What is the danger of smart grids

Electricity is getting more expensive, and the global economy is looking hard to find ways to increase its energy efficiency. In addition to solar and wind turbines, active construction of “smart” power distribution networks, the so-called Smart Grid, is underway around the world, which allows the efficient use of energy. They are usually automated and connected to the Internet, which causes a natural interest in their level of security.
Attention! All vulnerabilities described in the article were transferred to manufacturers and eliminated by them, but can occur in existing systems
What are they made of?
Smart Grid technology is just getting ready to conquer the world. Now they are used mainly in home automatic climate control systems, where the simplest elements of “smart” power grids are being introduced. Such devices allow the end user to monitor, efficiently use wind and solar energy, and in their absence, switch to other sources. Are smart grids dangerous for progressive homeowners? To answer this question, you need to find out what control components such networks consist of.
In 2013, China invested $ 4.3 billion in Smart Grid, and global investments amounted to $ 14.9 billion. According to Pike Research, more than $ 46 billion will be spent on the transition to this technology by 2015, not only economists support it, but and environmentalists. At Greenpeace, for example, they are confident that Smart Grid networks will save the planet.
Fingerprint utilities send requests to a remote host in order to determine whether it belongs to a particular family. From the response to the request, you can determine the operating system or find out the modification of the device.
After a short fingerprint study, we found on the Internet traces of embedded systems of at least nine different manufacturers, on the basis of which Smart-Grid systems are built.
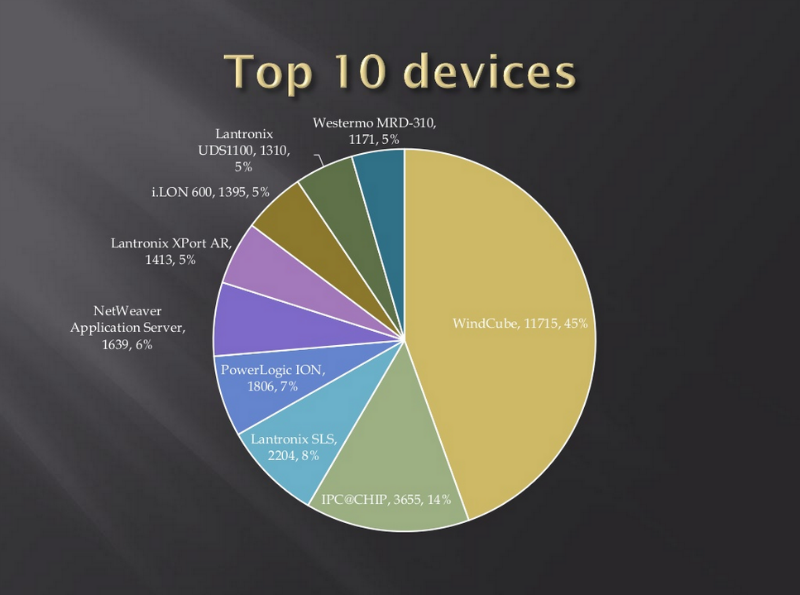
Statistics on Smart-Grid microcontrollers
The most common family turned out to be WindCube, but as a testing ground for experiments were chosen more “intelligent” devices of another manufacturer, in the online catalog of which there is a controller with many promising features: PowerPC processor, RTOS real-time operating system, built-in web server, support for FTP, Telnet, SSH, TCP / IP, HTTP, PPP.
We are looking for the smartest
The Internet search for Smart-Grid systems based on the selected controllers did not cause much difficulty. Thanks again to the official website of the manufacturer, which indicates the name of the operating system and instructions are posted according to which the owner of the device can view the configuration settings of the device at ..... / ZZZ . After that, we went to Google, where we used the inurl modifier, which allows us to search for information in the subdirectories of the site, and entered a combination of the OS and ZZZ names. As a result, we got several pages with IP addresses, subnet masks and serial numbers of specific devices. But what systems do these microcomputers work with?
Dorks are keywords, URLs, or their components, which allow you to use the search engines or web crawlers to find the path to the admin panel or to the error page.
As it turned out on one of the detected pages, the platform under study is working, in particular, as part of the monitoring systems of solar-log photovoltaic installations, which have been extremely common. According to the developer, in the world there are more than 200 thousand solar power stations and almost 1 million inverters connected to the web server of this company.

Solar panels connected to the Solar-Log web server
We disassemble the firmware
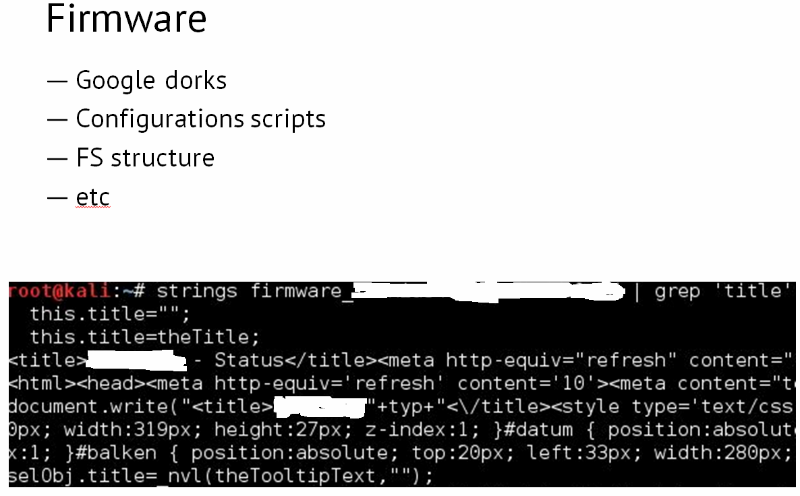
Firmware “
cutaway” After downloading firmware for Solar-Log systems, we looked at how its file structure looked, looked for “dorks” (Google dorks) and configuration scripts that allow you to control the system. Using the strings and grep commands, the Solar-Log Client header was found in the firmware, which prompted the idea to google the inurl URL: Solar-Log-Client. As a result, we found many private user systems and pages with data on the energy consumption of various Smart-Grid-systems from Solar-Log. But this information may be of interest only to supervisory authorities, but not to an attacker.

Solar-Log Power Generation Data for Various Smart-Grid Systems
It is possible without a password
More curious things were found in the admin panel. When studying the Solar-Log Admins, an interesting fact emerged: approximately 5% of the systems did not require a password to enter the configuration page. The remaining 95% of the systems had a password set, but it was of little use. Having formed a simple request to one configuration script, you could make the Solar-Log admin panel calmly give a backup copy of the configuration, upload it to your local computer and extract the password.
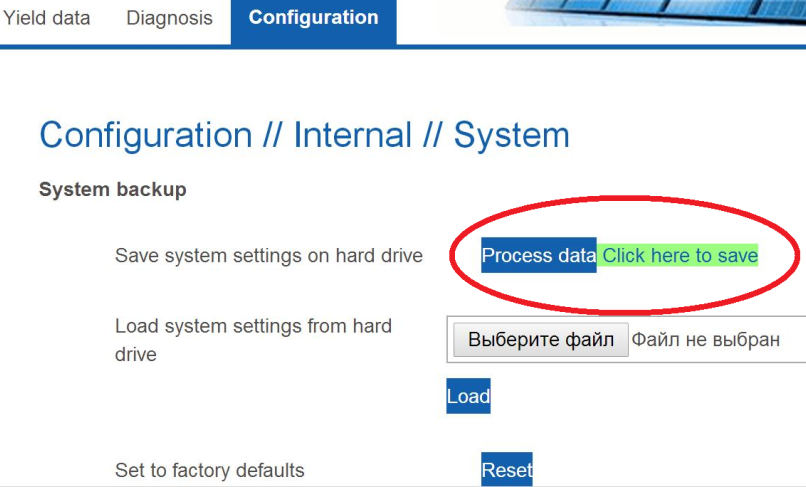
Admin panel
With the decryption of the password, which was always under the index 222, there were some difficulties. The HEX editor gave out some rubbish, so we went the opposite way: we looked at the device that had no password, entered an arbitrary password (1234567890), saved it, then downloaded the configuration file and looked at how it looks in encrypted form.

Backup copy of the configuration file
In the same way, you can make a list of all required passwords matching their encrypted options.
Move on
Getting to the Solar-Log configuration page, as you might have noticed, was quite easy. The device firmware download is available from this page, where you can search for interesting artifacts. By the way, the official documentation states that the firmware update process is password protected. However, we were faced with the need to enter the password only on one of the systems, and it was very simple, coincided with the username and was not available for change to the ordinary user.
What tomorrow?
Users of “smart homes” and mini-offices connected to alternative energy sources are, in fact, beta testers of Smart Grid systems. And the developers do not spare the thrifty owners too much, making serious mistakes in the protection mechanisms. In our case, anyone could choose one of hundreds of thousands of Solar-Log Smart Grid installation owners on the Internet, bypass authorization (sometimes it is also not required), remotely install defective firmware, gain access to control system parameters, and penetrate other network segments. Physical effects are possible, up to the incapacitation of inverters, fire and other unpleasant events.
If the power supply networks of critical facilities are intellectualized with the same haste, the level of risk may not be lower than in the case of SCADA systems, and the plot, when cybercriminals use a computer to disconnect the whole city from the mains, will become quite realistic.
Author: Artyom Chaykin
