Wi-Fi features in Apple iOS and the impact on corporate networks
Without any introduction, I’ll say that there are a lot of devices on Apple iOS in corporate networks, and in the future there will be less of them (especially with such a massive popularization of BYOD ideology). It doesn’t matter whether they are used directly as business devices or simply as personal gadgets of employees and superiors. Therefore, you need to put up with them and somehow get along. In this note, the Wi-Fi features in Apple iOS are collected under one roof and links to materials for further study are provided. Let's take a look at what is and what is not in iOS, and how to live with it.
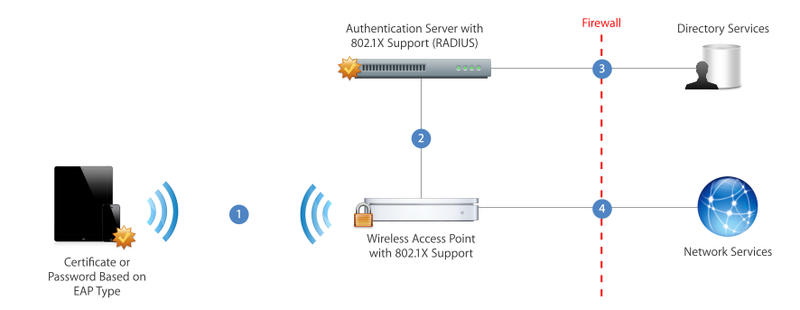
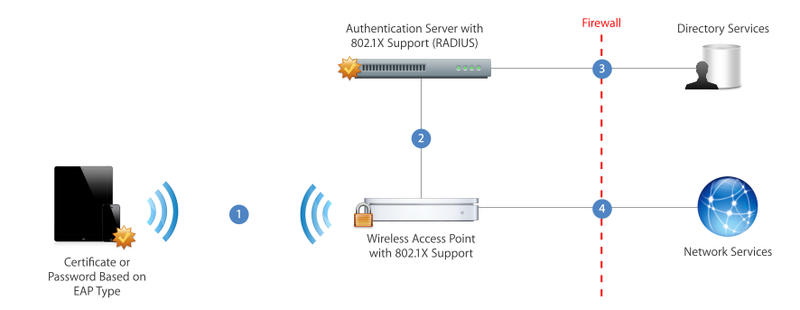
In general, in Apple's vision of i-devices on corporate networks, paradise, quietness and grace awaits. The paper on the deployment of iOS in corporate WLAN is provided with just one illustration. Apparently, you don’t need to know anything else.
Let's go in the reverse order.
But, as the author of several popular financial pyramids likes to say, this was all a hint ...
An article on the Apple support site “recommendations on setting up WiFi for iOS devices” reveals interesting details
An interesting note with a selection of impressions of Cisco TAC from iOS support
The Bonjour protocol (service announcement, AirPlay video transmission, etc.) is not routed. Those. devices must be in the same VLAN (which is normal at home). However, in a corporate environment, the chances of connecting a wired AppleTV and a wireless iPhone to one VLAN are minimal (if you have the right network design).
Whether you consider iOS suitable for the corporate environment or do not consider it - but somehow you have to live with it. Let's summarize everything in the form of recommendations for supporting iOS on a corporate wireless network
. Ideally, we want to give people access to the Internet and nothing more. If you need mail and so on - it’s much easier (from the point of view of Wi-Fi) to force all these devices to enter the corporate network via VPN thanto wreak havoc and destruction to change anything in a debugged Wi-Fi network.
If you plan to support enterprise applications in the corporate network - you should think
There is a wonderful NSA document for security . I think they can be trusted ( if this is not an intentional misinformation of a potential adversary ).
In conclusion, I note that Apple in terms of Wi-Fi has made a significant breakthrough. If the first firmware for the iPhone were so crooked that they completely mowed Cisco networks , now everything is much better. I still cannot call iOS devices “corporate”, but, in general, it is already possible to support iOS on a corporate network. To be careful of your appetites and promises. (This is not about managing the fleet of devices and BYOD in general!)
Share your opinions. Of particular interest is the experience of people supporting 50+ devices.
Good at first.
- All necessary (and unnecessary) encryption mechanisms are supported: WEP, TKIP, CCMP. At the same time, we remember that if we want 802.11n and high speeds on the network, then WEP and TKIP disappear, which Apple warns about on the support site.
- All basic authentication mechanisms are supported: EAP-TLS, EAP-TTLS, EAP-SIM, PEAPv0 (MSCHAP-v2), PEAPv1 (GTC), as well as proprietary Cisco LEAP and EAP-FAST.
- Of the certificates, PKCS # 1 (.cer, .crt, .der) and PKCS # 12 are supported
- Very user friendly 802.1x supplicant - no multi-level dialogs with obscure options - just enter your password, select / confirm the certificate and work.
- Thus, we have support for both WPA and WPA2 in Personal and Enterprise options and a wide range of options that the user can configure independently.
- Recent models support 802.11n and even 5GHz.
- In IOS6, there is support for 802.11k and 802.11r, which allow the device to determine the optimal access point when roaming (APs transmit data about their load) and quickly move to it.
In general, in Apple's vision of i-devices on corporate networks, paradise, quietness and grace awaits. The paper on the deployment of iOS in corporate WLAN is provided with just one illustration. Apparently, you don’t need to know anything else.
But it was not there.
Let's go in the reverse order.
- 802.11k and 802.11r (according to the aforementioned paper) are only supported on the iPhone 4S, iPhone / iTouch 5 and the new iPad - so for now, you don’t have to rely on them either.
- 5GHz is only supported on iPhone / Touch 5, iPad (1-4, mini) and Apple TV. However, much enthusiasm for the iPhone 5 is not visible, iTouch 5 is generally not clear who needs it (you can take a Mini for almost the same money), and the iPhone 4 / 4S still feels pretty good. Therefore, relying on 5GHz only for “total” support for i-gadgets will not work - you will have to work in 2.4GHz with all the ensuing consequences (3 channels, interference, heaps of neighbors, etc.).
- Friendly 802.1X supplicant allows you to safely accept someone else's unverified certificate.
- It is very convenient for labs and demonstrations, it is not very nice if someone gets on a fake access point ( MSCHAP is quietly opened further - namely, the vast majority uses it because of the prevalence of Active Directory - and the user name / password is mined).
- This feature is disabled through Configuration Manager, but for this you need to either hand over the phone to the IT-specialist, or send the profile to the user remotely and make sure that he has applied it.
- We’ll add about the “super speeds” 802.11n and MIMO in smartphones and tablets for the company. No Comments ( Amazon Blame )
But, as the author of several popular financial pyramids likes to say, this was all a hint ...
An article on the Apple support site “recommendations on setting up WiFi for iOS devices” reveals interesting details
- iOS doesn't like hidden network names. My iTouch 4G on IOS5 works quite quietly with a hidden network, but I heard complaints from others.
- Wide channels (40MHz) are not supported.
- On the one hand - well, that's right, there is nothing to stick with wide channels in 2.4GHz. They fit exactly one there, the interference from this in most cases is more than good. But why aren't 40MHz at 5GHz supported? The answer in the picture above is 20MHz, and so enough for the eyes.
- And what about the rest of the devices on the corporate network where wide channels are enabled (if you still use, say, iPads at 5GHz, as some fashion retailers do)? The only answer is to suffer. In parallel with HT Protection, 802.11n has a compatibility mode of 40MHz with 20MHz, which also reduces network performance in similar ways (preliminary frames, etc.). How much - depends on many parameters, mainly on how often the iPad will require broadcast - you can’t accurately predict.
- When connected to a Wi-Fi network, the device checks for an Internet connection while trying to connect to the Apple server and steal a specific web page from there. If this page is not available, it is assumed that we are sitting on a hotspot and a browser window pops up asking for a login, while the system no longer tries to crawl into the network. Conveniently. As a recent incident with IOS6 showed, in the absence of access to this page - there is no access to the network.
An interesting note with a selection of impressions of Cisco TAC from iOS support
- OKC support doesn’t really bother anyone if you don’t use soft-phones or if you have iOS6 devices (802.11r will successfully replace OKC).
- If there is no access to the Internet for more than 20 minutes, the device tries to reconnect or find another network (maybe it’s lucky there).
- TAC adds another stroke to the picture with hidden SSIDs - if there are two or more SSIDs, the device will always connect to open networks, even if you intentionally choose a profile with a hidden SSID.
- Devices (especially the iPad) have significant transmission power, but worse reception sensitivity (home-specific effects).
- A variety of jambs are possible when disabling the 11Mbps speed (which requires, in fact, enabling 802.11b support). I did not observe such problems on my iOS4 / 5 device, most likely these are remnants of older versions. However, some Motorola partners have confirmed that they have encountered this problem with customers.
- The article is dated July 2012, perhaps with the release of iOS6 some of the problems are gone. Unfortunately, Apple is not very generous with the details.
The Bonjour protocol (service announcement, AirPlay video transmission, etc.) is not routed. Those. devices must be in the same VLAN (which is normal at home). However, in a corporate environment, the chances of connecting a wired AppleTV and a wireless iPhone to one VLAN are minimal (if you have the right network design).
- However, the popularity of AppleTV has led many vendors to implement the so-called Bonjour Gateway is essentially an analogue of DHCP Relay, but for Bonjour, even now they are measured by its performance, showing diametrically opposite (these are two different links) results :). This feature is supported by Cisco, Aruba, Aerohive. Motorola does not support the Bonjour Gateway in its pure form - other L2 to L3 forwarding options are offered - from the proprietary MiNT to L2TPv2 / 3 and PBR.
- There are still little things (only 1 WEP key is supported, etc., devices do not connect to networks with WMM disabled ), but they really should not worry anyone, because non-similar configurations should not be used on corporate networks.
Total
Whether you consider iOS suitable for the corporate environment or do not consider it - but somehow you have to live with it. Let's summarize everything in the form of recommendations for supporting iOS on a corporate wireless network
. Ideally, we want to give people access to the Internet and nothing more. If you need mail and so on - it’s much easier (from the point of view of Wi-Fi) to force all these devices to enter the corporate network via VPN than
- In this case, it is enough to create a guest network, create an https hotspot on it with RADIUS authorization tied to the corporate user base (AD or another). I already wrote about the reasons for mandatory authentication on hotspots here .
- It’s enough to deploy a 2.4GHz network in total guest access mode for everything: b / g / n-speed support (of course, turn off the low speeds of 1,2,5.5Mbps if possible), 20MHz channels, unclosed SSID, etc. .
- A prerequisite for enabling access to an i-device should be the use of a security profile that blocks the ability to accept other people's certificates (protection against phishing and disclosure of corporate credentials).
If you plan to support enterprise applications in the corporate network - you should think
- Do we transmit synchronous traffic (voice, video)? Many schools in the US now use iPads to transmit instructional videos, for example.
- If not, we follow the recommendations of the previous paragraph, but instead of a hotspot we configure 802.1X, fortunately, there are a lot of options. Since the average user is frightened of the word "RADIUS" - it is much easier to convince him to apply a security profile by giving it complete with network settings ("click here and everything will configure itself").
- You may have to play a little with the speed settings on the network (if optimizations were carried out) and turn on some rates.
- Make sure that the page www.apple.com/library/test/success.html access from your network, or configure a redirect to your web server, which will convince iPhones that everything is in order. :)
- If you plan to transmit voice and video, everything becomes more complicated.
- Traditionally, such networks are built at 5GHz, because providing QoS in a "polluted" 2.4 is very problematic. The best way out is to state directly that the operation of streaming applications for iPhone4S and below is not guaranteed or supported, and then transfer iPads and other new devices to 5GHz.
- In this case, wide channels should be considered if they are used at 5GHz. Testing will help evaluate the performance drop caused by the appearance of iPads in such a network.
- For fast roaming (if required), it makes sense to upgrade users to iOS6 (there is a suspicion that 802.11k / r is a feature of the OS, not chipsets, though) and configure them in your wireless infrastructure. Otherwise, at least enable PMK Caching.
- If you plan to use Bonjour, we analyze traffic flows and do L2 forwarding on top of L3 (or enable and configure Bonjour Gateway). It is very good if you can do selective ACL forwarding in order not to send all the traffic, but it depends on the capabilities of your existing network equipment.
- We thoroughly test the behavior of devices of different generations and different firmware at different speeds. Typically, in high-performance WLANs, 18Mbps and lower rates are disabled. In this case, you will have to test which speeds can be disabled - and which ones to leave. Perhaps, coupled with special requirements for signal strength, this will entail changes in radio planning, for which you need to be prepared.
There is a wonderful NSA document for security . I think they can be trusted ( if this is not an intentional misinformation of a potential adversary ).
In conclusion, I note that Apple in terms of Wi-Fi has made a significant breakthrough. If the first firmware for the iPhone were so crooked that they completely mowed Cisco networks , now everything is much better. I still cannot call iOS devices “corporate”, but, in general, it is already possible to support iOS on a corporate network. To be careful of your appetites and promises. (This is not about managing the fleet of devices and BYOD in general!)
Share your opinions. Of particular interest is the experience of people supporting 50+ devices.
