Your Anonymous Secret Publications Still Not Anonymous
- Transfer
The “white hacker” Ben Caudill had already finished eating his sandwich by half, when he casually reached for his iPhone, swiped his finger on the screen several times, and then handed it to me with the words “Did you write this?”
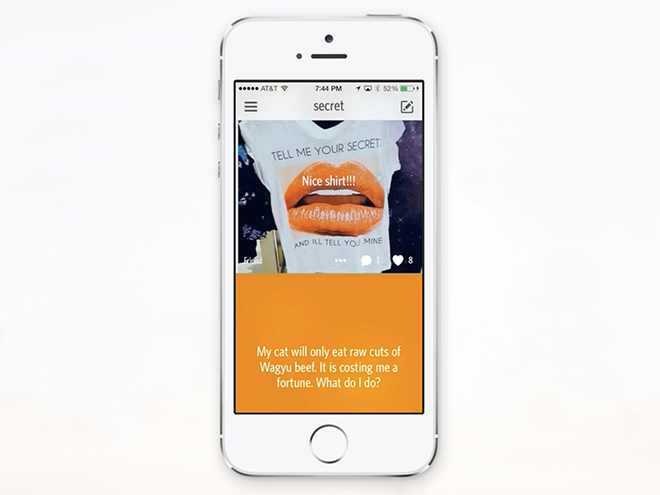
Yes, I wrote it but no one should have known about it. He showed me one of my posts in Secret, a popular application that allows you to anonymously share the most secret secrets with your friends, I repeat - no one will know that the secret belongs to you. A few minutes ago I gave Caudill my email address and that was all he needed to discover my secret while eating a sandwich in the midst of a leisurely dinner in Palo Alto.
Frankly speaking, my secret was rather boring, but the general flow in Secret consists of rather sharp and frivolous messages - rumors from Silicon Valley or deeply personal confessions like: “He made me an offer, but I was forced to refuse. I thought it was "a matter of life," but my heart is now broken. " At that moment, Caudill could enter the email address or phone number of any Secret user and read his secrets.
 The author’s secret: at heart I really like only one Tim Burton movie
The author’s secret: at heart I really like only one Tim Burton movieSecret users are lucky that Caudill is one of the “good guys”. He is co-founder of Rhino Security Labs , a small Seattle-based information security firm. The co-founder of the company and the head of its technical department, as well as the co-author of the hack, previously known for his manipulations with Google Maps, Bryan Seely, by the time we had lunch with Ben, had already passed on the information about their hack to the CEO of Secret. Hackers hope to receive a reward in accordance with the Secret program for catching bugs, which has been around for six months. Both hackers say they restrained their desire to get into other people's secrets.
Earlier this week [The original article was published on 08/22/14, - approx. translator ] in an interview with WIRED, Secret Director General David Byttow confirmed the existence of such a vulnerability and added that the staff had already fixed it and began to analyze the causes of its occurrence. “As far as we can tell, no one has exploited the vulnerability in any meaningful way,” says Bittov. “But we are obliged to take measures and precisely determine its causes.”
Surprisingly, for Secret, this has already become commonplace. Since the company launched a bug-catching program in February, thanks to the finds of 38 “white hackers”, 42 security problems were fixed. Given the degree of confidentiality of some secrets, such an iterative approach may seem inappropriate. However, Bittov claims that identifying so many errors proves the effectiveness of the system.
“Since hackers find this kind of vulnerability through our HackerOne bounty program , we are moving further and further forward,” says Bittov. “We have not had a single public incident regarding security and privacy. All exposed unprotected spots were found thanks to our bug trapping program. ”
 Rhino Security Lab co-
Rhino Security Lab co-founder Benjamin Caudill Caudill and Seeley appreciate the speed and kindness of Secret's reaction to their discovery. But it is difficult not to take this case as a warning regarding other applications that are trying to speculate with a human desire to remain anonymous and maintain privacy on social networks. There are many such applications, among them: Whisper, Yik Yak, here you can also include the Snapchat application - a service that allows you to send friends photos that are automatically deleted a few seconds after viewing. Snapchat signed an agreement in Maywith the US Federal Trade Commission (FTC), which accused the creators of the application of exaggerating security promises of sending “disappearing” photos. As it turned out (which was quite expected), the recipient could save any photo using a third-party client program or by taking a screenshot. Snapchat owners have pledged to provide more honest information about the capabilities of their service and agreed to another condition: for the next 20 years, the application will be supervised by experts from FTC.
The trick with the Snapchat application is quite simple, as well as in Secret - the hacking method immediately becomes clear and obvious as soon as you understand what the point is.
To hide the identities of its users, Secret usesthe anonymity that arises thanks to the crowd. When you first install Secret, you cannot see a single post from your social environment until you give the application access to your phone’s contact list. Then the application correlates the email addresses and phone numbers of people from the list with the data of current Secret users, only after that you can follow their updates. (For the same purpose, you can give the application access to your Facebook profile, although this path is well protected from hacker attacks).
To see the anonymous secrets of your friends, you must be subscribed to at least seven users. Even in this case, you won’t know for sure which of your contacts uses Secret: for example, there are 500 people in your contact list, 30 of them are users of the application, but it is not known which of the 500 people are included in these 30. A tidy secret published in application by your "friend", can belong to any of 500 people.
The fact is that you yourself control the list of your contacts. This is precisely what Caudill and Sealy took advantage of for their purpose.
 Rhino Security Lab co-founder Brian Seeley
Rhino Security Lab co-founder Brian SeeleyThe first thing that Caudill did was to create some fake accounts in the app. This is easy, because you do not have to confirm your email address or phone number to register with Secret. For the sake of his experiments, Caudill wrote a simple script to create 50 accounts, but to overcome the threshold for viewing secrets, he needed only seven.
Then he deleted all the contacts from the list on his iPhone, and instead of them added seven fake addresses. Then he added another contact, the email address of the person whose secrets he wanted to see - me.
Then he started a new profile and synchronized his contacts. Now he has a new empty account, and the contact list includes only eight profiles: seven bots, which he manages, and mine. Thus, it is easy to guess that any secret that was allegedly published by one of his “friends” belongs to me.
After Caudill showed me my own secrets, published in the app, he moved on to the next victim: Secret CEO David Bittov. To prove the effectiveness of the application concept, he gave the hackers his phone number and email address to try to gain access to the secret he published. I followed every step that Caudill went through on his iPhone, and soon we revealed the secret of Mr. Bittov. It turned out that he was talking about a pet: “Isn’t it, Lucy is the cutest dog in the world?”
 This method works only in one direction: if you know someone’s email address, you will be able to learn the secrets of this person, but knowing the secret, you You won’t be able to identify its author.
This method works only in one direction: if you know someone’s email address, you will be able to learn the secrets of this person, but knowing the secret, you You won’t be able to identify its author.Bitt reports that the hacking form that Caudill and Seeley discovered is not new to Secret. In May, hackers from Russia, using several mobile phones and a full pocket of SIM cards to create fake accounts, did the same trick. Since then, the Secret development team has created and constantly improved algorithms for detecting bots and other suspicious activity. When the system finds an anomaly, it begins to automatically hide messages or purposefully give vague information regarding the sources of secrets, for example: “friend” becomes “friend of friend” or just someone “from your environment”.
According to Mr. Bittov, over the past few weeks, while the company was expanding its infrastructure, there were times when the bot detection system for some reason did not work, which allowed Caudill and Seeley to crack the application in the same way.
Because of this, it seems that the company operates in a startup mode: it experiments, learns from its mistakes, boldly tries something new, and fails. “The idea that we are trying to convey to users is that to be anonymous does not mean to be someone that cannot be tracked down,” explains Bittov. "Secret is not a place for illegal actions, terrorist threats or the exchange of ambiguous images ... We do not promise you constant security and absolute anonymity."
Thus, the question arises: is the application safe enough for the purpose for which it is used? This is clearly not the case. I choose one of the secrets on the main page of the service and read it out to Mr. Bittov on the phone: “At work I am being burdened with more and more responsibility. And I silently fight mental illness. ” Is the Secret app safe enough to keep this user anonymous?
He asks me a counter question. If there were no applications like Secret, where would this person go to take his soul? Where could he share his struggle with mental illness? On Facebook? Do not make me laugh.
“Our job is to make sure that people feel safe and maintain self-confidence,” Bittov continues. “People cannot share this on Facebook. This is our mission: people can write different things here and not feel lonely. It is very important".
Hacker Caudill is skeptical about achieving such a double goal. He doubts the possibility of communication while maintaining anonymity.
“To some extent, I understand what this is all about. They try to be something like WikiLeaks, but for everyone. However, in reality this does not quite work, ”adds Caudill. “You can’t communicate with your friends, be socially active and at the same time remain anonymous. "I can’t imagine a situation in which a man, chasing two rabbits, would catch both."
