Expert hacking landing on PHDays IV: making keys to locked doors, breaking browsers and escaping from the “smart home”

Why is the Internet of things a threat to national security? What is impression? How to find a zero-day vulnerability in applications with circulation of hundreds of millions of copies? Is there a panacea for DDoS attacks? We present to your attention a new portion of the speeches that will be delivered at the Positive Hack Days IV international forum (see also the 1st and 2nd announcements).
About 2,000 practical security experts will gather in Moscow on May 21 and 22, 2014, to talk about the cyber potential of Iran, China and the DPRK, cryptography after Snowden and Heartbleed, raising awareness of Yandex employees in information security issues, important findings of the SCADA Strangelove group, cyber threats for modern electrical substation, the main directions of attacks on SAP systems. Forum guests will learn about next generation compromise indicators, visual analytics in information security, reverse engineering automation, and much more.
In total, the PHDays IV program has planned more than 40 reports , sections and round tables (we will discuss the latter separately), master classes and short fascinating FastTrack stand-ups .
Do-it-yourself practical tasks
Positive Hack Days workshops are usually focused on maximum attention. Hands-on Labs at PHDays are practical exercises, for participation in which you need, as a rule, to have only basic training, a craving for new knowledge - and usually also a laptop.
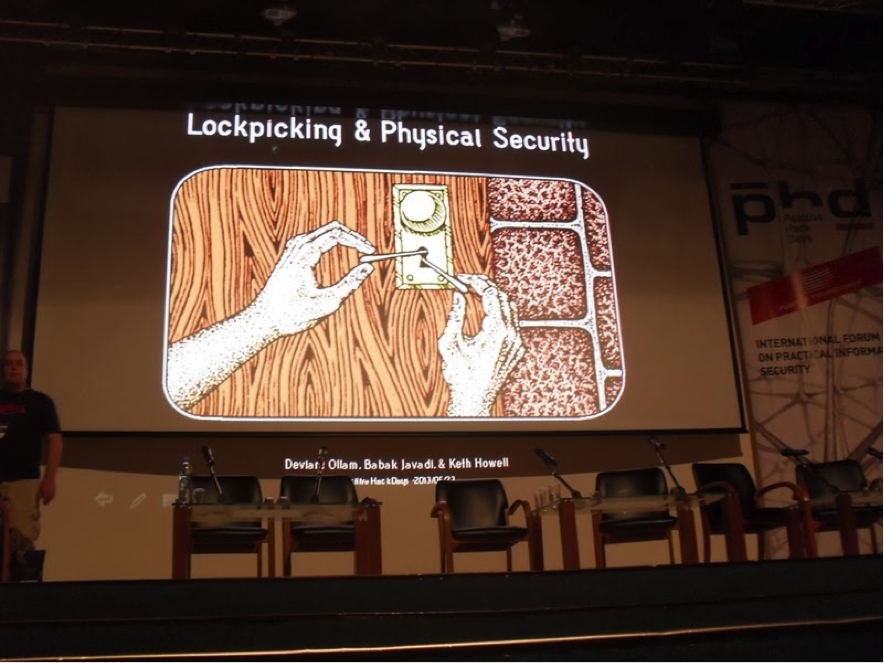
The traditional full house on the site is caused, in particular, by the performance of three Houdini from TOOOL (Deviant Ollam, Babak Javadi and Keith Howell), who tire of demonstrating that physical security is the basis of any security. This time they will talk about impressionism - the art of creating a key to someone else's door using a blank, a flat file and close observation. All participants in the presentation will not only get acquainted with the features of the method, but will also be able to practice its application.
A brief description of all Hands-on Labs is available on the event website .
Search for answers

At PHDays, the most acute practical safety problems will be prepared, for the solution of which there are no ready-made recipes today.
So, the participants in the section “The Internet of Things - the Next Generation Threat?” Will focus on the dangers that the deep penetration of digital technologies into our lives can cause. How to predict these dangers? What tools should be used to minimize possible damage? Andrei Bosenko and Aleksey Kachalin (“Perspective Monitoring”), Andrei Moskvitin (Cisco), Andrei Petukhov (VMK Moscow State University), Artyom Chaykin (Positive Technologies) will try to answer these questions.
PHDays IV will be visited by French professor Eric Éric Filiol, cryptologist, expert in the field of cybersecurity and cyber warfare, winner of the Robertville Prize for the book "Computer viruses: theory, practice and application." He will present his view of the changes that have taken place in cryptography after the revelations of Edward Snowden and the scandals with RSA, Heartbleed, Google, ANSII, and will touch on a couple of topics that have not yet been written in the newspapers.
Specialists from around the world will consider promising approaches to detect and prevent intrusions (speaker - Robert Griffin from EMC), new dangers for telecom operators using the Orange network as an example (Sebastian Roche, security services of the core network in Orange Group). Other topics discussed include a comparison of the cyber potential of Iran, China and North Korea (it will be presented by William Hagestad) and problems of raising employee awareness about information security - Natalya Kukanova from Yandex will tell about them (according to Positive Technologies, on average more than 30 % of the employees of the largest companies follow phishing links!).
A description of the business reports planned for PHDays IV can be found on the forum website .
And now more about the new reports.
On the search for binary zero-day vulnerabilities in 2014
How to search, find and exploit zero-day vulnerabilities in statistically significant applications (OS, office applications, browsers) - 10 years after the release of Shellcoder's Handbook, after a million reports, thousands of application utilities and multiple multiplication of computing power? The speaker will try to answer this question by introducing his own fuzzing system, several zero-day vulnerabilities, and a number of protection bypass technologies.
The report will be presented by Alice Shevchenko (Esage), a computer security researcher. She has been managing her own company Esage Lab since 2009 and is a co-founder of the Moscow hackspace Neuron.
Cyber espionage: what are compromise indicators and what they eat
Speakers will talk about the concept of indicators of compromise (IOC) and its use in responding to and investigating incidents. The platform developed by the authors allows you to integrate various formats of indicators of compromise with the dynamic protection framework.
Speakers: Fedor Yarochkin - Analyst, P1 Security, Sinik Academy; Vladimir Kropotov and Vitaly Chetvertakov are independent researchers in the field of information security.
Visual analytics in information security
Infographics are called the new technological alphabet, and it is natural that specialists in the field of information technology are eyeing it, and not only for research design. The authors of the report developed visual tools for traffic analysis, attack modeling, security assessment, detection of financial irregularities in the mobile money transfer system. They argue that such an approach is much more effective than the traditional one, and they are ready to prove it in practice.
Igor Kotenko and Yevgeny Novikova, employees of the SPIIR laboratory, intend to demonstrate how visual analytics turns an ordinary "information security" into a computer Batman.
Time Attacks on SQL and NoSQL
The main area of application for such attacks is web applications. The study is devoted to various search algorithms for SQL and NoSQL databases and attacks by analyzing the execution time of such algorithms.
Speaker - Ivan Novikov, information security expert at the company and CEO of Wallarm. He was repeatedly awarded for detecting vulnerabilities in Google, Facebook, Twitter, Nokia, Yandex. At the moment, he is actively developing a self-learning WAF system.
Cyberthreats of control systems of a modern electrical substation
The author will talk about the full-fledged testing ground created in Cheboksary that imitates a modern high-voltage substation, and analyzes real cybersecurity incidents in the control systems of an electrical substation.
The results of the joint work of NTC FGC UES OJSC, Kaspersky Lab and TsUE CHEAZ LLC will be presented by Maxim Nikandrov, an expert in the field of power management systems, head of the control systems department of TsUE CHEAZ LLC.
Trusted channels and data conversion
Programmers become more competent and know that it is necessary to correctly process user data and not to give confidential data to unauthorized users. However, not everyone understands what is a channel for exchanging data with a user, and what is a trusted data source, and they only think at the level of their own code syntax. The report attempts to systematize deficiencies such as insufficient input validation (primarily in web applications).
Speaker - Omar Ganiev, expert at IncSecurity, a Russian company. Since 2011, he has been actively participating in CTF competitions, he has won many victories both in individual competitions under the pseudonym Beched and in team competitions (as part of the teams RDot.Org, UFOLogists, More Smoked Leet Chicken).
SAP Attack Vector - CUA System
The report will discuss the main areas of attacks on SAP, in particular on the centralized user management system SAP CUA. The author will show the vulnerabilities of CUA systems related to architectural features, incorrect configuration and default settings.
Speaker - Dmitry Gutsko, SAP Security Expert. Heads the security analysis group for SAP applications at Positive Technologies. He has published numerous vulnerabilities and studies on various SAP security topics.
Security modeling of access control and information flows based on DP models
The report is dedicated to security modeling of logical access control and information flows in modern computer systems. We consider the approach to security modeling based on the theory of DP models, its advantages and capabilities, as well as application features in the development of protection mechanisms. The basic elements, provisions and methods of DP models are described. New modeling approaches are proposed that focus on the software implementation of access control mechanisms.
Denis Kolegov - Ph.D., assistant professor of information security and cryptography at TSU, senior engineer for security testing at F5 Networks.
Reverse engineering automation
In the process of reverse engineering, many routine actions arise on the way of the researcher to understand what and how the program does. But there are a large number of technologies for increasing the level of abstraction of the presentation of programs and the automation of routine actions. The report will consider the advantages of these technologies, application examples and open utilities for their implementation.
Speaker: Anton Dorfman is a researcher, reverse engineer and fan of assembly language. Since 2009, the organizer and active playing coach of student CTF teams.
The announcement of the remaining reports can be found on the forum website .
Briefly and clearly
In addition to standard lectures, an extensive FastTrack is planned in the PHDays IV program, consisting of rich and dynamic fifteen-minute speeches, which we will briefly discuss below.

Analysis of the work of various anti-virus laboratories
A curious incident with the developers of the company helped to find out how the anti-virus laboratories actually work “on the other side” when analyzing suspicious software. Speakers will talk about how real attackers can detect antivirus laboratories' interest in their team servers in advance by analyzing incoming traffic.
The FastTrack express study will be presented by Igor Agievich, Deputy Head of the IT Department of Radio Monitoring Technologies, and Pavel Markov, software engineer at OJSC Radio Monitoring Technologies (St. Petersburg).
We catch shellcodes under ARM
Despite the abundance of shellcode detection tools, most of them are relevant only for the x86 platform. Speakers will attempt to make up for this shortcoming. The applicability of existing methods to ARM will be analyzed and possible heuristics for detecting shellcodes for this platform will be considered.
Svetlana Gayvoronskaya is a former member of the Bushwhackers CTF team, a member of the Microsoft Research project to automatically detect malicious tenants in cloud infrastructures. Ivan Petrov is an active member of the Bushwhackers CTF team. He is exploring the possibilities of exploiting ARM devices, writes modules for Metasploit.
Introspection of virtual machines, or How to track an attacker in the cloud
The speaker will talk about how “clouds” can help identify cybercriminals, and will also consider the approach used in the project to create trap systems (honeypots) and when taking into account the actions of an attacker or an insider in VirtualBox. Nazar Timoshik - software security engineer, penetration testing specialist, worked in various Ukrainian outsourcing companies (SoftServe, Eleks, Symphony-Solutions).
Axapt injection: attack on business data in Microsoft Dynamics AX
The speaker will explain how to take advantage of the three-tier architecture of Microsoft Dynamics AX ERP-system in order to get access to the domain administrator’s account of the system and data on the activities of the enterprise using X ++ language code.
Speaker: Dmitry Erusov for the past 10 years has been developing and implementing solutions based on the Axapta ERP system.
Techniques that make it difficult to detect and analyze malicious code in PHP scripts
The report describes the main methods that malicious code developers use to make it difficult to detect and analyze their scripts: multi-stage encryption, obfuscation, code hiding, "mimicry", hidden calls to PHP functions and others. For each method, examples are considered of methods for detecting with a scanner, the complexity of implementation, and detection. A list of decryption tools is provided.
Speaker - Grigory Zemskov, head of the company “Revision”, information security specialist. Author and developer of the AI-Bolit malware scanner. He worked as a senior developer at Tecom Group and a leading architect at Teleca Russia.
Crowd to pieces: Crowd filter like a panacea for DDoS
DDoS protection is a battle of resources. Crowdsourcing of resources to filter traffic and load balancing can help reduce the cost of fighting DDoS. The report will examine the concept of a defense system that makes distributed attacks known to be ineffective.
Denis Makrushin, an expert at Kaspersky Lab specializing in technologies for protecting against cyber threats, will talk about the technologies of “cloud” DDoS counteraction during his FastTrack speech.
Technical implementation of the integration of IT-GRC class systems and security and compliance control systems
The report discusses the implementation of the integration of the IT-GRC system and the security and compliance control system (CCMS) using built-in mechanisms. The article demonstrates the construction on the basis of the XSD-scheme of the report of the CPSS report of the reference XML report containing all possible elements and attributes from the reports of the CPSS report.
Marat Rakhimov graduated from NRU ITMO in 2013 with a degree in Organization and Technology of Information Protection. He works as a design engineer at Gazinformservice LLC. Certified Administrator of the RSA Archer GRC Platform.
There is nothing more permanent than temporary
Web developers or administrators often do not pay attention to temporary files and make configuration errors, so access to important information may not get the most welcome guests. The report will examine the main attack vectors that are possible due to the “footprints” of various popular programs and version control systems, and provide detailed statistics on such attacks.
The applicability of the ancient proverb to information security will be illustrated by Dmitry Bumov, security researcher and penetration testing specialist from OnSec.
How to get credentials without administrator privileges
An attacker usually cannot easily get the password from an account if he infected a computer with access to the organization’s internal network at the level of a regular user. Known methods require privilege escalation or a lot of luck. The author will present an original technique for exploiting vulnerabilities in the implementation of Windows SSPI, as well as a tool for using it to circumvent limitations.
Speaker - Anton Sapozhnikov, Senior Consultant, KPMG. Engaged in penetration testing for more than seven years, worked with many companies on the Fortune Global 500 list. CTF competitor in the More Smocked Leet Chicken team, which won and won prizes at events such as Codegate, HITB, DEFCON.
NFC: protocol security
NFC technology successfully penetrates most sectors of human activity - from paying for the metro to arranging a smart home. Conveniently. But is it safe? The report will consider the protocol for the interaction of NFC devices, the attack surface will be outlined and the threat model for NFC will be considered. An example is a MiTM attack on an Android phone using its own Arduino-based NFC transmitter.
The report will be presented by Andrey Plastunov (system analyst of the company “Perspective monitoring”) and Roman Bazhin (developer of the software “Perspective monitoring”).
All details about the FastTrack performances are on the forum site .
Technical reports and master classes are only part of a grand event that will take place in less than a month. An excitingcompetition program ; battlefield prepared for visitors to PHDays Everywhere sites; participants in CTF competitions identified ; finalists of the Young School competition for young scientists selected .
See you at Positive Hack Days IV!
