2.5F Authentication
- Tutorial
Hi Hi! Congratulations to all those involved on the day of Ibeshnik )
I want to share my experience in setting up 2.5 factor authentication of remote users. Why 2.5, I think, you will understand from the content, if you consider the model "1. What do I know. 2. What I have. 3. Who I am "reference. If interested, please!
I tried to draw something on the diagram:
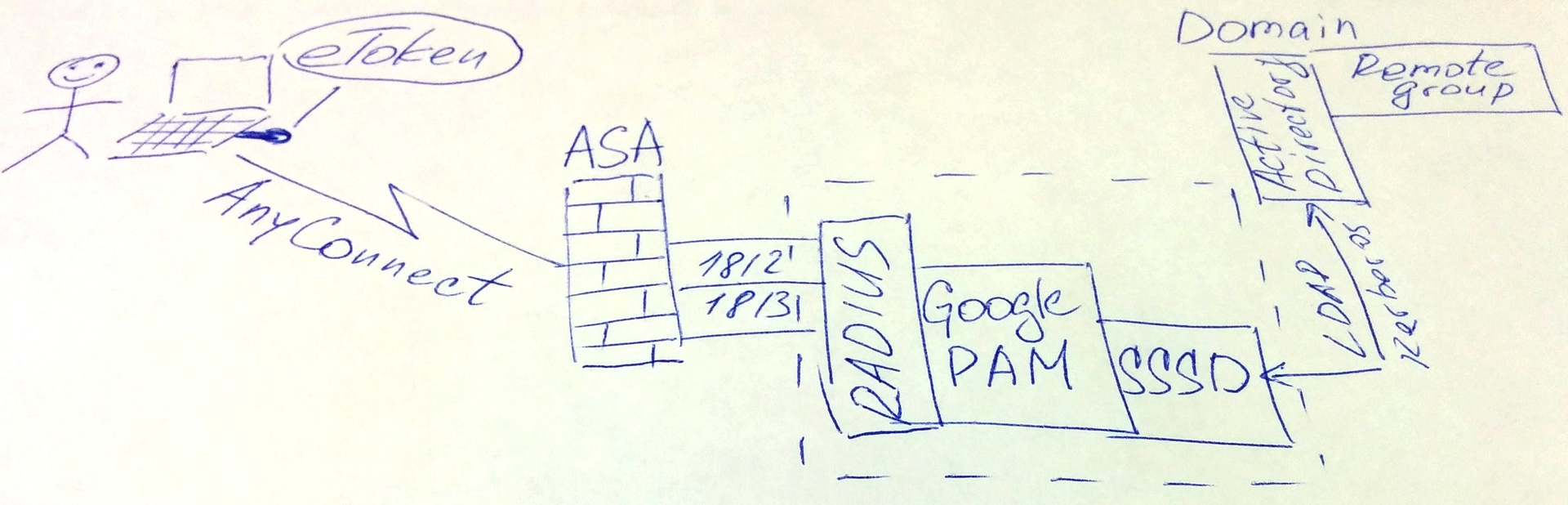
Briefly: the remote user has eToken (Alladin), an account in Active Directory that is part of a specific group, and a one-time password from the Google Authenticator mobile application. He needs to successfully connect to some service.
There is an article on Habré in which the main moments on setup of CISCO ASA, AnyConnect, Google Auth and Freeradius are described. I don’t see any sense in duplicating, everything is practically the same, except for the following.
I recommend installing the RADIUS server utilities for testing with the radtest command and radiusd -X debug
From the experience of the errors that appeared, it would be more convenient for me to configure in the following order:
But as usual, not everything is so simple and in order. On github, the Google components we need are here: “ The pluggable authentication module (PAM) is in a separate project. »During installation, various kinds of errors may occur, here you need to read and reinstall, if necessary, developer tools and libraries (gcc, libqrencode, etc.).
Now, what did not work out (maybe it did, but he decided not to write about it) from the author of the article cited above.
To use accounts from AD, you must install SSSD and components.
Next, add the RADIUS server to the domain:
We allow access to users from a predefined group in AD:
At this stage, there may be a problem with the domain name (.ru, .net, .test, etc.) Level 1 records may not be determined, so your domain name may be incomplete, this will affect the authentication process and the configuration of the RADIUS server.
In my case, it looked like username @ domain, where domain is only a level 2 name. What can it bring to? You simply cannot authenticate successfully unless you comment out the following lines in /etc/raddb/policy.d/filter
Otherwise, the data you entered will be filtered out as erroneous. In order to create a Google Authenticator domain user, do the following:
This user must be a member of the group that we indicated above with the realm permit command .
At this stage, problems also arise, security mechanisms will not allow creating a home directory for a new user. This directory is required for the ~ google-authenticator file , which contains information with verification codes and a key for each user.
To fix this, you need to transfer the SELinux component to permissive mode:
Next, go to /etc/pam.d/radiusd and write the following config:
Do not forget about NTP and synchronize the time, otherwise one-time passwords will not work, and in the file / var / log / secure there will be a message “invalid code”.
When everything is ready, you can test:
2.5 factor authentication is ready. If I forgot something and you did not start, write in the comments, I will try to help)
I want to share my experience in setting up 2.5 factor authentication of remote users. Why 2.5, I think, you will understand from the content, if you consider the model "1. What do I know. 2. What I have. 3. Who I am "reference. If interested, please!
I tried to draw something on the diagram:
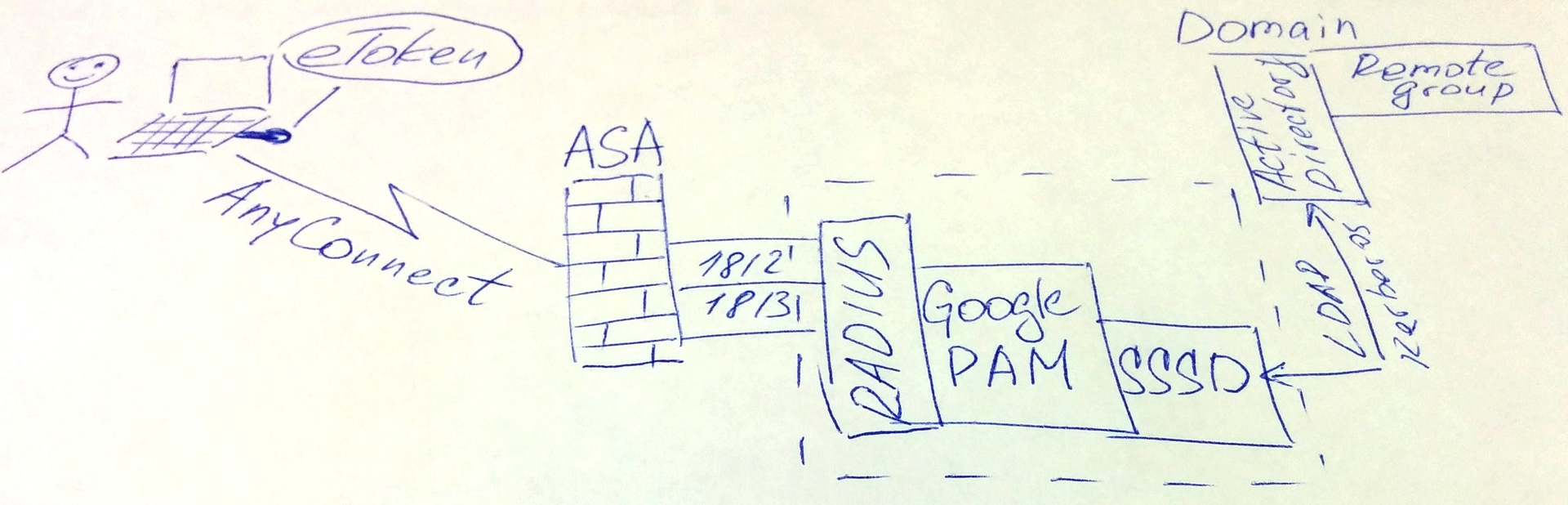
Briefly: the remote user has eToken (Alladin), an account in Active Directory that is part of a specific group, and a one-time password from the Google Authenticator mobile application. He needs to successfully connect to some service.
There is an article on Habré in which the main moments on setup of CISCO ASA, AnyConnect, Google Auth and Freeradius are described. I don’t see any sense in duplicating, everything is practically the same, except for the following.
I recommend installing the RADIUS server utilities for testing with the radtest command and radiusd -X debug
yum install freeradius freeradius-utilsFrom the experience of the errors that appeared, it would be more convenient for me to configure in the following order:
- RADIUS
- Sssd
- PAM
- CISCO
But as usual, not everything is so simple and in order. On github, the Google components we need are here: “ The pluggable authentication module (PAM) is in a separate project. »During installation, various kinds of errors may occur, here you need to read and reinstall, if necessary, developer tools and libraries (gcc, libqrencode, etc.).
Now, what did not work out (maybe it did, but he decided not to write about it) from the author of the article cited above.
To use accounts from AD, you must install SSSD and components.
yum install sssd realmd adcliNext, add the RADIUS server to the domain:
realm join ваш_доменWe allow access to users from a predefined group in AD:
realm permit -g ваша_группа_из_ADAt this stage, there may be a problem with the domain name (.ru, .net, .test, etc.) Level 1 records may not be determined, so your domain name may be incomplete, this will affect the authentication process and the configuration of the RADIUS server.
In my case, it looked like username @ domain, where domain is only a level 2 name. What can it bring to? You simply cannot authenticate successfully unless you comment out the following lines in /etc/raddb/policy.d/filter
# if ((&User-Name =~ /@/) && (&User-Name !~ /@(.+)\\.(.+)$/)) {# update reply {#Reply-Message += "Rejected: Realm does not have at least one dot separator"# }# reject# }Otherwise, the data you entered will be filtered out as erroneous. In order to create a Google Authenticator domain user, do the following:
su – domain_user@domain
google-authenticatorThis user must be a member of the group that we indicated above with the realm permit command .
At this stage, problems also arise, security mechanisms will not allow creating a home directory for a new user. This directory is required for the ~ google-authenticator file , which contains information with verification codes and a key for each user.
To fix this, you need to transfer the SELinux component to permissive mode:
setenforce permissiveNext, go to /etc/pam.d/radiusd and write the following config:
#%PAM-1.0
auth requisite pam_google_authenticator.so forward_pass
auth required pam_sss.so use_first_pass
account required pam_nologin.so
account include password-auth
session include password-authDo not forget about NTP and synchronize the time, otherwise one-time passwords will not work, and in the file / var / log / secure there will be a message “invalid code”.
When everything is ready, you can test:
- After starting AnyConnect, the eToken PKI Client window will appear.
- Choose your certificate. Enter the password for the container - 1 factor
- Next, enter the credentials of the AD user (login + password) - 2 factor
- Add the code from the application on the phone to the password (without spaces) - 0.5 factor
2.5 factor authentication is ready. If I forgot something and you did not start, write in the comments, I will try to help)
