The problem-game method of motivating a student of the specialty "Information Security"
The first article already mentioned the problems of lack of motivation among students. An attempt to combat them will be discussed further.
Having a problem
Let me remind you of the main problems associated with the lack of motivation of students in IS specialties:
- the lack of a meaningful connection between general disciplines (primarily mathematics for technical specialties) and special ones, due to the difficulty of coordinating topics between departments and the maximum unification of courses for the maximum number of specialties taught at a university;
- lack of motivation to study (I came across the following motivation of students: “to quit the army”, “find a husband”, “what was enough money for”);
- lack of motivation from teachers to teach those who do not want to learn.
The fact that this problem is of a systemic nature, recognized at the state level, is also indicated by the presence of relevant sections in the "Main Areas of Scientific Research in the Field of Ensuring the Information Security of the Russian Federation" of the Security Council of the Russian Federation.
List of directions
3. Problems of personnel support of information security of the Russian Federation.
3.1. General methodological problems of personnel support of information security and the development of the content of professional education in this field.
3.1.3. Methodological problems of using modern information technologies for training specialists in the field of information security.
3.1.4. Problems of scientific and educational-methodological support of the system of continuous training in the field of information security.
3.2.1. Problems of organizational support of the training system in the field of information security.
3.3. Problems of technological support for training in the field of information security.
3.3.1. Problems of improving technologies and educational and methodological support for the training process in the field of information security.
3.3.2. Problems of technical and software use of modern information technologies in the educational process.
3.1. General methodological problems of personnel support of information security and the development of the content of professional education in this field.
3.1.3. Methodological problems of using modern information technologies for training specialists in the field of information security.
3.1.4. Problems of scientific and educational-methodological support of the system of continuous training in the field of information security.
3.2.1. Problems of organizational support of the training system in the field of information security.
3.3. Problems of technological support for training in the field of information security.
3.3.1. Problems of improving technologies and educational and methodological support for the training process in the field of information security.
3.3.2. Problems of technical and software use of modern information technologies in the educational process.
Formulation of the problem
In the ideal case, in order to solve the problems mentioned, it is necessary to create a motivation system that includes public policy, the education system, patriotic education and, most importantly, serious funding of all these issues. It is on this path and for the sake of the mentioned money that those who speak on television at various meetings and public councils go.
We (with one of the teachers of the department) tried to solve this problem on our own and with minimal time and financial costs. Naturally, in a separate study group, in a single period of time, without the mentioned preparation and environment, and even 4-5 year students who are already carefully demotivated by the ideological and educational vacuum surrounding them, it seems that it is already impossible to interest students in information security, to make it interesting to them, they wanted to learn and learn.
Together, as it seems to us, we managed to solve the problem, managed to find a form of training that encourages further study of both special and general disciplines.
Refusal to consider all pedagogical (didactic) methods and technologies
In the process of selecting educational (didactic) technology, a huge amount of relevant literature was considered. In addition, this consideration itself, in fact, began long before the task arose and probably lasted a couple of years (at least).
This article will not consider the process of studying, selecting, and actually choosing didactic technologies, nor will they be reviewed. The situation with the generalization of this topic is a separate serious problem, and a separate article on the development of the methodological segment of the educational program on information security will be devoted to this.
An approach
As a pedagogical device, a combination of playing, role-playing and problem-solving didactic technologies was selected that could act as a motivating factor in teaching information security in the existing environment. The discipline on which it was planned to work out the reception is “Information Security Management in an Organization”. It was necessary to develop a model, some level of abstraction, which would:
- was interesting as a game;
- a team the size of a study group could take part in it;
- the duration of the game should not exceed the duration of the training pair (or better, its half),
- informational and educational content of the game must comply with existing regulatory documents on information security;
- the lesson should be maximally visualized, on the one hand, to use the most developed information retrieval systems for students, and on the other hand, to illuminate the issue as voluminously and comprehensively as possible.
At the same time, our programming skills are practically zero, ordering is impossible - due to the lack of funding for such experimental activities (or is complicated and lengthy in the conditions of our grant system).
As tools available were: a computer with standard office software and a projector.
Prototypes
Life has already taught that before you invent a bicycle, you should look around you and look for a ready-made solution. There are about 2 dozen computer games that immerse a player in the world of information security on the market. Worth ( Review ) attention - 2-3. In addition to computer games , there are also real quests ( Cicada 3301: a secret community of hackers or just a game? ), Card games ( Card game “Outsourcer” or “Lokalka. Interrupted sleep of a system administrator” ) and other forms of games.
There are two more games ( Plague Inc. and Bio Inc. ) that are interesting from the point of view of building the game process - “attack-defense”, and which prompted the principle of creating the described technique of motivation.
Unfortunately, all these games (omitting issues of copyright, their availability on the Internet, the impossibility of their purchase due to their relative "old age" or the complexity and duration of purchases by a state organization) are focused on an individual player, in terms of complexity and duration of passage they cannot be used in full-time studies, although it is extremely desirable as an “homework” or “compulsory reading / viewing” element of the educational process.
Igrodel (substantive modeling)
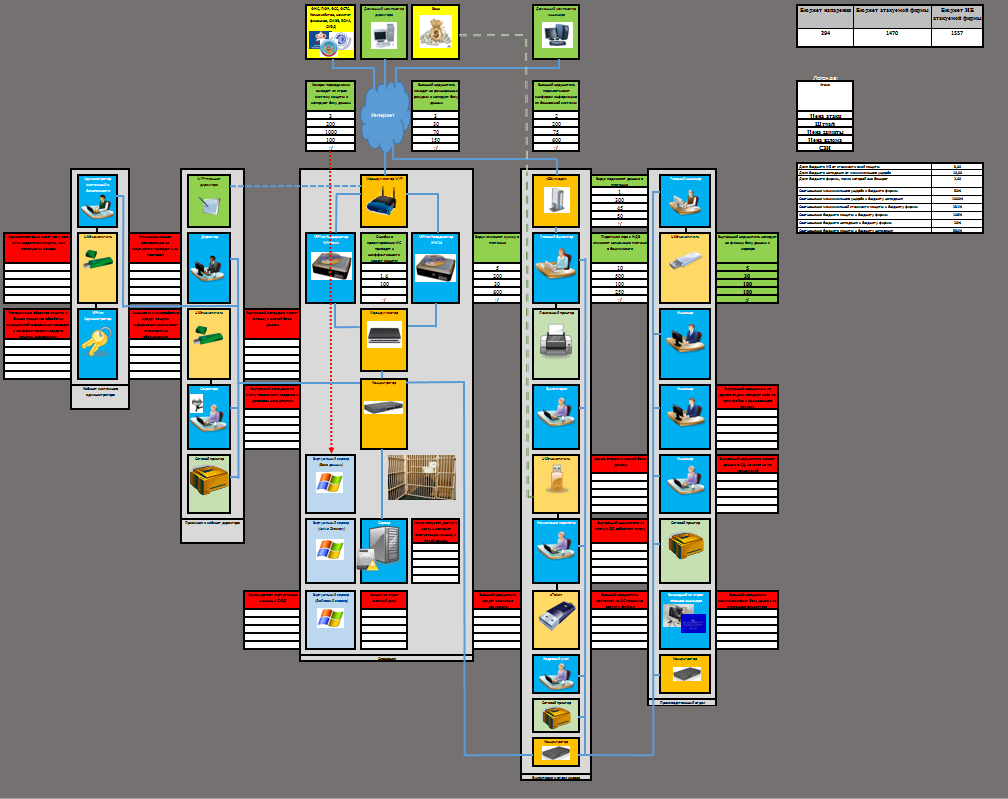
MS Excel was chosen as a modeling tool, a small organization information system (~ 9 workstations and 1 server with virtual machines) as a modeling object, threats modeling, construction and management of an information protection system under financial constraints as an object of study. For maximum compatibility and use on machines with limited rights, it was decided not to use scripts, everything should be modeled using regular Excel capabilities (some of the rules and restrictions in the "Game" are associated with this, for example, reducing or increasing the cost of attacks or SZI are recounted even by already completed attacks and defenses, but since “the world is not perfect”, these restrictions are explained as “inevitable physical laws of the game world”).
The idea of the game was as follows: an attack is carried out on the organization’s information systems (by order of a third party that allocates a budget for the attack, specified as part of future profits), the information security service blocks existing threats by acquiring various means of information protection. Both sides have their own budget, the goal of the attacker is to “ruin” the organization, the goal of the defenders is to prevent this. The organization has some kind of budget, theft of which "bankrupts" it. The game goes on until the parties exhaust their budgets, or until the organization is "ruined".
As the source data were selected:
- FSTEC regulatory document “Basic model of personal data security threats when they are processed in personal data information systems (extract)” ;
- formula for threats of unauthorized access from page 16 of the specified document (threat of unauthorized access: = <source of the threat>, <vulnerability of software or hardware>, <method for implementing the threat>, <target of influence>, <unauthorized access>);
- part of the elements from Figure 3 “Elements of a description of the threats of unauthorized access to information in the ISPD” on page 22 of the specified document;
Threat Description Elements

- Appendix No. 2 to the "Requirements for the protection of information not constituting state secrets contained in state information systems" , approved by 17 order of the FSTEC.
I’ll make a reservation that not everything that was conceived was implemented and brought to the end, for example, it was envisaged that students should collect information on the cost of information protection means themselves, assess the damage done and the “cost” of the attack. This is partially implemented on the first page of the game.
A few more assumptions:
- all SPIs are “independent” and neutralize only one threat;
- the imaginary “Next-Generation NSD” was added, similar to the Next-Generation Firewall, which is a mounted data protection from the NSD level of applications or services;
- The number of vulnerabilities and corresponding threats has been reduced to save time.
The selection of SZI examples was carried out from the register of certified FSTEC and FSB SZI.
Interface Description
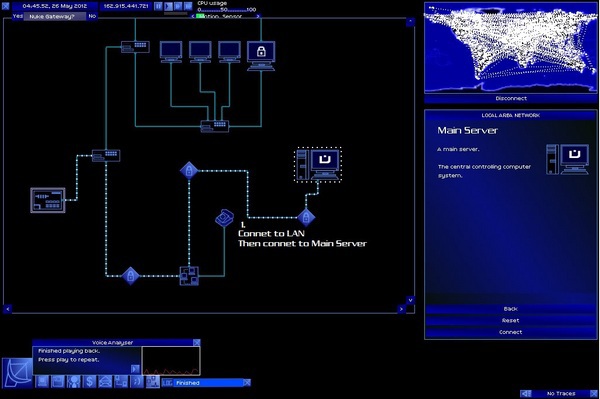
The game ( Zip-archive with the Game ) begins with an introduction to the organization’s information systems, vulnerabilities, possible threats, their implementation methods and information protection tools.
It also provides information on available budgets and some analytical information.
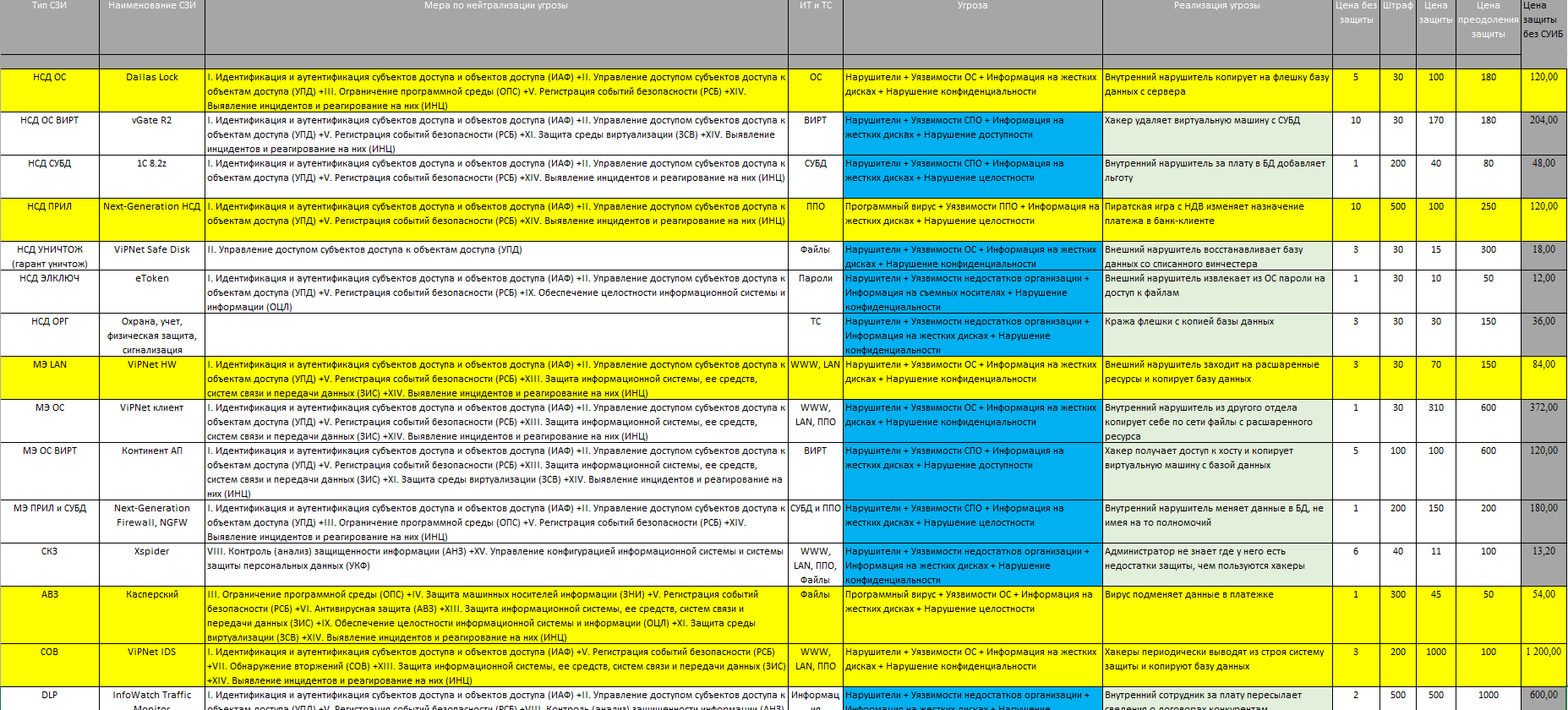
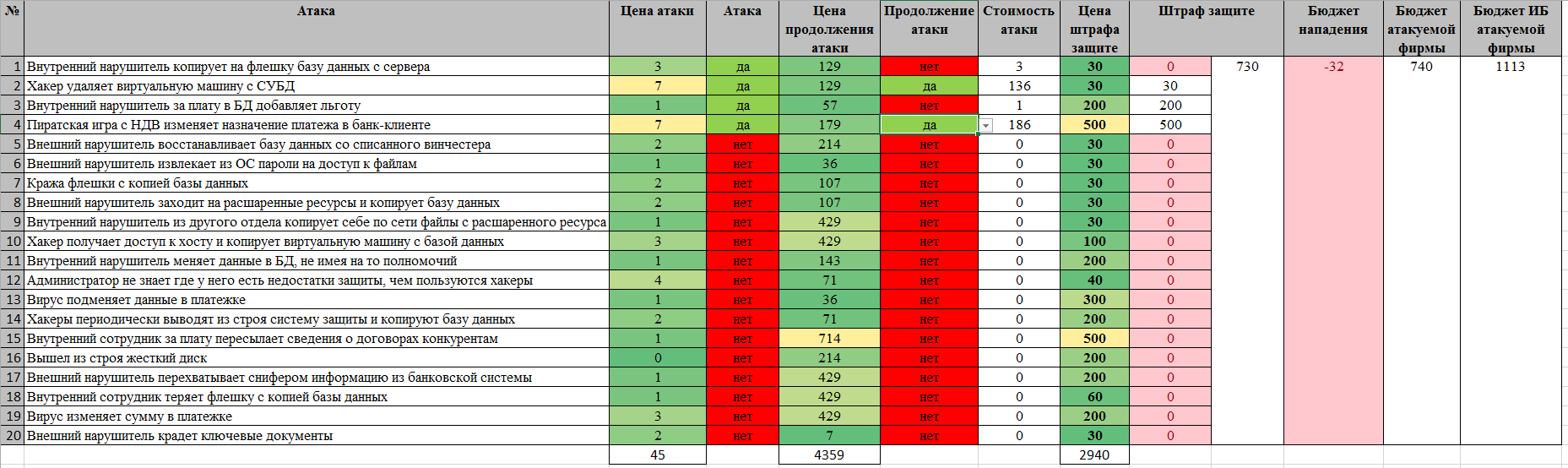
The second tab of the Game shows the types of SZI, examples of real SZI, "measures" according to the 17th order of the FSTEC, objects of attack, threats, methods of their implementation and various costs of attacks and protection.
The third tab shows the information security service interface. The “purchase” of the SPI is carried out by answering the question in the corresponding line. The IS Budget column shows the remaining budget. The column “Damage to the company ...” shows the budget of the organization remaining after the theft.
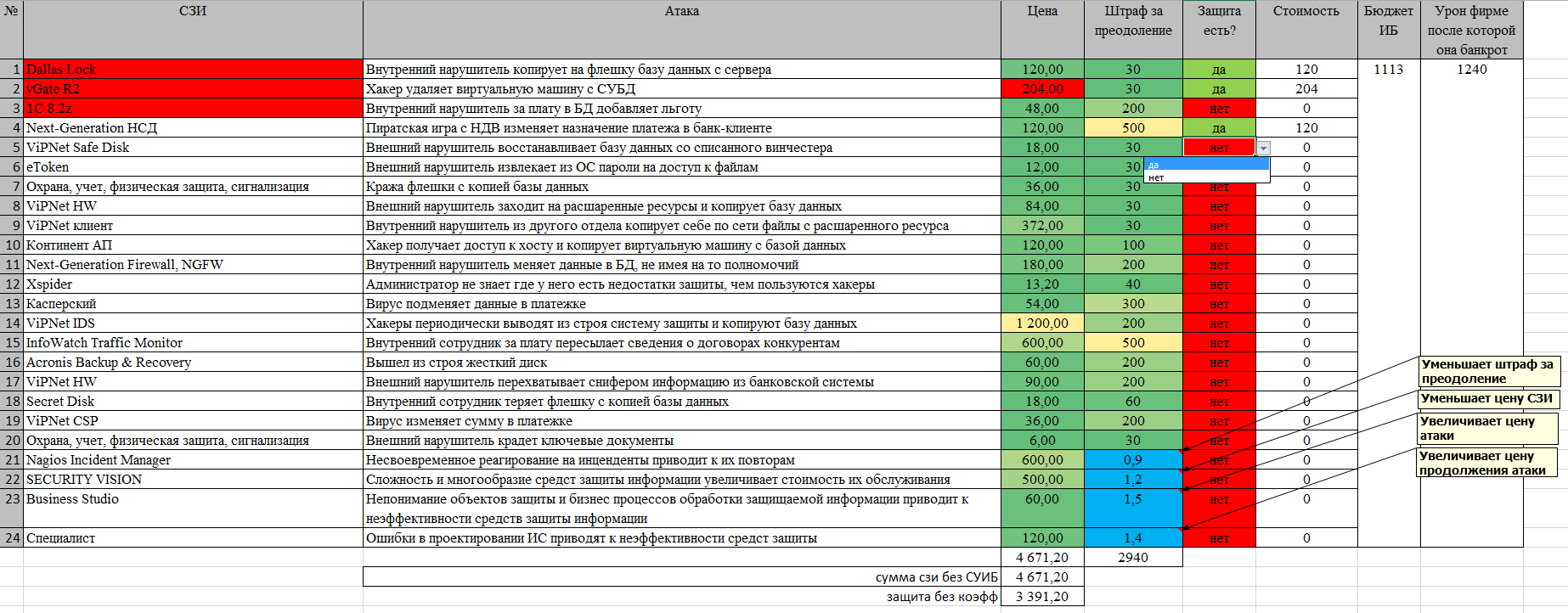
The fourth tab shows the hacker interface. He has the ability to realize the threat, and in case of failure, spend a significant budget and “crack” the defense. Continuing the attack in the event of initial success does not make sense, does not increase damage and meaninglessly increases the cost of the attack. In case of successful implementation of a threat or hacking of protection, the corresponding value of damage appears in the “Penalty to protection” column, the amount of damage increases and the corresponding budgets decrease.
For the convenience of sorting, all prices are highlighted from yellow to green in the direction of decrease.
The interface for each player generally corresponds to the available real information for each of the roles.
All prices are based on various reports and reports about real hacks, my expert assessment and real retail prices of SZI (with some generalizations and divided by 1000). I note that these figures were not selected and not adjusted - after they were entered into the Game, only the ratios of allocated budgets were adjusted.
Examples of losses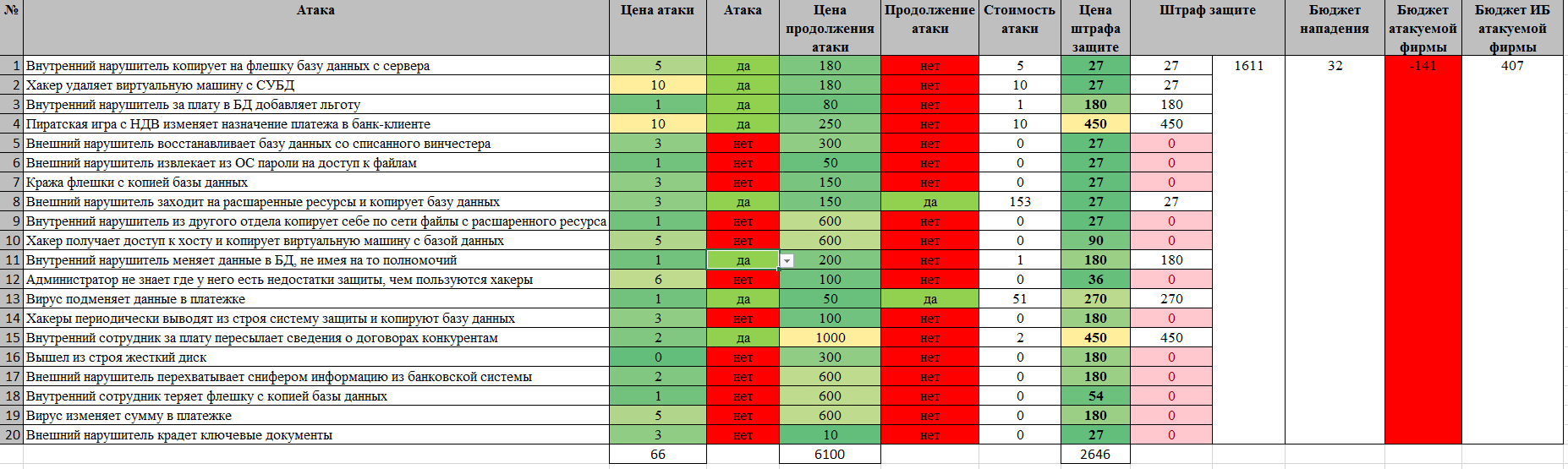
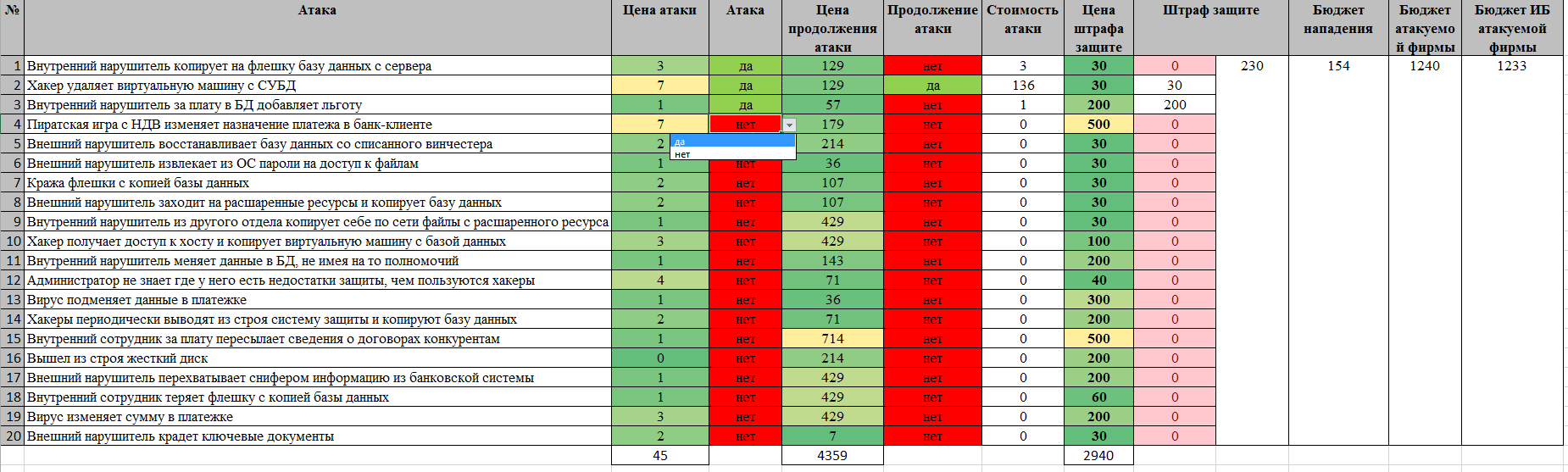
This is how the organization’s loss looks.
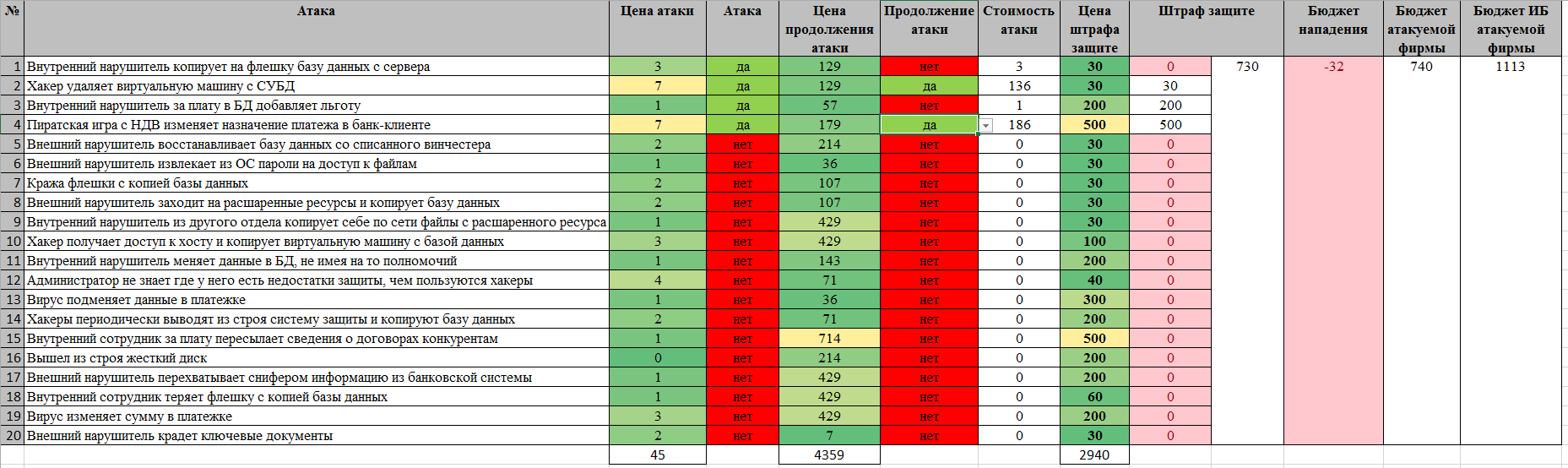
It looks like a losing attacker.
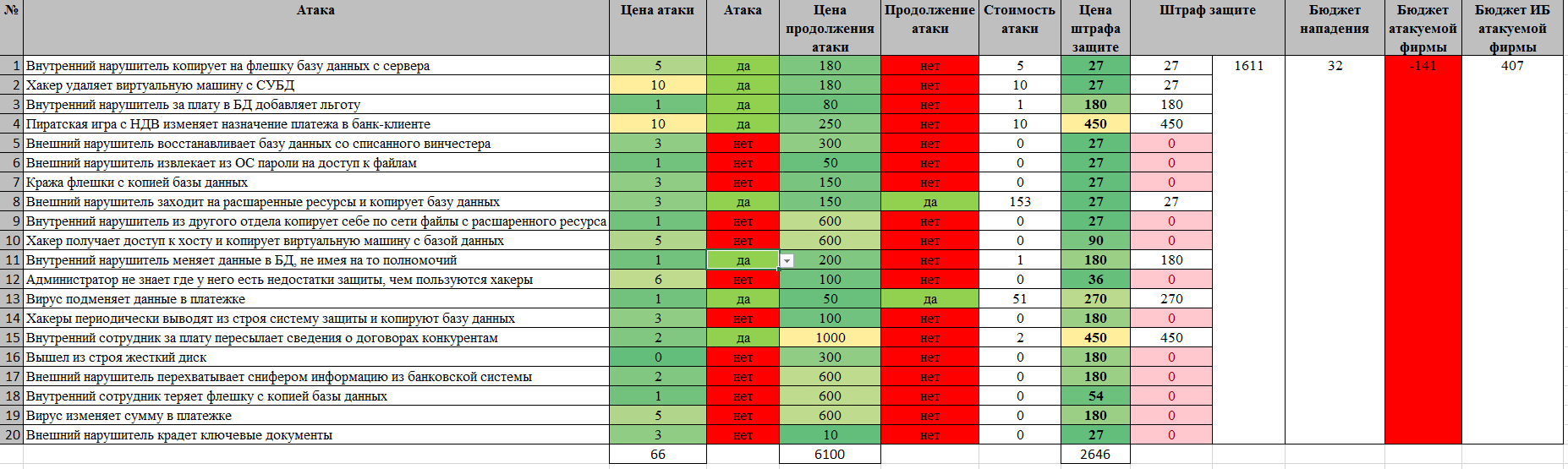
This is how the organization’s loss looks.
It looks like a losing attacker.
Game Rules and Options
There were 2 options for the game:
- the defenders acquire all the SPIs within their budget, after which the attackers try to “ruin” the organization until the victory or exhaustion of their budget (continuation of the attack is not considered a separate move and can be carried out at any time during the attacker's move);
- the defenders acquire 3 SPIs in a row, then the attacker and the defenders take turns one at a time, in case the defenders exhaust the budget, the attacker walks in a row until his budget is won or his budget is exhausted (in this case, a successful attack (SPI is highlighted in red), protection is prohibited on this line) .
In both cases, the attacker should not see the defenders interface.
In a real learning environment, the game was as follows:
- one student playing the role of a “hacker" was chosen;
- the rest of the students played the role of the information security department of the organization, of which the head of the department was selected, whose word was final in determining the next step;
- selection and switching of interfaces was carried out by the teacher;
- the attacker leaves the classroom and the defenders make a defense decision, the teacher makes decisions, switches the interface and calls the attacker;
- the attacker makes his move or moves and, in the second version of the Game, leaves the class again.
According to the results of the game, students must make generalized conclusions, for example, about the presence of very expensive hacks or the ratio of budgets.
results
The involvement in the game was almost one hundred percent. Students, and then really working specialists (for the sake of comparing strategies, we also gave them a play) played with great interest, selected strategies, argued, played in a team, and leaders were determined.
After a large number of games, players have a question about the conclusion of a universal strategy that guarantees a win or a desire to "improve" the Game.
This moment is the key in the transition from the game to training in professional disciplines that allow you to solve the (real) situations modeled by the Game in the best way:
- risk theory;
- game theory;
- Database;
- programming;
- modeling;
- situation modeling
- probability theory;
- theory of information collection and analysis;
- statistics
- metrology;
- microeconomics;
- project and process management.
According to the results of multiple experiments, the selected problem-game technique was recognized as successful and adopted by the teaching staff.
In addition to the indicated application (roles, model, motivation, problem statement, visual demonstration of the complexity and volume of IS tasks), this technique can be used in work on theses or dissertations, including when determining their topics - areas of scientific and practical research.
Applicability of the model in extracurricular activities
The results of using the game have led to several possible non-training situations of its use:
- in the case of developing the Game for a specific information system of a real organization and its complication (increasing the amount of vulnerabilities and threats used), you can get a model that accurately describes the real situation with ensuring information security, which in turn will allow for training (cyber tricks) and simulation testing of the protection system information, assess risks and verify such assessments, justify the budgets of information security departments;
- to conduct comprehensive testing of regulatory documents (for example, an attempt to combine “vulnerabilities” and “attack objects” with “threats,” “threats” with “measures”, and then with their implementation through regulatory requirements for SIS and an attempt to select real SIS to these requirements, showed a real the impossibility of completing this process in its entirety without any simplifications and assumptions that reduce the volume and, therefore, the complexity of the resulting system, and leading to the omission of the methods used in reality for unauthorized access to information).
Game Model Development
And, as usual, I call for the development of the described technique and for writing the Game in "normal" programming languages. Looking ahead, I’ll say that this technique is planned to be used as a problem setting with the transition to the implementation of the indicated scheme of the information system, information protection system and information extraction system in practical and laboratory works in the specialty “Information Security”.
Link to the Zip archive with the Game .
