What is happening in the development of enterprise mobile applications
In 2013, the mobile development market for business was estimated at $ 245 million. In 2016, our market was supposed to be $ 1 billion, but most likely it will be slightly lower due to the situation with the economy and because of sanctions. According to some estimates, this is approximately half of the total mobile development market.
People get used to working with tablets and phones, get used to have access to corporate services in cafes, on the plane, in the car - and employers want employees to be in touch and outside the office. Hence, such a growth direction.
The Russian segment is also a lot of “file improvements”, because turnkey solutions for our big business are not suitable. Plus, the sea of integration with corporate systems zoos, this is also a large share of development. At the same time, half of production companies, retailers and state organizations in Russia do not have their own applications today. An example of a complex application is here .
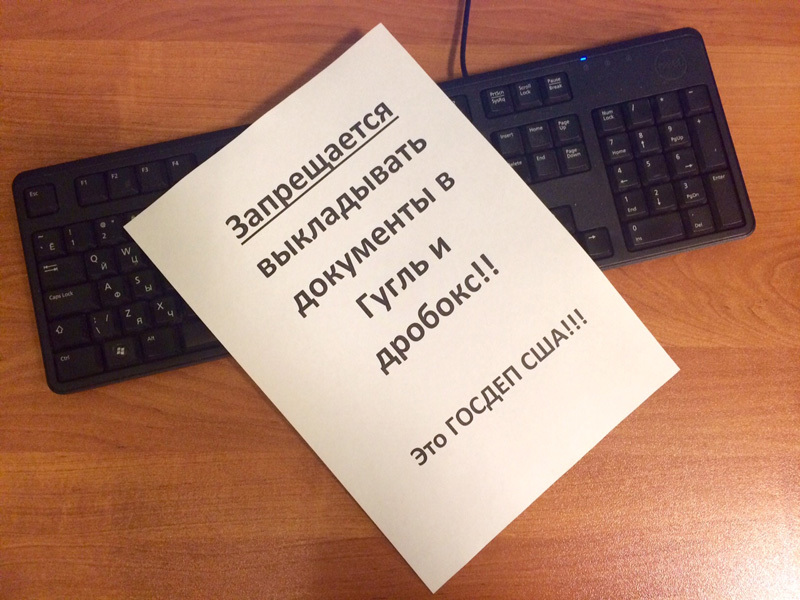
Below is a more technical overview of the situation and a series of rakes. Starting with such obvious ones as the fact that if you are involved in nuclear energy, you probably should not do document storage through Google.Drive.
Why do you need these business applications so dramatically?
In 2013, the share of office employees using phones and tablets in the case exceeded 50%. And the leaders suddenly realized that when a person has a telephone with him, then:
- He can work 24 hours a day, because he has a telephone with him, and if something is urgently needed, he will answer;
- Man himself, voluntarily, was hung with sensors, in particular, of geo-position;
- It is better to be able to control corporate data on the phone than not to have it;
- Anyway, he will get into the network for important documents from the phone, so it's better to protect this exchange.
The first signs were remote workstations such as terminals “punching through the base” of rights by the traffic police and terminals for checking passports of the Ministry of Internal Affairs. Then the business connected with logistics joined in - at first they started tracking trucks, and then full-fledged applications for couriers and merchandisers appeared. For example, a courier delivers an order, he notes in the application that the order has been delivered. If the client begins to say that there is no order, you can check the courier track by GPS.
Now we already see that the workplace is three screens. Desktop, tablet and phone. The exchange of information does not stop. If before the office was limited to the perimeter of the LAN, now everything has begun to change dramatically.
Of course, not all office workers need mobility.Bookkeeping will work for a long time from the desktop. On the other hand, couriers, traveling employees and tops have long and firmly settled on tablets and phones. They were quickly joined by lawyers, insurance agents and other people who need a database on hand or some kind of sophisticated calculator.
Naturally, employees are not always happy. For example, the adored feature for Android phones is a remote wipe in case of dismissal. If Blackberry has a well-defined corporate memory and regular user memory (and the counterparty’s contact cannot be transferred from one to another, for example), then other OSs are still growing up to that.
Employers are happy, of course. You can write a letter or coordinate a document already outside of working hours. Personal time? No, not heard. In the USA, for example, they’re doing strange things with mobile apps. For example, they check that the employee really went on a business trip and really stayed at the hotel where he brought the documents from. Or here roaming is paid only during working hours.
But, of course, epic failures happen with misunderstanding. Mobilization requires additional costs for the security of corporate resources. First you need to protect the internal Wi-Fi network, then implement microVPN for remote connections, then think about MDM systems to manage profiles and application / certificate updates, lock and wipe stolen devices, and so on.
Another important point of implementation is that the workflow needs to be protected, and more often than educating people, it’s easier to pick up applications that they themselves can do and VPN, and everything else. Before that, for example, there were cases when employees did not read the license of the same Google about the fact that as soon as you upload a document there, it’s not necessary to complain that it is no longer yours. The security guards have already realized that you still can’t take the phones away, and they are forced to love mobile workflows for security. The same SAP is like a "foreign aggressor", but it seems to have passed FSTEC certification that they do not have bookmarks. In Russia, in general, there are only a few companies that are trying in this direction (below), so there’s no one to choose from.
Where do these applications go?
Sometimes a company buys iron itself and distributes it to employees. The brightest example is Russian Railways with their “bulletproof” smartphone, on which you can drop a brick.
The second option is industrial devices, for example, tablets, which are tightly welded to the machines or, in general, are their integral part.
The third option is personal devices, this is the so-called BYOD concept.
Let's go through each one. In BYOD, it is tempting that using employees ’smartphones seems to be cheap; you don’t have to buy anything. But you need to maintain a whole zoo of axes and iron, plus you need to constantly think about security. Both iOS and Android are developing in the direction of supporting special workspaces that are separate from user-defined personal ones, but so far the most cunning can do anything on their devices. Although, of course, Android 5.0 has taken a big step towards business users, in particular, built-in encryption has appeared. It’s very important for BYOD to have expensive and multifunctional Enterprise Mobile Management class solutions (this is MDM + MAM + MIM), that is, centralized application management, VPN access for mobile devices, software updates, rolling policies, and so on.
In the case of their corporate devices, you can provide much tighter control over the data. For example, there is even a domestic development, shaitan-brick, which runs on its own special Linux without any extra kit. They are going to undergo full certification so that the shaitan brick is available for government agencies. I have already seen the device live (with an incomplete set of software) and I can say that most of all it pleases 70–80 hours of constant work. I mean - 3 days without charging simply due to the lack of a bunch of background processes such as caching media files, pushes, and so on.
Russian solutions
Here is a list of domestic and open source vendors:
- CDC Group of Companies - delivers Russian-made software products developed on the basis of the OPTIMUM technological platform, which allows you to create multifunctional solutions for automating the work of mobile personnel and connect additional modules as needed. CDC customers include more than 4,500 companies, most of which are leaders in the Russian market.
- NIIS OKB - Russian MDM, the product is called SafePhone PLUS .
- WSO2 Enterprise Mobility Manager - open source MDM.
- Openmeap is an open source map that is used a lot where.
If you have something to add - write in the comments.
Alternatives to the application
An alternative to a mobile application is either terminal access to the "large" desktop version (I even know people who use 1C: Enterprise from phones this way), or the web face of the same application.
The problems are obvious:
- Browsers are not optimized enough to provide performance in remote complex applications. In the application, the same code, for example, responsible for rendering dozens of fields, executes much faster. Over time, this gap between the hardware purchased for the company and web technologies widens, and it becomes harder and harder to work. On the other hand, applications optimized even for the oldest models of tablets and phones are commonplace. Response time is one of the main indicators of the usability of the application for practical tasks.
- In case of terminal or web access, it will not work offline. You can work with the mobile application at any time, and as soon as synchronization occurs, the data will go to the system. This is very convenient for those who travel a lot or often run to the workshop, for example. Loss of communication does not become a disaster and does not lead to data loss.
- Providing terminal access to the internal corporate environment from mobile devices is a special task. In practice, no one will adjust the interface for the device, think about the convenience of the user. Only a laptop will work conveniently.
- A mobile application can be installed not only on a smartphone or tablet, but also on industrial devices that, in principle, cannot or are extremely inconvenient to connect to a web environment. For example, there is an application for managing the maintenance and repair of equipment in industrial enterprises. Often, special devices do not contain a browser at all, like the same courier reader.
- Terminal access, relatively speaking, provides the ability to access the “picture with buttons” and does not make it possible to fully utilize the functionality of the mobile device. For example, insurers can photograph dents on cars and immediately transfer them to the office using a mobile application. With web or terminal access, this cannot be done as quickly. They also have a photo check in the same application, implying that there were no image modifications in the gap between the camera and the application.
- Another example is a mobile version of a company’s website with sales. You can just make a mobile layout of the site, or you can use a separate application with the ability to log in to your account, automatically track your location, upload a photo of your personal profile, link a phone number for SMS alerts, and more. As a rule, for many regular customers or counterparties the application is more convenient for you. From a commercial point of view, PUSH alerts are an opportunity to keep up to date with regard to promotions in stores, taking into account the geo-location.
- In the case of terminal access, data transfer from one IT tool to another is difficult. For example, in the case of a mobile application, you can create or edit a document in the Office, upload it to the application and send it back, or you can simply upload something to a mobile device and save it.
There was an example when manufacturers could not work through web access at all: there is no 500 megabyte cache, no offline.
Implementation experience, bulk facts
- The magical product SAP Mobile Documents has recently appeared. This is a native application that allows you to work with documents from various sources and their functionality, for example, the check-in | out mechanism. Also organized mechanisms for the safe operation and storage of these files, for example, the life of a folder, a document, restrictions on actions with a document: reading, downloading, printing, deleting, and so on. This thing has a web and desktop version. It is still very fresh now, but many people already like it. We have one big introduction. It is especially nice that he knows how to connect out of the box to the same Sharepoint 2010 and sap services. While the product is fresh, the vendor often issues licenses with it for its MDM. But, of course, mistakes are climbing. For example, during test trials we caught a bug that the files posted from the Windows client Cannot be taken offline for collaboration on iOS. SAP rules, of course.
- Samsung advertised a new piece of hardware and came to visit with it, there is a solution only for corporate customers. If you need a super-secure system, you need to look towards Tizen (z3, OS Tizen 2.4.0.1) - you won’t dig in there, it is certified in the Russian Federation that there are no bookmarks, and now it is collecting documents for the second management certification. They generally have their own applications, and they all, in turn, sign and certify: a device and a disk with a checksum, even like that. Each individual device receives its own set of documents. But this is completely for the defense departments. According to Samsung, you can broadcast applications with Android, or you can write in native C ++ or make hybrid applications. They promise to give source codes to everyone who uses it.
- One of the funniest paperwork rakes is that some customers introduce document encryption RAR encryption in their corporate policies. There, employees think that they took the document, sawed it in the archive, and it is protected. Or put passwords on the XLS. The problem is that all this is the good old “123456” and, in general, everything that is sorted out with a dictionary or brute in half an hour. The same goes for Wi-Fi - open at a time. During the last audit, it turned out that the accountant was closing all of her documents with the same Vera2015 password. So beware of people with powerful graphics cards on laptops.
- The good old mistake is to take a student to write an application inside the company. Without a background, he will definitely leave a hole. Then it will be found (not immediately, at first a critical mass of leaks for the scandal will accumulate), and still you will have to rewrite everything. Another common mistake - as soon as the new iOS comes out, everything immediately falls off. Android is not so aggressive in terms of updates (“There is a hole in 4.4, if you want it, update it,” plus the company may not release an update; mostly top devices and devices from Google are guaranteed to be updated for 2-3 years), but not updating iOS for the end user - a tragedy. Although it is always clear in advance what will happen, but no one itches. The story is that pros roughly understand what will happen tomorrow, and do not do what works right now.
- Another point in devices - software requirements are different. The phone three years ago does not cope with everything. Somehow we bought Chinese devices in one company, we decided to save specifically. There were enough problems for the full program. It began with the fact that the Chinese firmware does not work as it should. Then it turned out that it was no chance to check what was inside. Then 1000 pieces of iron began to slow down - they were “littering” with the vital products of applications, somewhere they went beyond the specification, somewhere the Chinese changed the composition of iron a bit within the party ...
- Once there was a funny story in the workplace. They gave us an administrator who doesn’t burn in SQL. Generally. We ask: is he the main system administrator? Yes, they say the oldest. We ask: what is his experience, are there any certificates? Yes, they say, now the eychars will send. Eycharas and send: "Master of telephone etiquette."
- It happens that people themselves knock right at the vendor. The story is this: they come, then they dance beautifully. A company buys a base product. Licenses are sold, the vendor leaves - that's it, the deal is closed. And then it turns out that you need to customize. The same MS Sharepoint is often implemented on the type of "yes, cool, work - and what to do next?". Despondency begins. It is also necessary to finish it for the company, then give a methodology for use, put in a process, explain what and how to do. At one customer there was not even an IS regulation - they say, recommend how to do it better. Many times I saw how MS Project Server, without a proper understanding of what to do in business practice with it, was simply being implemented in vain.
- Very often the reason for the introduction is the phrase "These have, I also want." The concept of using mobile devices - almost no one in the Russian Federation. They don’t even think about it. What for? We need a system, then we will write the concept as it will be. In fact, you need to understand why and how you are going to use it. And not just because Petrovich has it.
- Once the customer says: “Let's have a super-fault-tolerant system, critical data inside.” We count the cluster, then show, and already in the smoking room it turns out that exactly 8 people will work there for a couple of years. Architecture, a lot of time, scaling calculations ... And just copy virtual machines. They have downtime that fits into what can be deployed in the same period.
It is specific that iron on such projects has recently become less, because it has become more expensive in dollars. Sometimes it works when there are a lot of different products on one piece of iron. But this is not always good. It’s better to save hardware on not making a failover cluster - it’s better to solve it by virtualization and fast backup. Many generally look into our cloud. They used to shun it, but now it begins: “Or maybe rent?” Especially those who earn in rubles.
Much can be done in general on open source or free software. The same balancers- you are welcome. Above MDM is open. It is clear that all the same money will be spent on implementation. It is clear that when taking a free product, you need to take technical support of this free open source product for a year or at least six months for implementation. And immediately think: wouldn’t it be necessary then for a couple of Javists to serve all this?
Process: how best to implement
- First you need to write a concept or other similar document - which pieces of iron and for what exactly will be used. What data and where will be available. What can, what cannot be entered on mobile and so on.
- Evaluate budgets and the need for such an implementation in general - that is, rationally relate to the issue. Evaluate open source options and their costs (including completion and support). If not open source, understand domestic or western vendor.
- Understand architecture and immediately lay down the scaling.
- Once again, consult with the pros already on a commercial basis. And not to those who made the elections above. Two looks are better than one.
Actually, at the first stage, all this can suddenly turn into a web face. Or in an application that contains web view and VPN pribluda.
Sometimes it happens what is needed exactly, but how and why - they did not think. I must say that the bank can write the concept itself, but the mining and processing plant is far from always. This is simply not its specificity. There are companies where the rake has already been stepped on, and there are - where the words “scaling” and “data protection on mobile devices” have yet to be learned. Often, the CIO will still think about mobile workstations, the only question is how and when. In this case, it’s convenient to look at the practices of the Western market: ours is catching up anyway, it’s one year faster than in Moscow and one and a half faster than in the Urals (excuse me).
In recent years, things that had to fit into the existing channels have changed, and now they are good in large cities everywhere.
References
- Application for a large manufacturing company
- Open source for telecommunications
- My mail: EvSmirnov@croc.ru.
