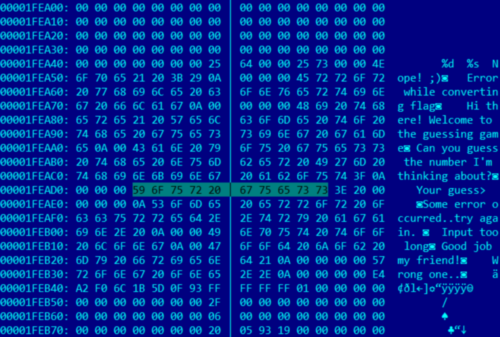
We look into the dump and see that at least the lines in it are already decoded:
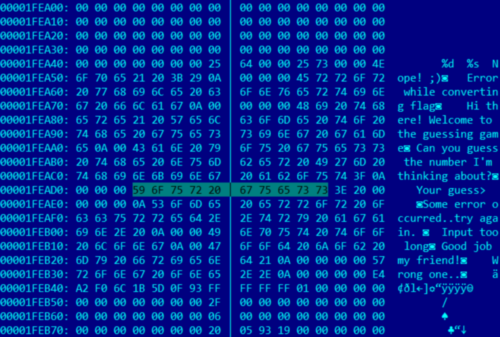
But the lines with neither the number nor the flag not yet seen.
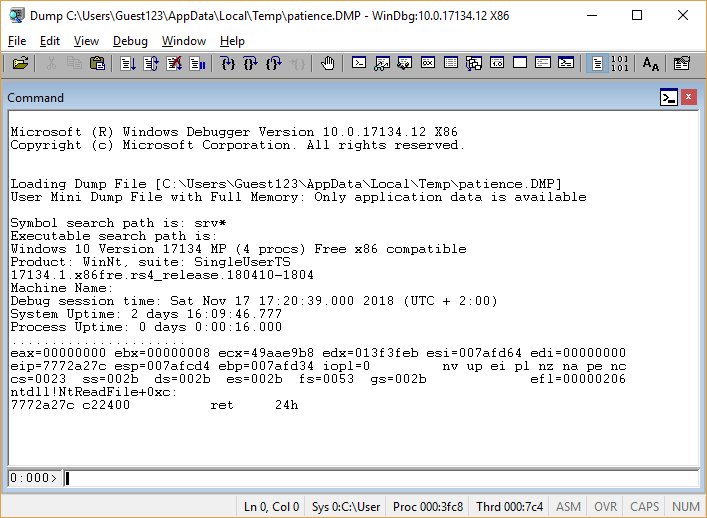
Moving on to the main-caliber gun: WinDbg (X86) -> Open Crash Dump ...
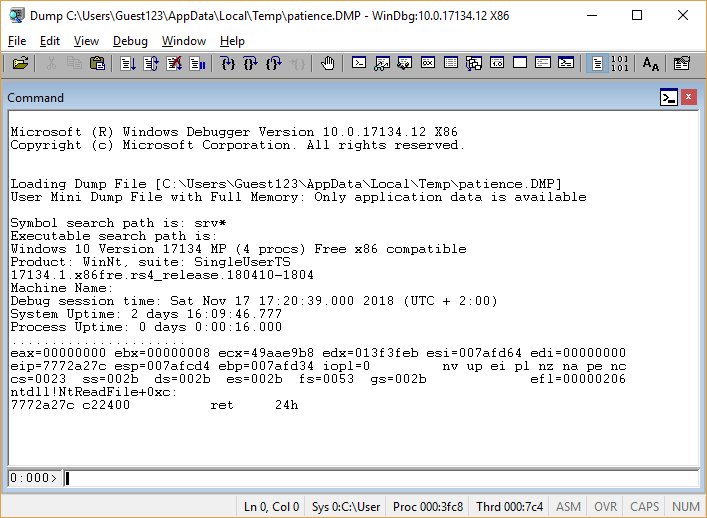
Where in memory is that line that we want to see printed - “Good job my friend!”?
Team
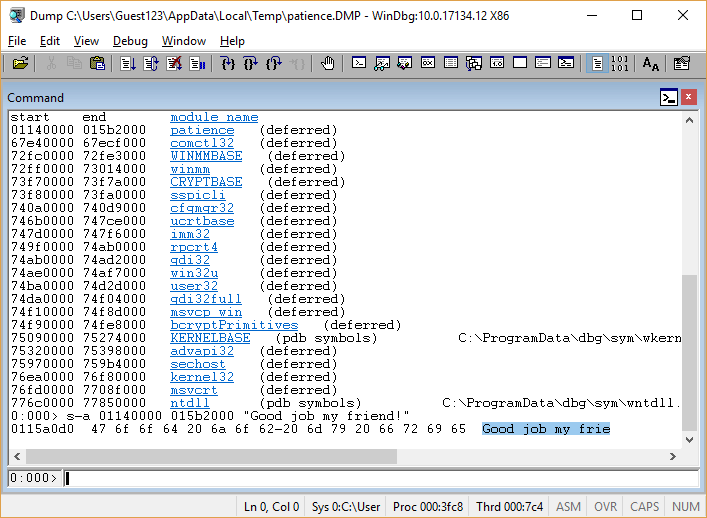
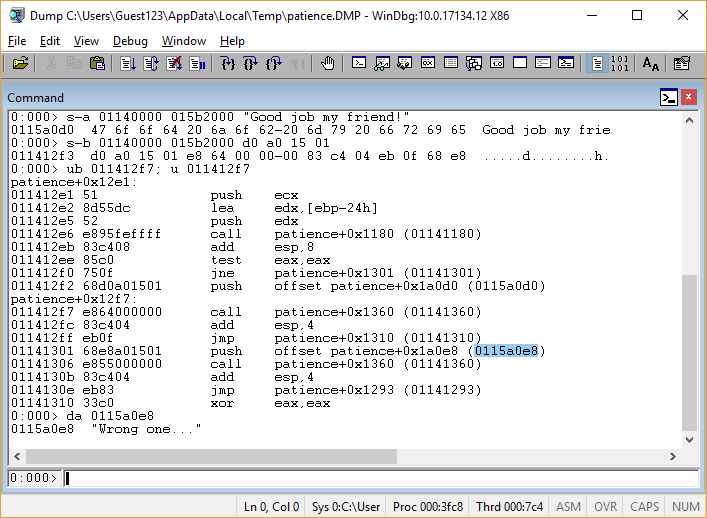
lmallows you to determine that the binary is loaded from 01140000to 015b2000; then it s-a 01140000 015b2000 "Good job my friend!"finds the search string at 0115a0d0: 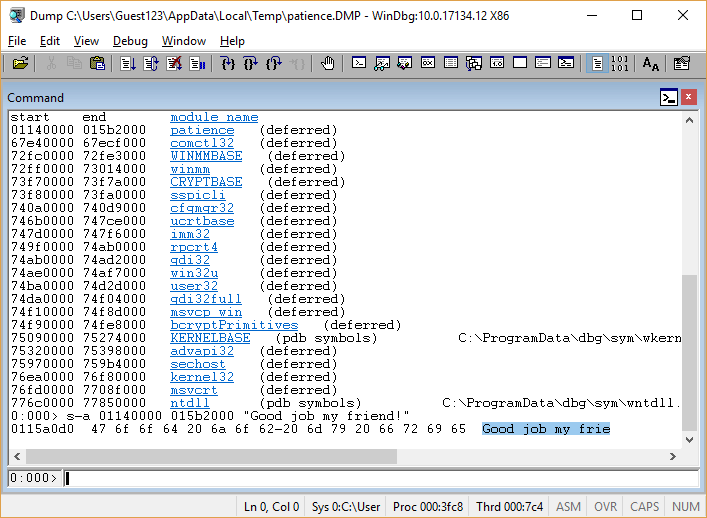
Let us now find where this string is printed: maybe some command contains bytes
d0 a0 15 01corresponding to the address of the search string? ( s-b 01140000 015b2000 d0 a0 15 01) Good luck! - such a command was found:

What is the code around this command? (
ub 011412f7; u 011412f7) 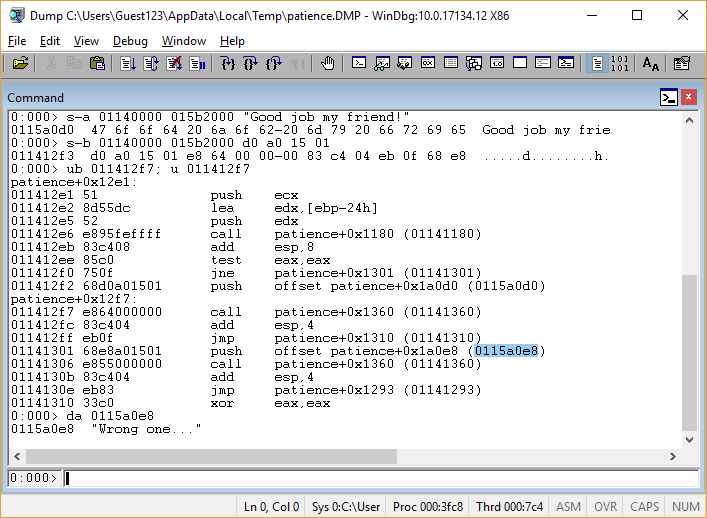
We see that, depending on the result of the function,
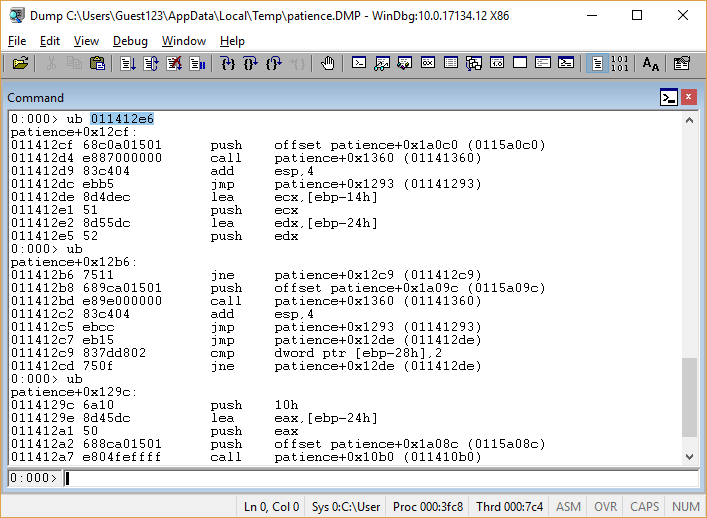
01141180either the search message is printed, or “Wrong one ...” The function code
01141180takes up three screens; it's pretty easy to understand that this is the implementation strcmp()in which the call was added Sleep(700). It is not clear why thereSleep(); but it still does not affect the result of the function, so we better understand what the lines are compared: 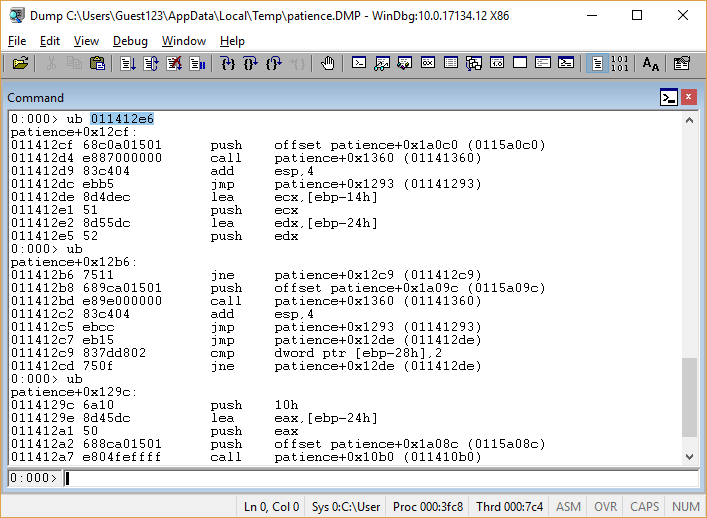
Two pointers are passed, equal to
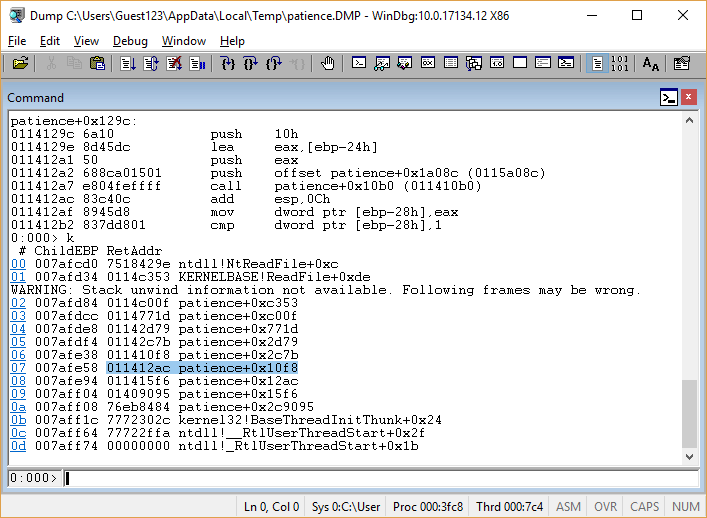
ebp-14hand ebp-24h; the second of them was passed to the function before the argument 011410b0. Is this the function that requests the hidden number? Check the call stack (
k): 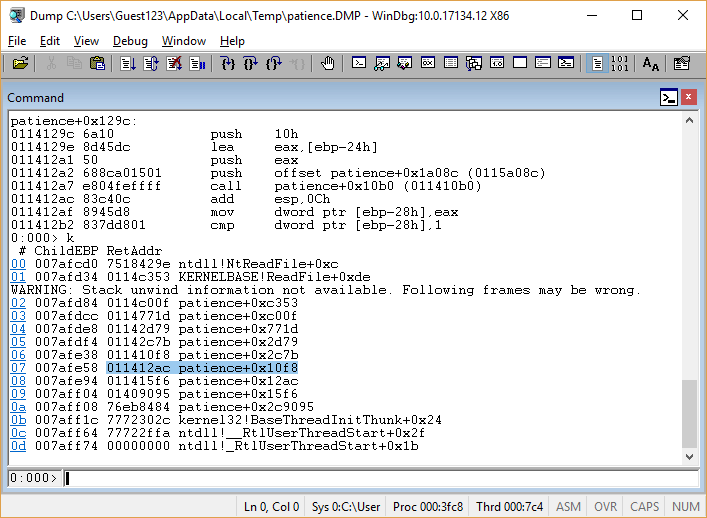
Yes, it is she!
The overall scheme of the puzzle is now clear: the user is stored at a guess
ebp-24h, unknown number - the address ebp-14h, then they are compared, and printed or «Good job my friend!», Or «Wrong one ...» All that is left - pull unknown number of stack frame It
ebpis already known from the call stack: 
Come on, Come on ...

Success! You can uncork something tasty.
But three mysterious things were left without explanation:
- Why inside the local
strcmp()callSleep(700)? - Why, when we entered the hidden number, did the program hang up for a dozen seconds before typing “Good job my friend!”?
- What does the watchmaker have to do with this whole puzzle?
So, it turns out that there is a second - more intellectual - way to guess the conceived number. If you just try randomly the numbers 0-9, then it is easy to notice that on the nine, the program a little bit “freezes”. If you try the numbers 90-99, then you can see that on the number 98, the program “freezes” twice as long. (By picking up her offal, we already understand what's the matter: a successful comparison of each pair of characters causes a delay of 0.7s.) To solve the puzzle, even without launching the debugger, it was enough to select each next digit so that the delay before the response increased - either manually with an exact stopwatch, or an uncomplicated script. Thus, the compilers hinted at a long-standing method of attacking cryptographic algorithms when the time to an error message is measured and analyzed.
But learning how to unzip programs wrapped by unknown crypto-packers is, in my opinion, both more interesting and more valuable :-)
Note that we didn’t need to figure out how the binary is encrypted, nor how the line with the hidden number appears on the stack (we saw in there is no dump among the string constants) - we managed to get both ready and ready, and a dozen WinDbg commands were enough for everything.
