Guide to Mikrotik RoMON
Everyone had situations when it is necessary to configure remote equipment (sometimes new), and access is only available to other network devices, no PCs / laptops or users with phones. In the case of Mikrotik, this problem can be solved in two ways: the built-in RouterOS mac-telnet and RoMON. About them and will be discussed below.
Mac Telnet from the router
For those who have forgotten: Mac telnet runs on Layer2, so connection is possible within the same network segment.
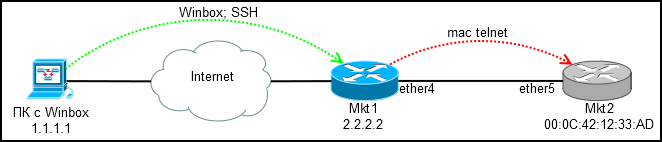
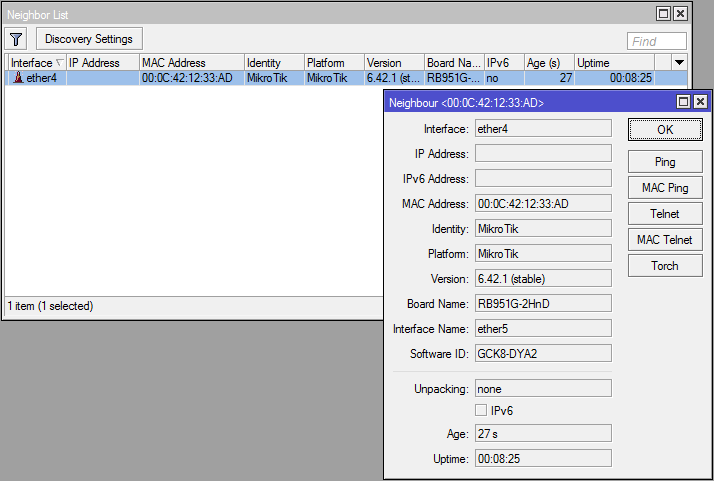
We connect via winbox or ssh to the configured router (Mkt1) and through it via mac-telnet to the new one (Mkt2).
Where to find mac-telnet:
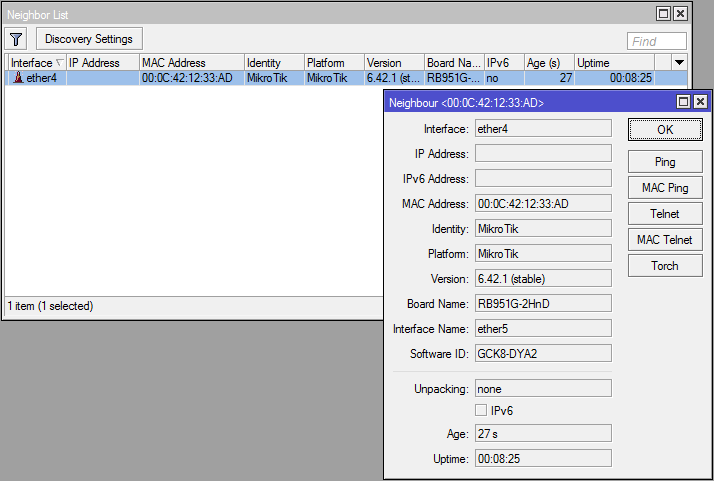
* [IP] -> [Neighbors] - if neighbor detection is enabled
* [IP] -> [ARP] - if there is any ip on the new router and it resolves to mac
* [Tools] -> [Telnet] - here besides mac-telnet there is a regular telnet and ssh
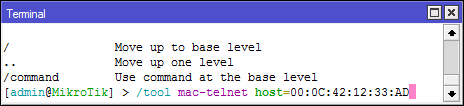
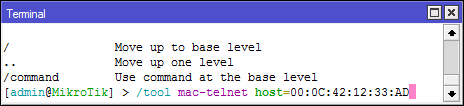
* / tool mac-telnet - from the console
What you should remember: if the device has a default configuration, then mac-telnet will be available only on lan ports (everything except ether1, usually), so clearly tell the installers where to connect the cable, otherwise no mac-telnet and RoMON will help you.
There is access, you can configure, but you want convenience? Especially when configuring queue trees and a large number of firewall rules.
Connecting via RoMON
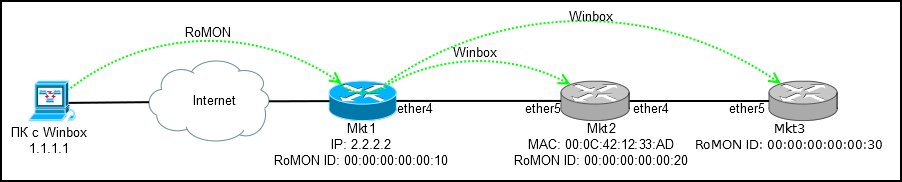
RoMON (Router Management Overlay Network) - Ability to use one mikrotik device to which there is ip access as a transit for connecting to the device via mac.
RoMON is disabled by default. The client part is built into winbox, so you do not need to install anything.
Setting on the transit router (Mkt1):
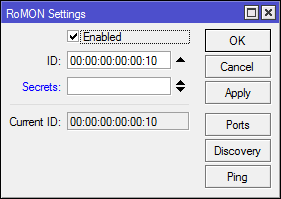
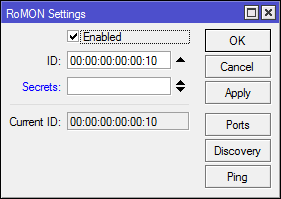
[Tools] -> [RoMON]
* Enabled - Enable RoMON
* ID - Manual RoMON ID setting, by default one of the router's mac addresses is selected
* Secrets - A set of passwords for RoMON authentication, used if The password on the port is not explicitly specified. The wiki details the password selection procedure.
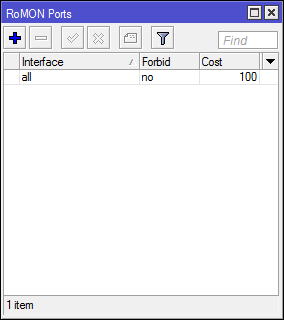
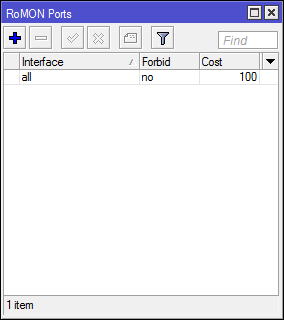
[Tools] -> [RoMON] -> [Ports]
By default, ALL ports are turned on, which is not particularly safe and it is not possible to disable all, so we set Forbid = yes on it , more precise rules for interfaces will block all.
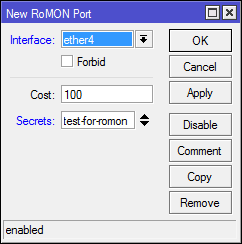
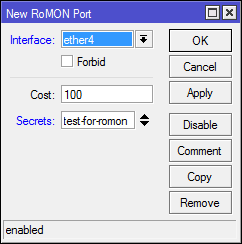
Create a rule for ether4:
* Interface - the port for which we are configuring
* Forbid - disable RoMON on the interface
* Cost - taken into account when building the path in large garlands
* Secrets - Set of passwords for authentication
Console option:
Setting up on a remote router (Mkt2):
Here we have a mac-telnet connection, so the settings will be console:
Now in [Tools] -> [RoMON] -> [Discovery] on Mkt1 we see a neighbor:
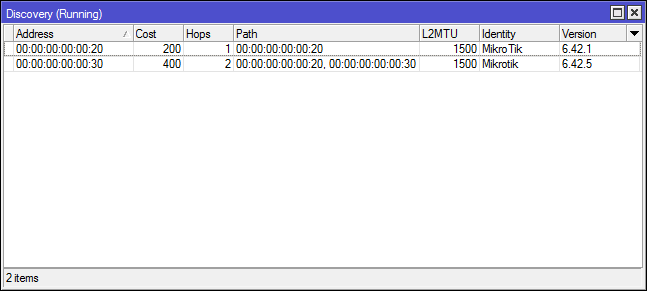
And another neighbor who is connected in transit through Mkt2, I leave the connection settings as an independent task, everything is similar.
Connection
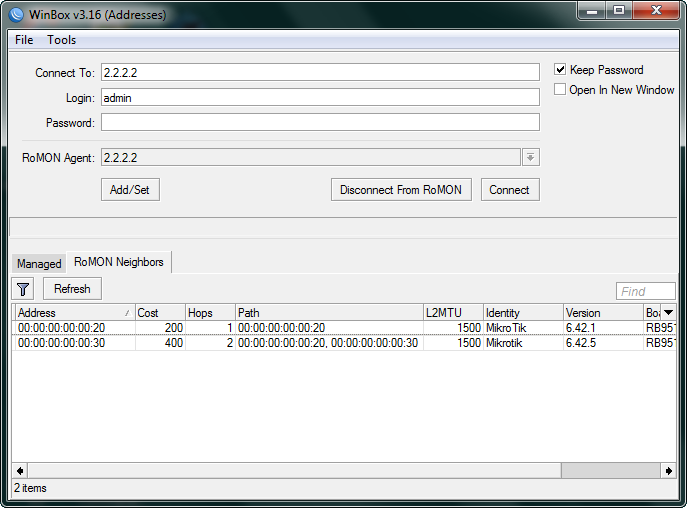
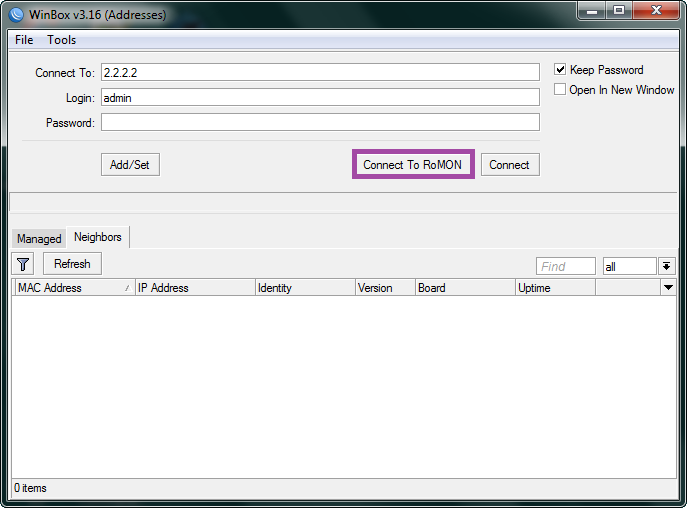
Launch Winbox and connect to 2.2.2.2 in RoMON mode using a regular account and password, secrets in RoMON refers only to the connection between routers:
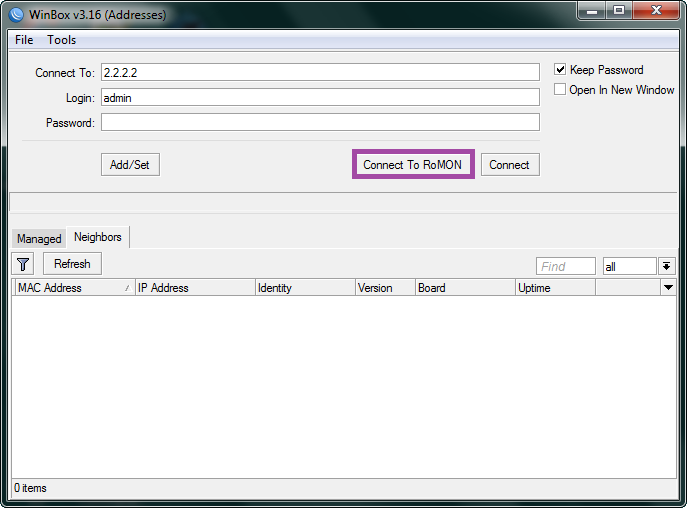
And here we see the most interesting thing - all routers in the RoMON chain are available for connection through a single transit Mikrotik.
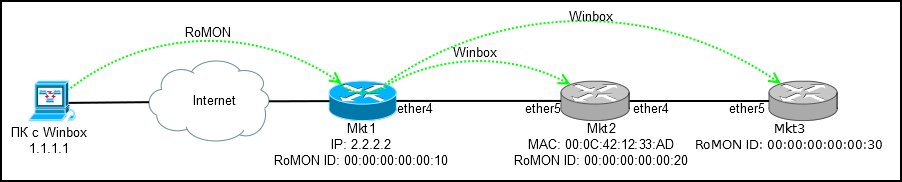
We select one of the addresses (RoMON ID) and connect to the router of interest.
Bottom line: We get transparent access to all routers in the chain, without the need for a consistent login via mac-telnet.
Additionally
[Tools] -> [RoMON] -> [Ping] - utility for ping routers by RoMON ID.
Regular mac-telnet is not a secure communication channel; if you have RoMON, you can establish an ssh connection using RoMON ID.
Connection via RoMON in command line mode (for shortcuts):
That's all. Functionality is not for everyday use, but it is useful to remember and know how to configure it.
Mac Telnet from the router
For those who have forgotten: Mac telnet runs on Layer2, so connection is possible within the same network segment.
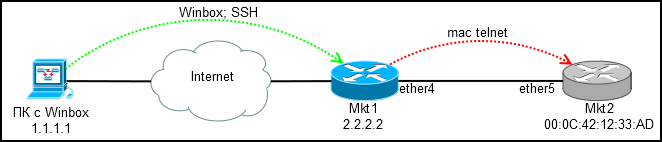
We connect via winbox or ssh to the configured router (Mkt1) and through it via mac-telnet to the new one (Mkt2).
Where to find mac-telnet:
* [IP] -> [Neighbors] - if neighbor detection is enabled
* [IP] -> [ARP] - if there is any ip on the new router and it resolves to mac
* [Tools] -> [Telnet] - here besides mac-telnet there is a regular telnet and ssh
* / tool mac-telnet - from the console
What you should remember: if the device has a default configuration, then mac-telnet will be available only on lan ports (everything except ether1, usually), so clearly tell the installers where to connect the cable, otherwise no mac-telnet and RoMON will help you.
There is access, you can configure, but you want convenience? Especially when configuring queue trees and a large number of firewall rules.
Connecting via RoMON
RoMON (Router Management Overlay Network) - Ability to use one mikrotik device to which there is ip access as a transit for connecting to the device via mac.
RoMON is disabled by default. The client part is built into winbox, so you do not need to install anything.
Setting on the transit router (Mkt1):
[Tools] -> [RoMON]
* Enabled - Enable RoMON
* ID - Manual RoMON ID setting, by default one of the router's mac addresses is selected
* Secrets - A set of passwords for RoMON authentication, used if The password on the port is not explicitly specified. The wiki details the password selection procedure.
[Tools] -> [RoMON] -> [Ports]
By default, ALL ports are turned on, which is not particularly safe and it is not possible to disable all, so we set Forbid = yes on it , more precise rules for interfaces will block all.
Create a rule for ether4:
* Interface - the port for which we are configuring
* Forbid - disable RoMON on the interface
* Cost - taken into account when building the path in large garlands
* Secrets - Set of passwords for authentication
Console option:
/tool romon
set enabled=yes id=00:00:00:00:00:10
/tool romon port
set [ find default=yes ] forbid=yes
add disabled=no interface=ether4 secrets=test-for-romon
Setting up on a remote router (Mkt2):
Here we have a mac-telnet connection, so the settings will be console:
/tool romon
set enabled=yes id=00:00:00:00:00:20
/tool romon port
set [ find default=yes ] forbid=yes
add disabled=no interface=ether5 secrets=test-for-romon
Now in [Tools] -> [RoMON] -> [Discovery] on Mkt1 we see a neighbor:
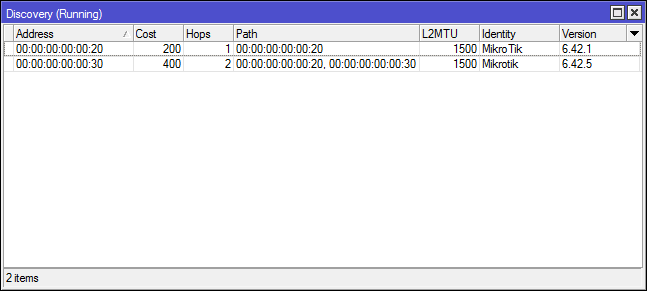
And another neighbor who is connected in transit through Mkt2, I leave the connection settings as an independent task, everything is similar.
Connection
Launch Winbox and connect to 2.2.2.2 in RoMON mode using a regular account and password, secrets in RoMON refers only to the connection between routers:
And here we see the most interesting thing - all routers in the RoMON chain are available for connection through a single transit Mikrotik.
We select one of the addresses (RoMON ID) and connect to the router of interest.
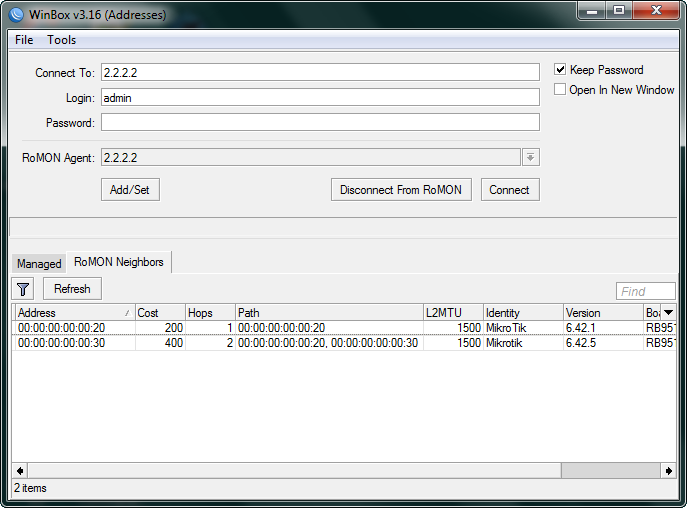
Bottom line: We get transparent access to all routers in the chain, without the need for a consistent login via mac-telnet.
Additionally
[Tools] -> [RoMON] -> [Ping] - utility for ping routers by RoMON ID.
Regular mac-telnet is not a secure communication channel; if you have RoMON, you can establish an ssh connection using RoMON ID.
/tool romon ssh Connection via RoMON in command line mode (for shortcuts):
winbox.exe --romon That's all. Functionality is not for everyday use, but it is useful to remember and know how to configure it.
