Information security and catering: how managers think about IT products

Hi Habr! I am a person who consumes IT products through the App Store, Sberbank Online, Delivery Club and is related to the IT industry insofar as. In short, the specifics of my professional activity is to provide consulting services to catering enterprises on the optimization and development of business processes. Recently, a large number of orders began to come from owners of establishments, whose goal is to build an information security system at enterprises.
Let's start with a couple of fun stories. History number one. In one casual dining cafe, managers changed every three months. Once the very first manager, being a big fan of Soviet history, created the password “07111917” and indicated it on all the resources with which he at least somehow contacted on duty: the IIKO automated accounting program, access to the Plazius loyalty program, installation of systems security and fire safety. Once this manager was caught selling personal data of guests to competitors, and was safely dismissed. However, the revolutionary password "07111917" continued to live and was transferred from one manager to another. As a result, every waiter in the establishment knew how to connect to office Wi-Fi. Moreover, the guests also found out this password, because the waiters, out of kindness,

In catering, staff often use information security weaknesses for their own selfish purposes.
History number two. A handsome young man in a cornflower blue jacket meets with the executive director of a large restaurant holding. The following dialogue is conducted between them:
- Our company specializes in information products. Today I suggest you consider the possibility of acquiring a new generation password manager, Hawkeye [1]. It is unique in that it has a high degree of reliability, both for the cloud version and for the boxed version. Encryption is done using the AES-256 algorithm. In addition to the standard functions of any password manager, Hawkeye has advanced backups and security audits. What sayTwo of these stories relate to one problem - the low awareness of managers about the role and importance of information security in the life of enterprises. But there is an additional caveat. The way representatives of IT companies make their proposals also contributes little to understanding among managers why they need IT products. Over the years of my consulting practice, I have come to the firm belief that the HoReCa segment is a poorly developed market among suppliers of IT tools for implementing and maintaining information security principles. In this text, I would like to share a fragment of a small study that we conducted among the managers of public catering enterprises in order to determine the degree of their awareness regarding the implementation and application of IT products. Primarily, I want to focus on using password managers. I add that the study was dictated by the desire to better understand the thinking of managers in order to more effectively promote their consulting services.
- Konstantin, thanks for the information, but what is the difference between the boxed and cloud versions and why do I need all this?
Briefly about the methodology. A qualitative data strategy was chosen. We conducted twelve informal interviews with managers and their deputies in six catering establishments. The interview questionnaire had twenty questions that related to the general philosophy of information security, knowledge of the regulatory framework, work with personal data, technical capabilities of the security system at individual enterprises, used IT products, including working with password managers. All interviews were transcribed, the results were compiled in a generalized form.
Everyone was in a situation where he could not remember the password for his account
If you start with conceptual questions, then most respondents associate the information security of enterprises exclusively with the storage of personal data of their employees. Managers do not go into the details of the technical side of the issue. They care how much this or that software will effectively save time, help in the safe storage of data, and how much it will be convenient to use. Moreover, priorities are placed in this order: (1) - time - (2) - security - (3) - usability.
“Listen, I need to draw up time sheets, schedules, prepare reports to the owners. The restaurant is constantly breaking something. I sorely lack the time to tune the program settings, reinstalls. We are not an IT specialist in the state. If there is something quick and convenient, then you can try. ” (man, 41 years old)
“Information security here is limited by the fact that labor books are stored in a safe, and passport data is on that top shelf next to the accountant. This is all bad and I understand that. But configuring security wisely takes time, but now I don’t have it. We had experience in the institution purchasing an advanced antivirus, even bought a license. Any notifications constantly came, it was inconvenient, distracting from work ”(man, 35 years old)
“About six months ago, a seminar on the 152 Federal Law was organized for us in a business incubator. Then, and now, I have little that I understand in personal data. The main thing, and I told the owner about this, it is necessary to restore order in our personnel records. I, an accountant, have access to the data, as agreed with me, and that’s all. Now we have a mess here, of course ”(woman, 34 years old).As the results of the interview showed, in five out of six institutions there are no standards and procedures for ensuring information security, no responsible persons. Moreover, there is no full-time staff or outsourcing specialist who is involved in setting up and monitoring the security system. As one of the respondents said:
“We have a boy who adds information to the restaurant’s website. In theory, he could do all of this here ”(woman, 35 years old).The concern of managers about the safety of personal data is understandable. There are more and more cases involving administrative and criminal penalties ; requirements for inspections of personal data operators are changing . In the restaurant sector, this topic is becoming increasingly relevant, since in addition to internal access to accounts, most institutions have loyalty programs, where the number of residents goes to thousands.
In my opinion, now representatives of the IT industry have a good chance to gain access to a market where there is a clearly identified problem and the need for its solution. In the next three years, the request to build an information security system in the catering will only increase. Especially in the regions.
Nevertheless, with all the superficial understanding of how the information security system should be arranged, all respondents use password managers. Moreover, some oblige them to use their deputies, chefs and administrators. The first thing we asked the respondents is what password managers do you use in your enterprises:
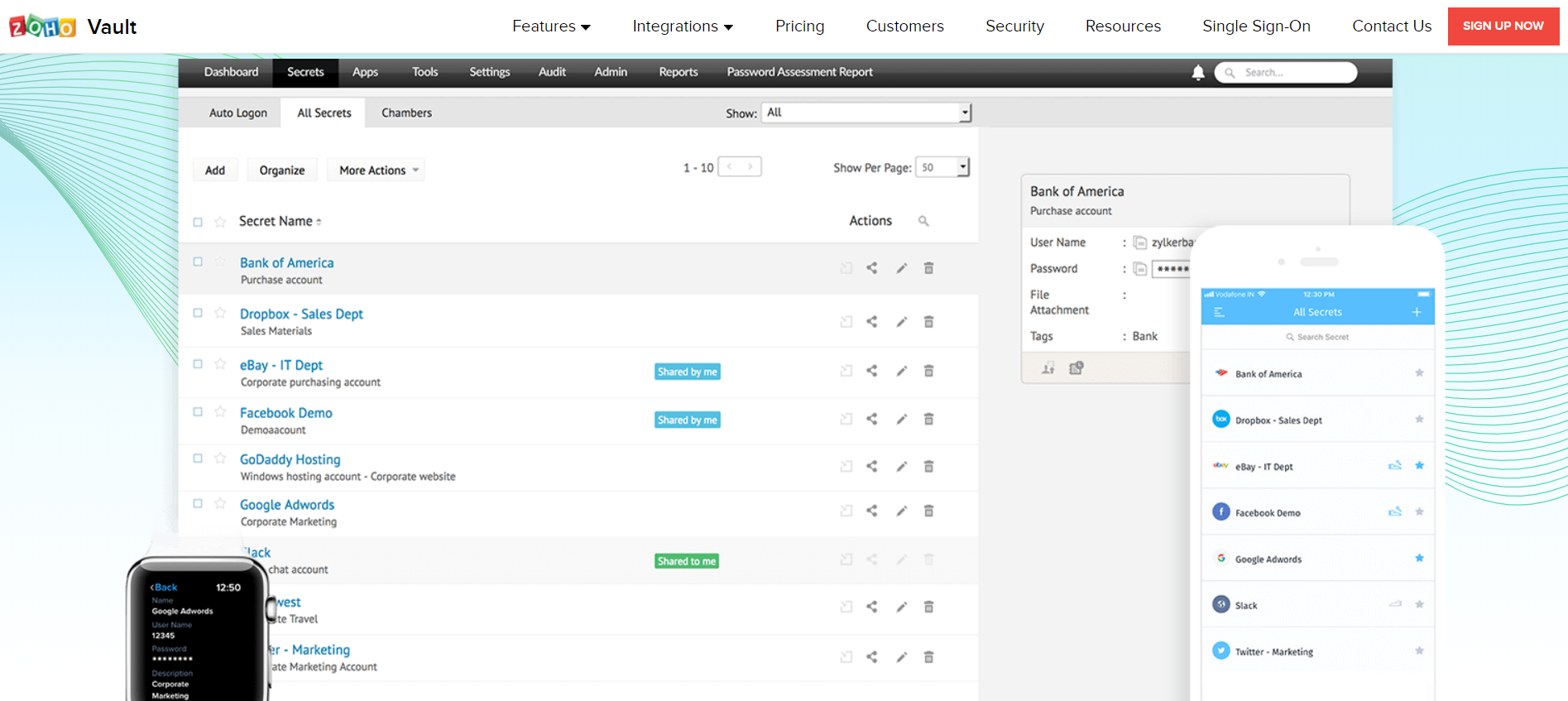
“I don’t know if I’ll say it right or not, but now I’m using Zoho [2]. Surprisingly, I can see the password even from the phone and from the work computer. The only thing I need to do is not forget the basic password for access. Therefore, I wrote it down in a diary ”(a 32-year-old woman).
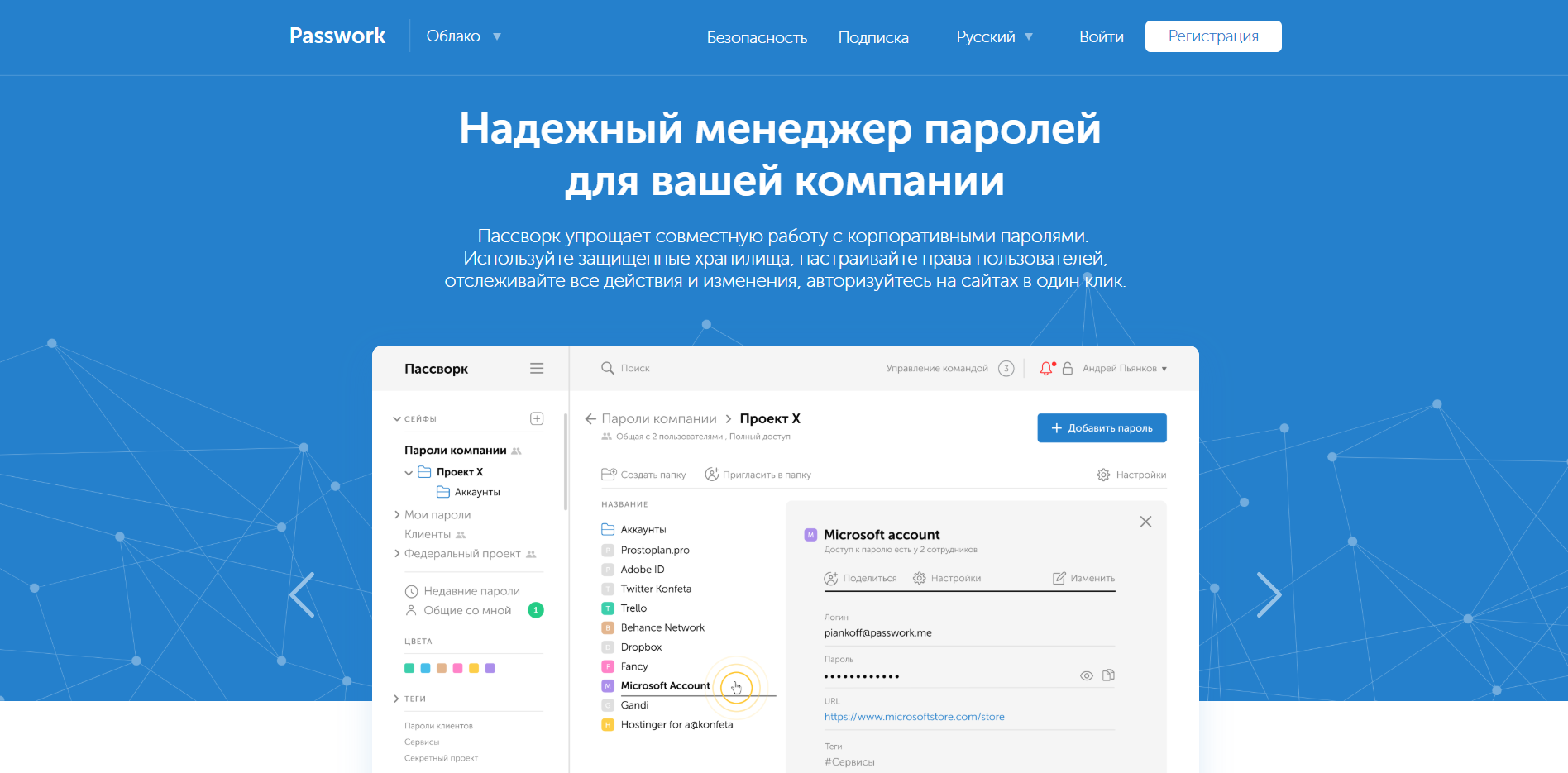
“Listen, I started using the password manager by accident. A friend at the university works at a bank and gave to use it. It is called Pasvork [3], it seems so far convenient, it saves time. We had a problem when the fired employee connected to the accounting system and looked at our revenue. It was completely by accident that they learned that the passwords in the restaurant were created by him. Urgently had to redo everything. So there was a need for a manager ”(man, 41 years old).
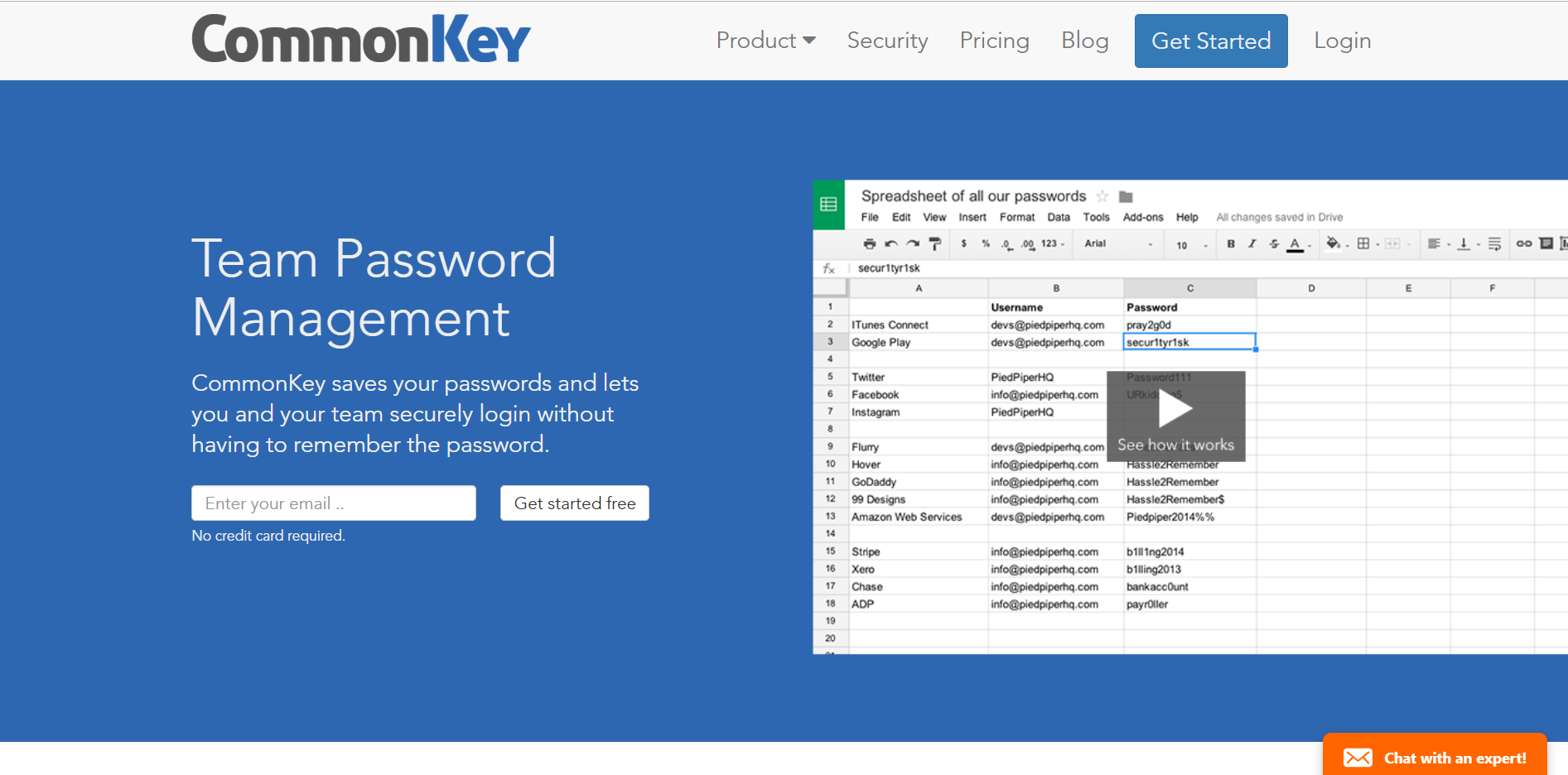
“I studied a little on IT in our technical. When I thought about the password manager, I settled on CommonKey [4], since it copes well with the function of administering personal profiles of employees. It’s very convenient for our pizzeria chain ”(man, 38 years old).
I note that I chose the most meaningful comments of the respondents. Most of the respondents could not remember exactly what their managers are called. For some, the password manager is exclusively associated with storing data on the browser. In general, respondents, when choosing a particular product, do not wonder about the cryptography mechanism that underlies the password manager. The priorities for them are speed and ease of use.
Despite the fact that among the respondents there is a common understanding of why they need a password manager, respondents use them from case to case. As the female respondent said:
“When on one side you are pulled by a banquet customer, on the other a supplier, and on the third the staff who asks when the salary will be, and at this time you create an account for a new employee, the only thing left is to write down the login and password on piece of paper ”(woman, 41 years old).However, there are certain practices. There are a number of problems that have made password managers used in the catering industry. What are these problems?
Firstly, access to loyalty programs. It is not a secret for insiders that the staff “muddies” with discounts, cashbacks are credited to plastic cards tied to relatives and friends of staff etc. The most effective way to prevent fraud is to regularly check the activity of accounts on the back of the loyalty program. The situation is complicated by the fact that at least three people need access to the program: a manager, a marketer (for SMS and push-messages) and an operator who maintains the loyalty program (in case of technical failures or additional options).
“The only thing when I try not to forget about the password manager is when working with our guest base. In addition to access to personal data of guests, virtual money can be credited or debited through this database. Once a month, I change the password, and do a ranking of accesses depending on the status of the user. Therefore, information must be constantly updated. Password Manager makes it easier to work in this regard ”(man, 48 years old).Secondly, at each enterprise there are magnetic cards of personnel for access to an automated accounting system (for example, IIKO or R-Keeper). There are entertaining cases. The waiter leaves and leaves with the card. In fact, the departed waiter knows the password for access to the system, where the financial indicators of the enterprise are reflected, dishes are deleted and written off, the working hours of the staff are recorded.
“There was a story when a laid-off employee conspired with a bartender and drank alcohol for hospitality. In some strange way, this comrade had an unblocked card and he used it ”(man, 38 years old)Thirdly, managers come and go, and accounts remain. The professional adaptation of the new manager slows down when he sits at the monitor screen and tries to reach the previous manager to find out the login and password from e-mail, Mercury and EGAIS systems, your personal account on the METRO company portal.
“I could not normally resolve issues when there was not a single access to existing accounts. The previous manager badly broke up with the owner and did not give me anything. I had to restore everything, sort through her drafts, persuade a person to share information. After that, I firmly decided for myself that I will keep all the passwords in a special program ”(woman, 29 years old).

Do not repeat the mistake of the President of Kosovo , use the password manager.
All of these situations can be useful to representatives of IT developers to formulate competent commercial offers to representatives of the restaurant sector. I emphasize once again that the HoReCa market is ready for the consumption of IT products. This applies not only to password managers, but also to antivirus software, video surveillance systems and business process optimization.
While writing the text, I realized the serious commercial prospects of implementing information security standards for restaurants, cafes and bars. Therefore, I ask all interested to write in the comments what kind of software you would recommend to HoReCa representatives to build a reliable information security system. At the end of the topic of password managers, please participate in the survey below. I would be very grateful for the detailed comments regarding your choice.
[1] The name is fictitious. Any similarities with other password managers are just similarities and nothing more.
[2] Respondent means password manager Zoho Vault: www.zoho.com/vault
[3] Respondent means password manager Passwork: passwork.ru
[4] Respondent refers to CommonKey password manager: www.commonkey.com
Only registered users can participate in the survey. Please come in.
Which password manager do you use in your companies?
- 0% CommonKey 0
- 23% Passwork 6
- 0% Vaultier 0
- 0% SimpliSafe 0
- 76.9% Other 20
