We crawl into the computer without using input tools, look for the Joker and connect to the server on Android - in the NeoQUEST-2014 tasks!

The NeoQUEST-2015 qualifying round will start very soon, and as a preparation for it, we are proposing to take together with us the tasks of the in-person NeoQUEST-2014 tour! We already told you how NeoQUEST 2014 went, shared the reports and photos (maybe someone even found themselves on them!). Now let's talk about that mysterious and hidden from the eyes of the audience, but the most important part of NeoQUEST - the competition of cybersecurity experts who turned out to be the best according to the results of the February online tour.
The confrontation for the participants included 5 tasks, but one of them failed. In this article, we will analyze four passed:
- "Am I Joker?" - We are engaged in competitive intelligence, using all the user information that we managed to get from social networks, go to a third-party site and exploit its vulnerability;
- “Unexpected find” - there is a computer and a flash drive, but there is no mouse or keyboard? It doesn’t matter, because the flash drive is not simple, but with SecureDrive, and the computer can identify one of its sections as a CD;
- “Don’t believe your eyes” - how to find a malicious program on a computer that hides its network activity, and at the same time files on a disk?
- “Frames decide everything” - we connect to a web server, which unexpectedly appears on a phone with Android OS, and form a special jar to get the key.
Before starting the analysis of tasks, let’s say about the most important - who nevertheless won the NeoQUEST-2014:
I place - AV1ct0r
II place - Dor1s
III place - Abr1k0s
AV1ct0r received the main prize - a trip to the international conference on information security, and the guys divided between themselves a LEGO robot and a 3D pen with a set of colored plastic.
By the way, many guests of the event also left with small but pleasant gifts won in competitions (more about this in the article on how the NeoQUEST-2014 full-time tour went).
Am I Joker? - task number 1
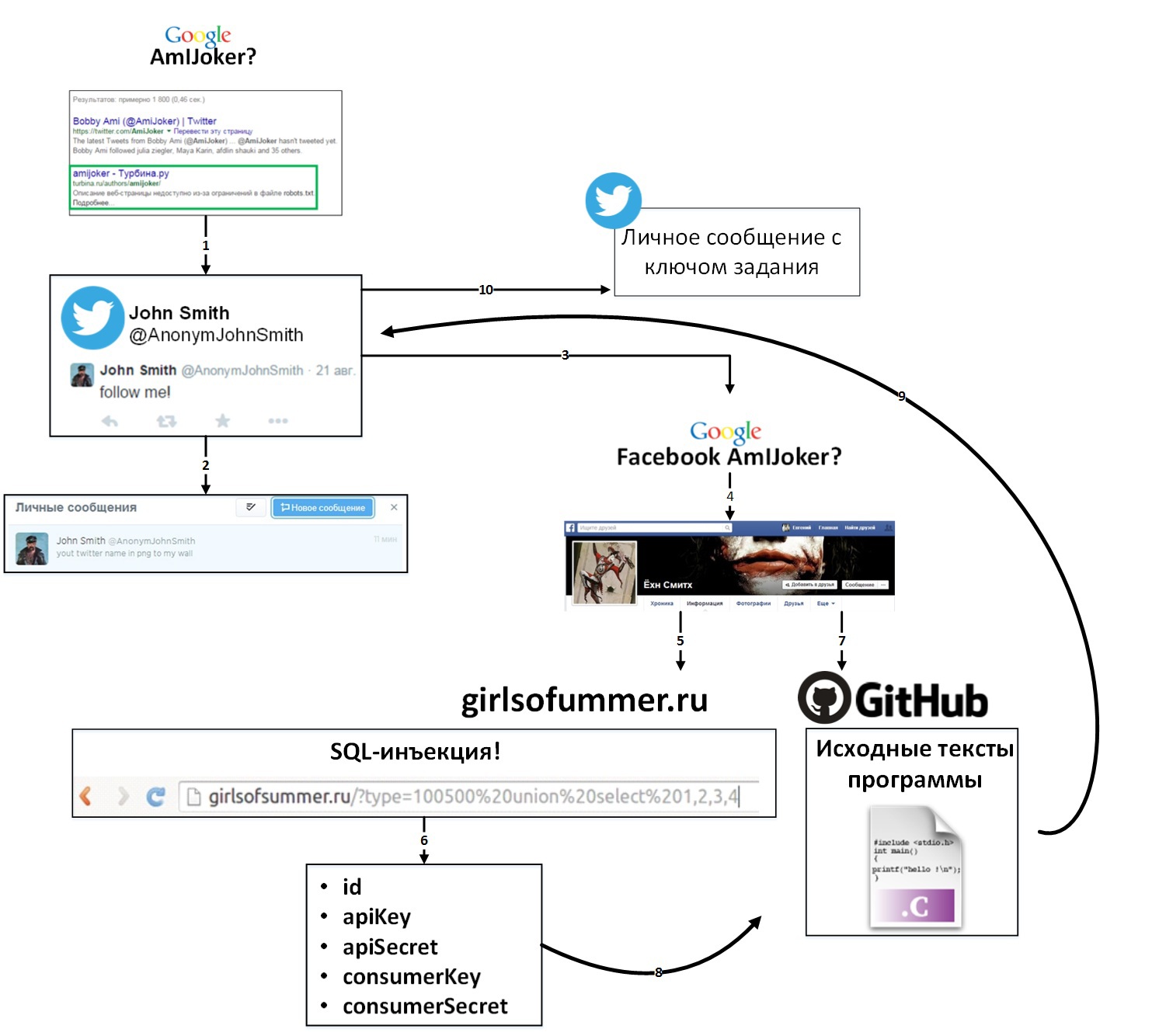
The entry point to the task was hidden in the title itself. The further passage of the task was divided into the following stages:
- A search for the phrase amijoker on google.com provided interesting information for participants:
- account of the same name on the site of the tourist community "Turbina"
- link to the user profile on the social network Facebook
- Getting useful information from an account on the Turbina website did not require registration from participants. Here is what participants could notice when they carefully looked at the AmIJoker user profile:
- John Smith Twitter Blog Link
- Twitter follow up call
- information that the user is working as a programmer
- If you go to the user's Twitter blog and subscribe to it, immediately after that, John Smith signed up for the member’s account and sent him a personal message with the following text: “your twitter name in png to my wall”. In this part of the assignment, participants had to guess that the name in png should be hidden using steganography. But not every algorithm will do. Of the ideas where to search for the desired algorithm, the most logical was the idea of searching in your Facebook account.
- Indeed, a link to the project posted on github.com is published on the account wall, and another link to github.com in personal information
- We go to github.com at the first link and look at the project. The program is written in PHP and works with the Twitter API. Using it, you could upload a photo, but there are not enough keys for the API and OAuth. This is where the second link to github.com comes in handy, we click on it.
- This repository contains a project written in C. It implements one of the simplest steganography algorithms. But how to get the keys to work with the Twitter API?
- Here the attentiveness of the participants was checked! In legend, it was not for nothing that the Aerosmith song “Girls Of Summer” was mentioned. After a short search, many found the site of summer girls. Also, the address of this site could be found in the general information of the account on Facebook. The site looks fresh in summer and pleasing to the eye!
- The site does not have any special functionality, however, an experienced eye may notice that switching between photos occurs by transferring GET parameters. One of the two parameters is vulnerable to sql injection. With this simple injection, participants could get the keys necessary to work with the twitter api:
- id 1
- apiKey 603445921-b8c9k8OMhalLS8FakTpDHoUuXIzKuHLabOPWspsR
- apiSecret O0DWIqmlNT02RKUZcXHIvkyMWG7Hwd9vKzAjd7JJ89Kbg
- consumerKey vlC5S1NCMHHg8mD1ghPRkA
- consumerSecret 3w4cIrHyI3IYUZW5O2ppcFXmsACDaENzFdLIKmEU84
Having received all the necessary tools, you just had to substitute the keys in the finished program and upload the picture to Twitter.
If the participant’s name was correctly written inside the png file, then in response to the picture he received a personal message with the job key.
In general, the task scheme looked something like this:
An unexpected find - quest number 2
All that was given to the participants was a computer without any input means and a Transcend flash drive with the SecureDrive function ... Only a monitor and a usb port were working on the computer, and the keyboard with the mouse did not function. The BIOS, by the way, was password-protected, so the participants had to get by with what they have. On assignment, participants needed to copy backup copies of sent mail from this computer and find a letter with a secret key.
In this situation, it is obvious that interaction with a computer is possible only with the help of startup programs from a flash drive. A simple check shows that autorun from removable media is disabled. Here you need to remember that autorun is possible not only from them, but also from CDs, as well as pay attention to the issued flash drive, namely SecureDrive. There is a section on the USB flash drive, which is defined by the computer as a CD, and on its other section there was just a special program, with the help of which the protected section of the flash drive was working! This should have led to the idea of using the section for your own purposes!
Such flash drives are quite widespread, and are often used as bootable ones, so it’s easy to find information on how to replace the contents of a virtual CD-ROM with your own. For this, a utility from the manufacturer, JetFlash Online Recovery , is used to restore the partition with SecureDrive in case of problems with the device. A study of the utility shows that the partition is created based on an ISO image stored separately from the executable file. In this case, no checks occur, as a result of which the required modification of the flash drive is achieved by replacing this image with a specially prepared one.
After being able to execute arbitrary commands on the target computer, you can begin to search for backups. The presence of the IIS shortcut on the desktop prompts the user to check the root of the C: \ drive for the presence of the corresponding folder:
dir C:\
The backup folder is also found there. Since the search for the desired letter without the possibility of using the keyboard can take a long time, the next step is to copy this folder to the second section of the flash drive. Before that, you need to determine the drive letter assigned to it in order to prepare the copy command:
xcopy C:\backup F:\backup /I /Q /Y
Copying takes a long time due to the number of files with letters. For the same reason, the required letter cannot be found manually. However, the quest legend gives a hint: the secret key was mailed on June 12! It remains only to automate the search process with a parameter, which is quite simple:
grep -l "12 Jun" * | sort -u | xargs grep -E "\<[a-f0-9]{32}\>"
Among the found lines, you can already manually find the desired key.
Don’t believe your eyes - task №3
In order to find the key, participants were given sheets with the NeoQUEST logo containing the word RDP, an IP address and a login password. The first logical thought is to try logging in via RDP to the specified computer ... and it works!
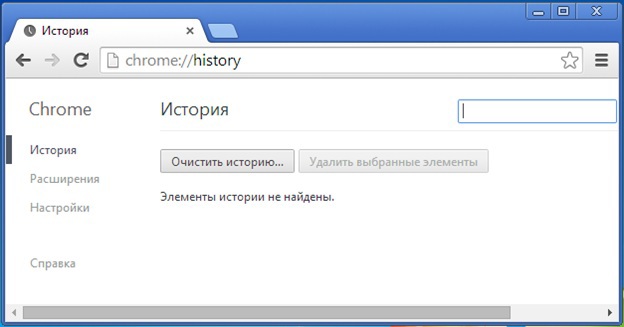
The task does not say anything about how to look for a key, which means that you have to act on a hunch. The computer’s desktop was empty, with the exception of three shortcuts with browsers that were clearly located there for a reason. When I try to start Google Chrome ... nothing happens. A normal browser window opens, you can go to any site, read the news, for example. When you start Mozilla Firefox - the situation is similar. Internet Explorer - all unchanged. It’s logical to try looking at browser-specific data: the history of visiting web pages, saved passwords, cookies, etc. ... But everything turns out to be futile - the history is cleared, there are no passwords.


Okay, if the browser “externally” functions as usual and has no clues, then perhaps the “internal” operation, invisible to the average user, has its own peculiarities. And the first feature to be discovered is that the browser periodically accesses the remote server, even though the open tabs are empty. Such actions are easily detected by the standard operating system application - Resource Monitor.

By installing the Wireshark sniffer and analyzing the outgoing traffic, the participants were able to detect the data stream to the 10.0.25.120 WEB server to the stub.php file. It might be interesting! But no, no matter how much you scan this IP address, no matter how much you break into this server - there is no result. And, looking ahead, indeed: the server is completely empty, there is no valuable information on it and it is used only to indicate that the participants are moving in the right direction.
The next feature is after a deeper analysis of the functioning of browser processes, namely, the resources they use. To do this, you can use both standard tools (Resource Monitor) and third-party (although this is still a question of how “third-party” you can call funds from Mr. Russinovich) Process Explorer and Process Monitor.
Process Explorer allows you to see the hierarchical display of processes, their properties, security settings, the resources that they have, and so on. But in a cursory scan, the processes of interest do not show anything interesting.
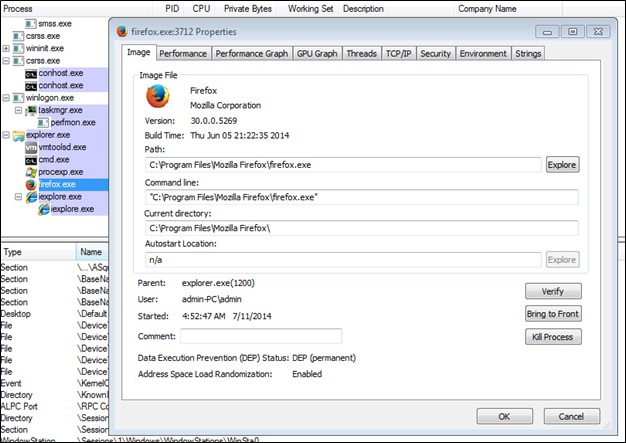
But after using Process Monitor, the answer to the task lies practically in the hands.
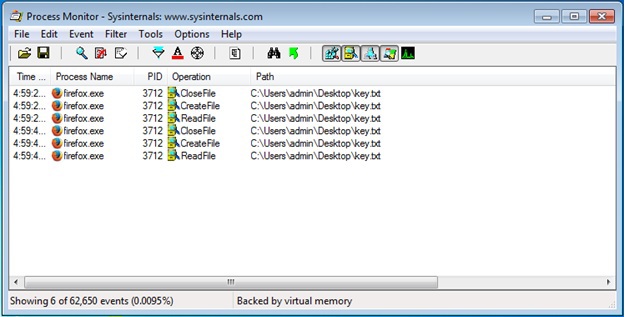
Process Monitor shows that the key.txt file, which is on the desktop, is periodically requested. Strange, but such a file is not there. How to be And here it’s worth remembering the old trick - the file may be hidden, but knowing the location, you can open it. A brilliant program allows you to do this (exhale!): Notepad.exe
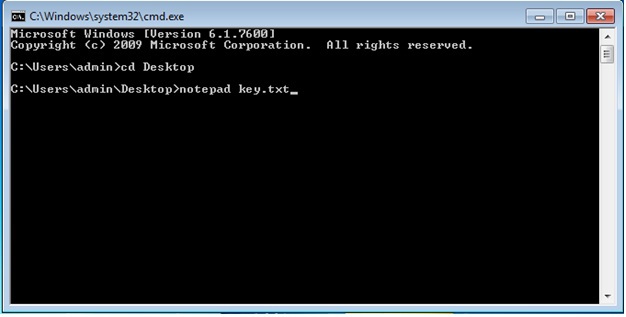
That's all. In the Notepad window that opens, there is a key necessary for the participant. Victory!

Now everything has become clear. There is malware on the computer that somehow embeds its code in all browsers, with the help of which it hides its network communication with the website. In addition, it also hides its files on disk, in particular, the file with the key to the task.
Cadres decide everything - task №4
In the legend, the participants were told that it was necessary to track the business contacts of one person: “Surely a lot of useful numbers are stored in the phone book” (excerpt from the legend) and an IP address was given by which you can access this book.
When switching to this IP through a browser, the user was prompted to upload a picture. If the user uploaded the jpg-file, then he was given a link to the edited image.
At first glance, this is a Web security task, but it is not at all. If you start picking a website, you can see some interesting things!
Firstly, using the Source Code Disclosure vulnerability, you can download the upload.php file by just writing something like 192.168.0.222 in the address bar of your browser: 8080 / upload.php or otherwise, by changing the case in the file extension. The source code for upload.php is:
Make your retro pattern
1024*1024)
{
echo ("Sorry bro ... your file is more then 1Mb...");
exit();
}
$valid_types = array("jpg", "jar");
$ext = substr($_FILES['filename']['name'], 1 + strrpos($_FILES['filename']['name'], "."));
if (!in_array($ext, $valid_types))
{
echo 'invalid file type';
exit();
}
if(copy($_FILES["filename"]["tmp_name"],
"/sdcard/pws/www/".$my_name."_".md5($_FILES["filename"]["name"].date_timestamp_get($date)).$_FILES["filename"]["name"]))
{
echo("success");
}
else
{
echo("error");
}
sleep(5);
echo("
Your file is here");
$url="/res/".$my_name."_".md5($_FILES["filename"]["name"].date_timestamp_get($date)).$_FILES["filename"]["name"];
echo("");
?>
What is interesting here? To begin with, we see that you can download not only jpg that is not interesting to us, but also a very interesting jar, apparently, this server can work with Java. Next we see the path “/ sdcard / pws / www /”, the word sdcard is very similar to the fact that the server is on the phone (although it’s still hard to believe!). And if you just take and search in Google this line, it becomes very similar to the fact that this is Palapa Web Server, raised on Android.
In addition, participants could find a very interesting information file by simply scanning the site with a scanner, for example, ArxScanSite, which determines the file structure of the site. This file is a picture below.
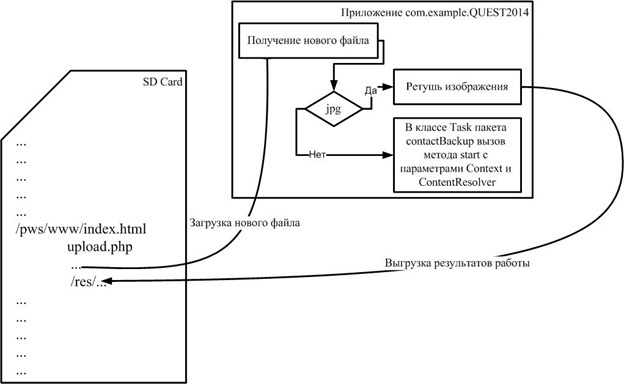
And after this, doubts that this is a telephone should not remain. It remains to connect Java + phone = Android and it turns out that we have a web server raised on an Android phone, although you can verify this once again by scanning it with Nmap.
So, what we have: we have a web server on Android, we know the path to the root of the server “/ sdcard / pws / www /”, we can upload jar files. And here the most important thing is to remember that in the task we were told “Surely a lot of useful numbers are stored in the phone book”, which means that according to the downloaded picture, we need to create a jar that writes all the phone numbers stored on the Android phone to a file on a memory card using the following path: "/ sdcard / pws / www /". Looking at the picture, it becomes clear that you need to create the com.example.QUEST2014.contactBackup package in which to create the start method, which receives the Context and ContentResolver and writes phone numbers to a file.
Next, you need to make this jar applicable for Android, there are several ways. The first path is performed in 4 stages:
- Exporting only our class to a jar file, after which we will get a regular jar file as a zip archive with a class file inside.
- Creating a dex file from our jar file using the jar2dex utility, you get the classes.dex file.
- Archiving the classes.dex file to a zip archive.
- Renaming the resulting zip archive to a jar file.
Another method involves 5 steps.
- Compilation of our application.
- Search in the directory where the Android SDK is located, the directory containing the dx.bat utility (for example, "android-sdk \ platforms \ android-3 \ tools").
- Create a directory with an arbitrary name in this directory, for example, “1”. Inside the directory “1” create a file structure similar to the structure of our application, i.e. "1 \ com \ example \ QUEST2014 \ contactBackup".
- Copying the contents of the "\ out \ production \ APPLICATION_NAME \ com \ example \ QUEST2014 \ contactBackup" directory to this directory.
- Call dx.bat with the following parameters - "dx --dex --no-strict --output = ctf.jar 1 /". As a result, we got the desired file - ctf.jar.
It would seem that everything was a victory, but there it was! When trying to load this jar, the site gives an error that convert.jar does not know such a file. Everything turns out to be very simple, if you look at index.html (the source code is given below). You may notice that a hidden tag is passed to upload.php called action and has the value “convert.jar”
Make your retro pattern Upload your image
Now you need to change the value to the name of the loaded jar-file and that’s it, voila! We get a list of contacts.
ID 190 Max NAME PHONE Smith +44234234234
ID 134 Max NAME PHONE Smith +4467652341
ID 137 Alex NAME PHONE Smith +4487653827
ID 193 NeoQuestKey NAME PHONE +78123123481
ID 4 Andrey Petrov NAME PHONE +79219325680
ID 11 Max Sushinskiy NAME PHONE +79843214982
ID NAME 13 Arkady Mamontov PHONE 000001
ID 1 NAME Test Test PHONE 1234567
ID 7 NAME Petr Ivanov PHONE 2359631
ID 119 NAME Ivan Zhukov PHONE 89215897894
It is clear that you need to take a NeoQuestKey phone and calculate hash from it. Well, that’s all, the flag is completed, the task is completed!
To be continued...
While the audience listened to reports on cybersecurity and received gifts by participating in fun contests, our heroic contestants very dynamically coped with tasks. Once again, we congratulate the winners and recall that the online stage of NeoQUEST-2015 is already approaching - with even more interesting tasks connected by a mysterious (as, indeed, always) legend! Stay tuned for updates on our website and blog Habrahabr.

